Part 1: APT Group Gamaredon Intensifies Cyber Offensive in Ukraine (Part 1)
Type 2: Send malicious HTML attachments by masquerading notification emails
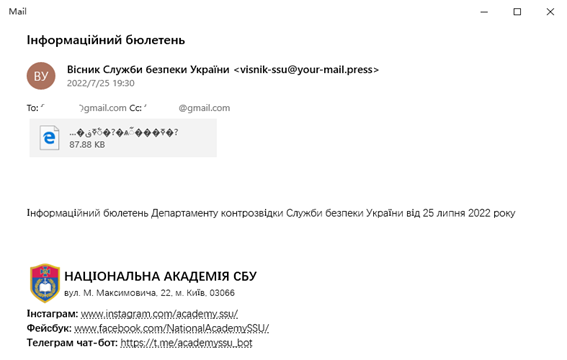
The second type of attack activity Gamaredon mainly carried out is spear phishing emails.
This is a new attack process that emerged in the second quarter of this year. Gamaredon attackers placed layers of malicious attachments in spear phishing emails and tricked victims into opening them with carefully constructed email content. This type of attack mainly targets Ukrainian military personnel.
Here we take a spear phishing email found on July 26 titled “Інформаційний бюлетень.eml” for example. In this email, Gamaredon disguises itself as the National Academy of the Security Service of Ukraine (Ðаціональна Ð°ÐºÐ°Ð´ÐµÐ¼Ñ–Ñ Ð¡Ð‘Ð£). It claimed that the email was “a security announcement of the counter-intelligence department of the Security Service of Ukraine on July 25, 2022”. The content of the email is deceptive, as the Security Service of Ukraine does undertake the work f anti-cyber espionage.
Figure 5 Type 2 – Decoy email
The email carries an attachment named “Інформаційний бюлетень_25.07.2022.htm”.The main function of the HTM file is to release a built-in compressed file and open it. The compressed file contains a malicious shortcut file named “Інформаційний бюлетень Департаменту контрозвідки Служби безпекту ійний бюлетень Департаменту контрозвідки Служби безпеки України від 25 Ð»Ð¸Ð¿Ð½Ñ 2022 року.lnk”.
The above malicious shortcut file will download a subsequent attack payload located at http://a0698649.xsph.ru/selection/headache.xml, and then run it. In similar attacks that have been captured, the subsequent attack payload is typically a powershell backdoor made by Gamaredon to steal information from the victim’s host.
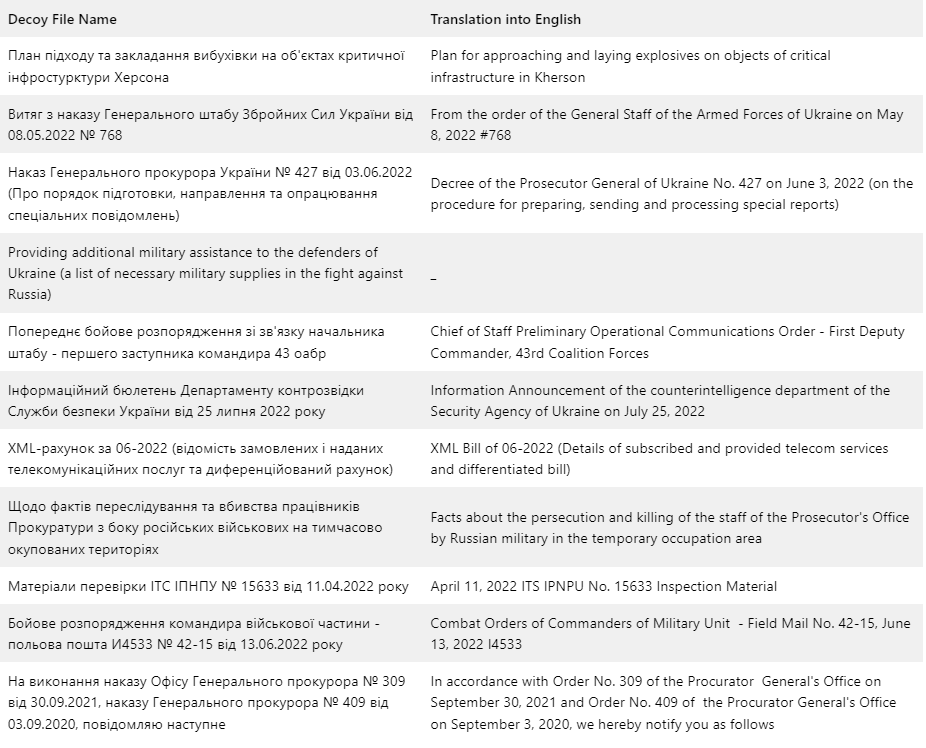
We counted the names of decoys appearing in such emails and found that most of them were related to key Ukrainian military intelligence, reflecting the Gamaredon attackers’ in-depth understanding of the Ukrainian military’s establishment, order numbers, document numbers, and other content.
