Overview Recently, NSFOCUS CERT found that the open source message middleware ActiveMQ developed by the Apache Software Foundation had an XML external entity injection vulnerability. Since the port 61616 was opened by default after the installation of ActiveMQ was started, and the TcpTransport function did not perform necessary checks on...
Year: 2023
O que é computação em nuvem? Como funciona o cloud computing
A computação em nuvem está presente por todos os lados, mas você tem ideia do que isso significa? Neste artigo, vamos explorar mais sobre esse mundo, desvendar conceitos, funcionamento e os diferentes tipos de nuvem. Além disso, abordamos como a inteligência artificial impacta esse campo, como proteger os dados na...
Israeli-Palestinian Conflict: Multifaceted Alliances and Fierce Cyberspace Battle
Background On October 7th, accompanied by the launch of thousands of rockets, the Palestinian Islamic Resistance Movement (Hamas) declared a military operation against Israel. As real-world conflict escalated, hacktivist organizations from various countries, including Russia, India, Indonesia, and Iraq, began engaging in continuous cyber warfare within the cyberspace domains of...
GovWare 2023
GovWare, Oct 17-19, 2023, Sands Expo Convention Centre, Singapore. The conference & exhibition was held with the theme of “Fostering Trust Through Collaboration in the New Digital Realityâ€. NSFOCUS participated this pivotal event in APAC to introduce our latest effective continuous threat exposure management (CTEM) program and XDR-powered threat analysis and...
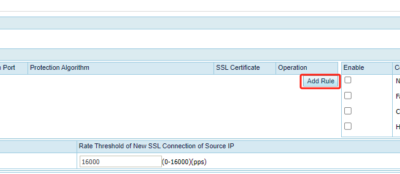
HTTP/2 Protection in ADS R90F03
Function Description For HTTPS application layer protection, ADS establishes a TLS connection with a client in replace of the server, and then authenticates the client through the application-layer protocol HTTP. If the client properly responds to the HTTP packet from ADS, ADS deems this client reliable and will add it...
NSFOCUS AISecOps: Elevating Your Security Operations Efficacy and Mitigating Alert Fatigue
In the realm of security operations, enterprises often face challenges such as a high volume of alerts, an inability to pinpoint real threats, insufficient security knowledge, and a lack of operational staff. While the operational platforms of major security firms exhibit similarities in functionality, some companies diligently analyze customer pain...