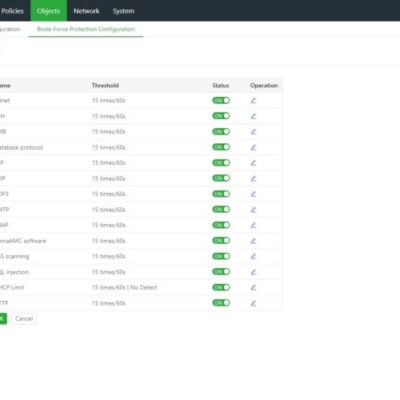
A brute-force attack involves systematically attempting every possible combination of letters, numbers, and symbols to discover a password. Websites requiring user authentication are susceptible to such attacks. Attackers may begin with dictionary words or slightly modified versions to expedite the process, exploiting common user password practices. These variations are known...
Year: 2024
AI Supply Chain Security: Hugging Face Malicious ML Models
Introduction to Hugging Face Malicious ML Models Background A recent report by JFrog researchers found that some machine learning models on Hugging Face may be used to attack the user environment. These malicious models will lead to code execution when loaded, providing the attacker with the ability to gain full...
NSFOCUS Research Labs Acknowledged by MSRC for Reporting Azure Database Service RCE Vulnerability
Overview NSFOCUS received acknowledgments from the Microsoft Security Response Center (MSRC) for reporting Azure Database Service RCE Vulnerability. Azure Database for PostgreSQL - Flexible Server is a relational database service based on the open-source PostgreSQL database engine. It is a fully managed database-as-a-service that can handle mission-critical workloads, offering predictable performance,...
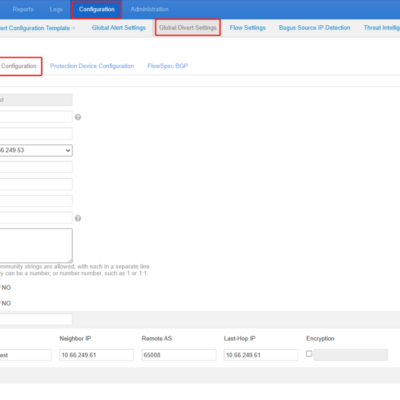
NTA BGP Configuration Example
NTA must establish iBGP neighborship with a router to implement null route or BGP diversion. Only in this way can NTA advertise route update notifications for the diversion of attack traffic to a third-party device for cleaning. BGP configuration module allows you to configure parameters for establishing a BGP session....
NSFGPT: A Large Model for Security Applications that Attracts Gartner’s Attention
NSFGPT is a large security model tailored for the security industry, based on the Security Large Language Model (SecLLM) as the core technology, and combining NSFOCUS’s 20 years of expertise in network security and 10 years of experience in AI security research and practice. It leverages a massive amount of...
NSFOCUS Innovative DDoS Protection Technology Secures Your Network Perimeter
Cybersecurity is crucial for national security in the digital world, where major powers clash over their interests. However, technology also enables more sophisticated and harmful network attacks. One of the most common and dangerous types of attacks is distributed denial-of-service (DDoS), which can hide, coordinate, and scale up to overwhelm...