Cross-Site Scripting (XSS) attacks are a type of injection in which malicious scripts are injected into otherwise benign and trusted websites. XSS attacks occur when an attacker uses a web application to send malicious code, generally in the form of a browser side script, to a different end user. Flaws that allow these attacks to succeed are quite widespread and occur anywhere a web application uses input from a user within the output it generates without validating or encoding it.
An attacker can use XSS to send a malicious script to an unsuspecting user. The end user’s browser has no way to know that the script should not be trusted, and will execute the script. Because it thinks the script came from a trusted source, the malicious script can access any cookies, session tokens, or other sensitive information retained by the browser and used with that site. These scripts can even rewrite the content of the HTML page.
Main types of XSS:
- Reflected XSS
- Stored XSS
- DOM Based XSS
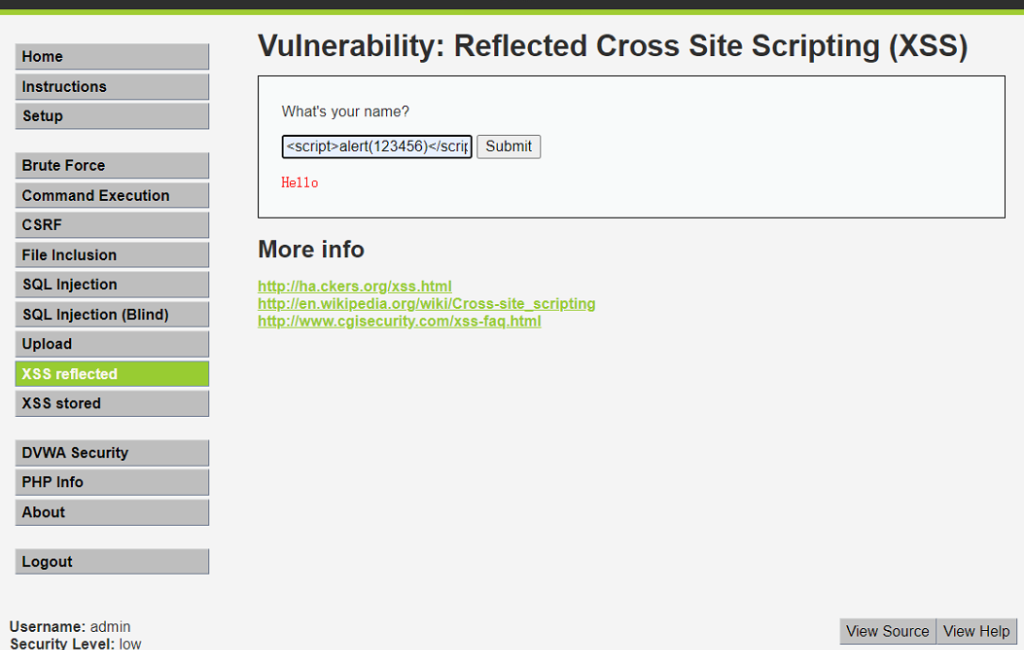
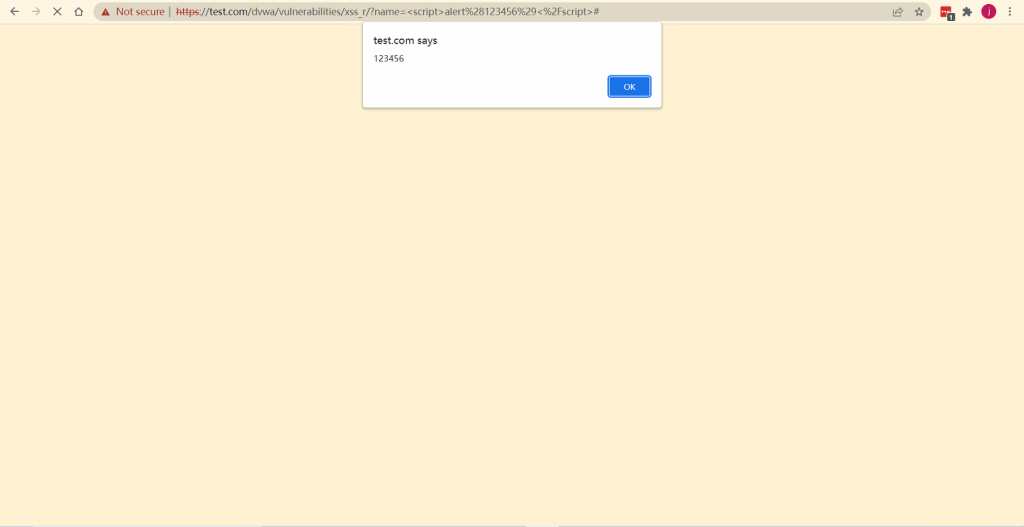
XSS demonstration by DVWA XSS reflected.
