What is Zero Trust Security? Zero-trust security is not a specific technology or product, but a security model based on the concept that "All entities are untrusted". Forrester defines zero trust as “Zero Trust is an information security model that denies access to applications and data by default. Threat prevention...
Year: 2023
CDIC 2023
CDIC, Nov 29-30, 2023, BITEC Bangna, Thailand. The CDIC conference & exhibition was held with the theme of “Powering Techno-Drive in Digi-Hype Behaviour towards Digital Trustâ€. NSFOCUS participated this pivotal event as Gold Sponsor in APAC to introduce our latest effective continuous threat exposure management (CTEM) program and XDR-powered threat analysis and...
Prepare, Prevent, and Response: A Comprehensive Ransomware Protection Guide
Rampant Ransomware Attacks On November 8, 2023, U.S. Eastern Time, ICBC Financial Services (FS), the U.S. arm of China's largest bank, fell victim to a ransomware attack, disrupting certain systems. Reports indicate that the attack, linked to a Citrix vulnerability known as "CitrixBleed," was orchestrated by the LockBit group. ICBC...
Apache ActiveMQ Jolokia Remote Code Execution Vulnerability (CVE-2022-41678) Notification
Overview Recently, NSFOCUS CERT found a remote code execution vulnerability in Apache ActiveMQ Jolokia (CVE-2022-41678). In the configuration of ActiveMQ, jetty allows org.holokia.http.AgentServlet to process requests for/api/Jolokia. An authenticated attacker can send a specially crafted HTTP request to write a malicious file through the Jolokia service, thus implementing remote code...
O que é Phishing? Tipos e dicas para evitar golpes
O mundo digital está constantemente sob ameaça de um dos mais perigosos golpes cibernéticos: o phishing. Trata-se de uma técnica maliciosa utilizada por cibercriminosos para enganar usuários e obter informações pessoais e sensíveis. Vamos explorar o que é, como funciona e como se proteger desses ataques. Continue a leitura! O...
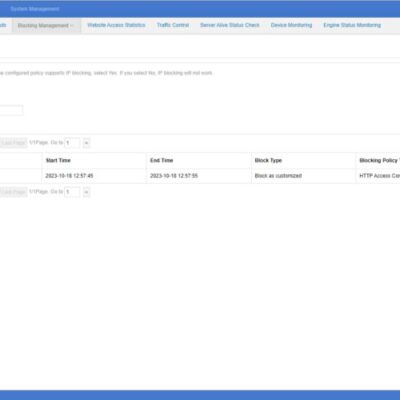
Introduction to NSFOCUS WAF Blocking Method
When you configure a protection policy for your protected website and set the protection action to block, NSFOCUS WAF supports three methods to execute blocking actions: Source IP Block, Session Block, and UA Block. Session Block and UA Block are newly added on system version 6073. Each block supports three...