Table 1 Statistics of decoy file names used in Type 2 attacks
Type 3: plant remote Trojans using SFX self-extracting files as baits
The third type of attack Gamaredon relies on is the SFX self-extracting file. This type of attack also targets the Ukrainian military.
This is an attack technique that has emerged in large numbers this year. Gamaredon combines a remote desktop tool called UltraVNC with the group’s commonly-used SFX decoy to control the target systems remotely.
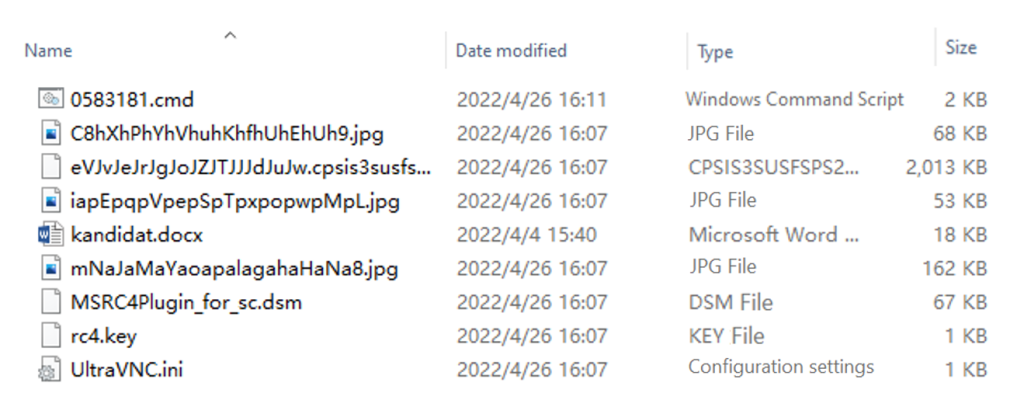
A typical SFX self-extracting file has a name like “Резюме кандидата на должноÑÑ‚ÑŒ ВПК.docx.exe_” Resume of the candidate for the military-industrial consortium position), using the extension to trick victims into running the file.
This type of self-extracting file contains several sub-files, including the UltraVNC remote desktop tool, the command file and ini configuration file for configuring the tool, and a decoy file.
Figure 6 Type 3 – Content of an SFX file
The C&C server of this UltraVNC in the relevant configuration file is licensecheckout[.] com.
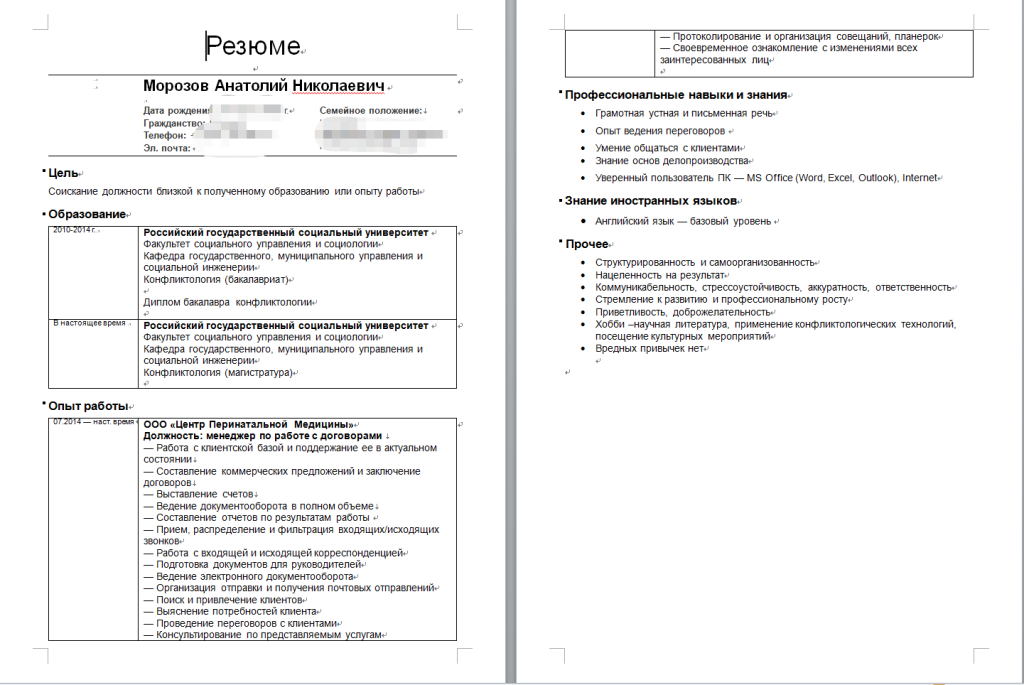
The decoy file named “kandidat.docx” shows a resume of a Russian.