Insert malicious code into the input box, as shown below:
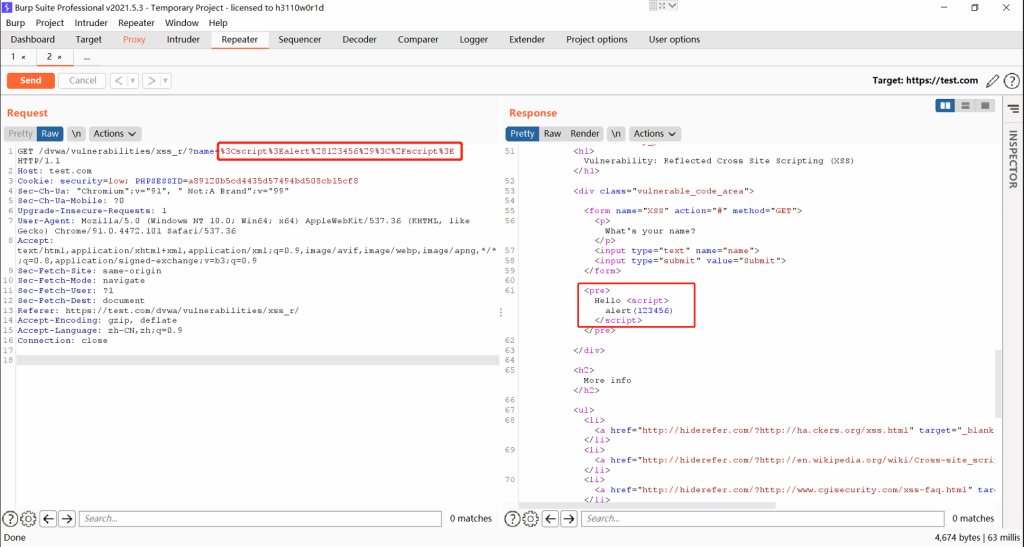
Use Burp to capture the request and response messages. Malicious code is embedded in the HTML source code of the response message.
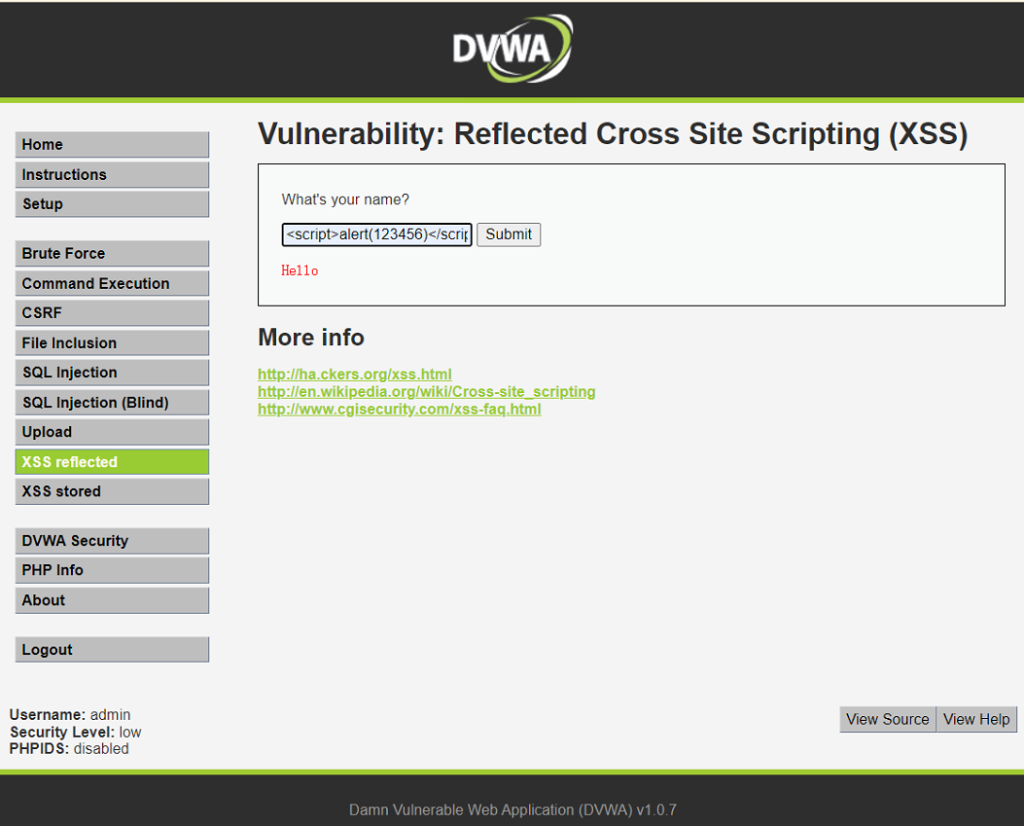
View the rendering result of the browser. The browser executes the malicious code.
NSFOCUS WAF can analyze malicious scripts in the request packets and defend against malicious XSS attacks.
