NIPS V5.6R10 has five types of rules to detect DDoS attacks, local privilege elevation, information gathering, suspicious network behaviors, and network monitoring events, respectively. They are described as follows. 1. Information gathering Information gathering is the first step of network intrusion. Attackers use various methods to scan and probe target...
Year: 2023
Relationship Between Security Concept and Security Assessment for Software Supply Chain
The three concepts, transparency of software supply chain, assessable capabilities of software supply chain security, and trusted software supply chain, are closely related to the ability of end users to conduct security checks and assessments for the software supply chain, including: 1. Basic assessment of software composition security Upstream and...
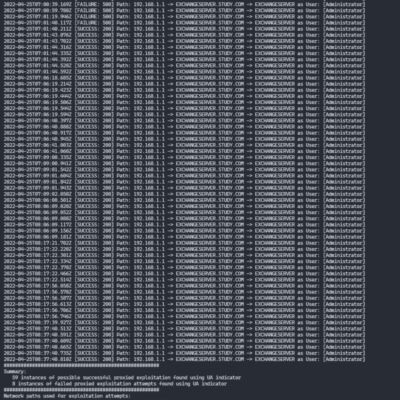
Exchange Server OWASSRF Vulnerability (CVE-2022-41080/CVE-2022-41082) Alert
Overview Recently, NSFOCUS CERT found that security teams overseas publicly disclosed the technical details of the exploit chain for Exchange Server vulnerabilities. An authenticated remote attacker exploits an Exchange Server privilege escalation vulnerability (CVE-2022-41080) to gain permission to execute PowerShell in the context of the system on an endpoint Outlook...