Figure 7 Type 3 – A decoy document
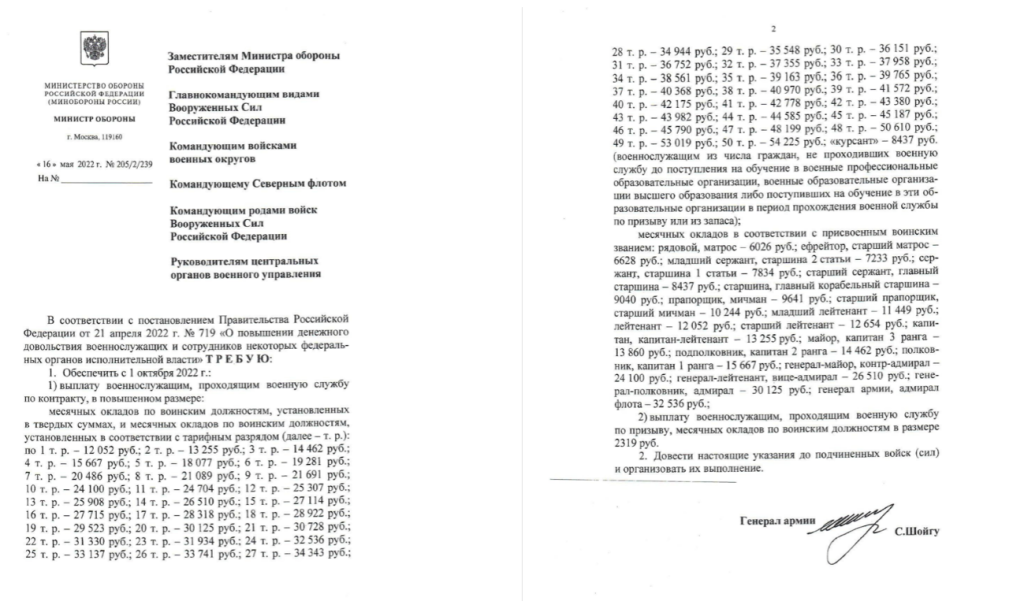
Most other similar documents contain military information, such as the Russian military pay adjustment document shown below.
Figure 8 Type 3 – Another decoy document
The decoy document demonstrates how the third type of attack differs from Gamaredon’s other attack activities. Among the similar samples we found, Gamaredon has added decoy files written in Russian, specifically containing sensitive information about the Russian government and military. It can be assumed that the direct targets of such attacks are Ukrainian organizations interested in such sensitive information, most likely including intelligence agencies such as the Security Service of Ukraine.
Summary
As the war situation entered a new phase, Russia and Ukraine launched a long-term tug-of-war in northern Kherson, northeastern Zaporozhye, western Donetsk, and northwestern Luhansk. The group Gamaredon also remained active in these regions, continuing to increase its cyber offensive against military, police, and other targets in these areas, with a clear spike in late July.
In the current round of cyberattacks, which began in the second quarter, Gamaredon has made a clear distinction between the various types of attacks, such as malicious office files mainly targeting police departments in Ukraine’s east, malicious shortcut attachments targeting the Ukrainian military, and malicious SFX files always carrying decoys on Russian military information, although there are occasional instances of exchanging the targets. This phenomenon suggests that there is a clear division of labor and a small amount of coordination within the Gamaredon group. The similarities between the above attacks lie in their carefully crafted decoy text messages, which demonstrate Gamaredon’s deep understanding of the Ukrainian environment and changes in the Ukrainian military. These elements probably came from the accumulation of Gamaredon’s long-term intelligence operations, and also present the strong social engineering and intelligence gathering capabilities.
Read more about the APT Group Gamaredon:
Russian APT Group Gamaredon Launches Phishing Campaign against Ukrainian Ministry of Foreign Affairs