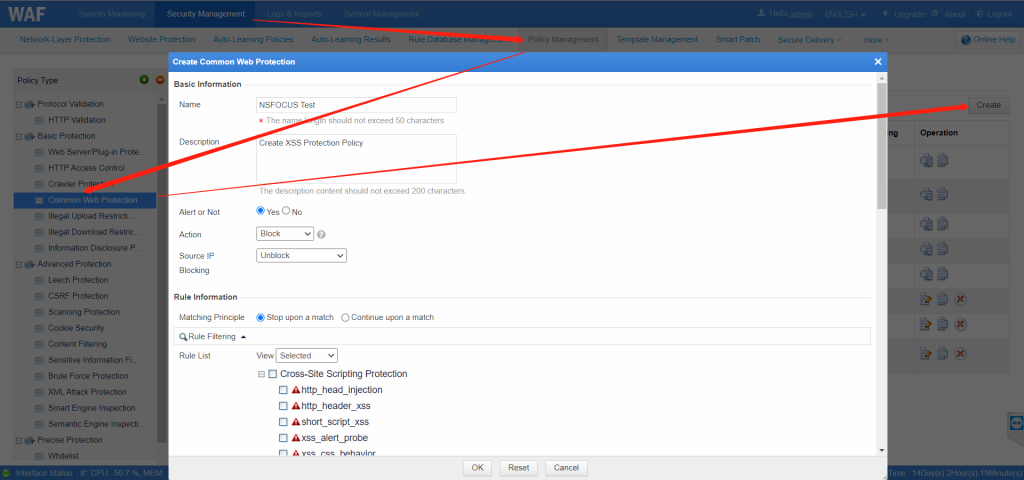
Configuration Steps:
Choose Security Management > Policy Management > Common Web Protection > Click Create in the upper right corner > Fill in or select Basic Information as required > Enable Cross-Site Scripting Protection on the Rule List > Select XSS algorithms as required.
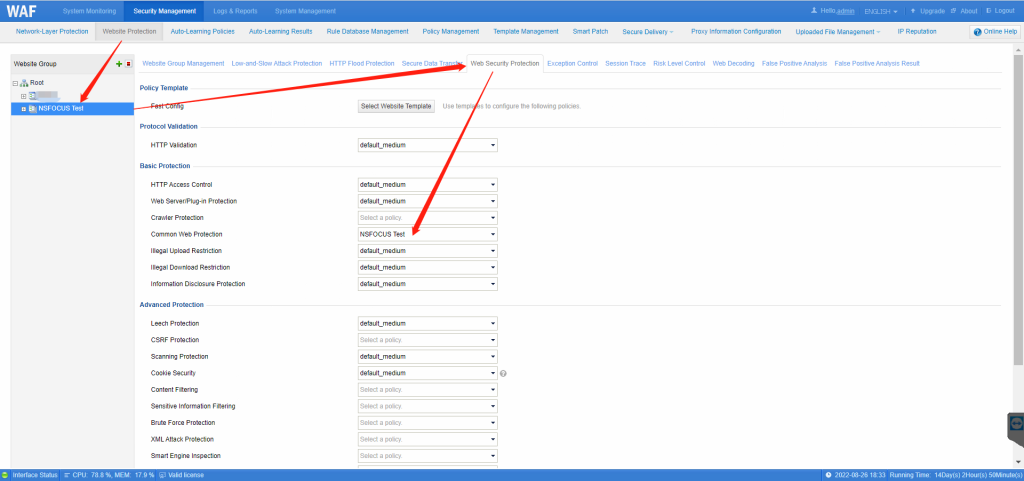
Enable the XSS protection for protected website:
Choose Security Management > Website Protection > Website Group > Web Security Protection > Common Web Protection > Choose the Policy created on last step > Click OK on the bottom.
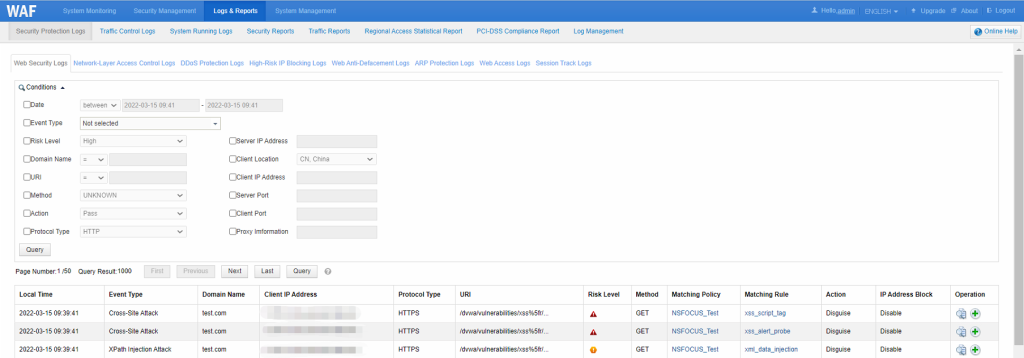
Check NSFOCUS WAF protection logs against DVWA XSS attacks:
Choose Logs & Reports > Security Protection Logs > Web Security Logs