The risk levels of API security events for NSFOCUS WAF version 6080 are categorized as follows: :Low Risk Events :Medium Risk Events :High Risk Events API Security Event Types: Event TypeDescriptionAbuseAttacks covered include JavaScript-related, account takeover, and CSRF.Sensitive Data ExposureAttacks covered include sensitive information leakage, anti-crawling, information leakage prevention, and...
Category: WAF
NSFOCUS WAF API Security Overview
NSFOCUS WAF v.6080 provides protection for third-party API assets. The API security protection features assist clients in refining their inventory of API assets through a combination of proactive and reactive strategies. By integrating automatically generated API baselines and imported OAS files, NSFOCUS WAF conducts API compliance checks. NSFOCUS WAF supports...
NSFOCUS WAF Security Reports
NSFOCUS WAF security reports are divided into classification-specific alert reports and period-specific alert reports. You can acquire reports based on query conditions, such as websites, event types, statistic collection periods, and statistic collection time. 1. Generation procedure: Logs & Reports > Security Reports > Classification-Specific Alert Report or Period-Specific Alert...
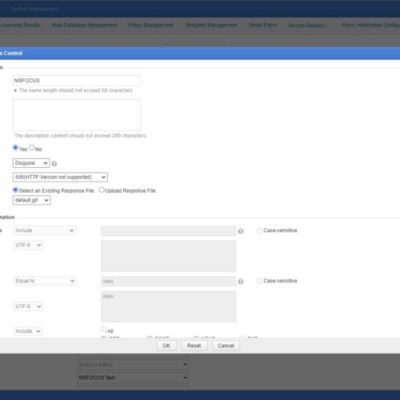
NSFOCUS WAF Disguised Response File Management
For a specific protection policy, NSFOCUS WAF can configure five actions. For more details, please view NSFOCUS WAF Protection Actions. When configuring a policy with Action set to Disguise, you need to select an existing disguised response file or upload a new one. Such files, whether existing or newly uploaded,...
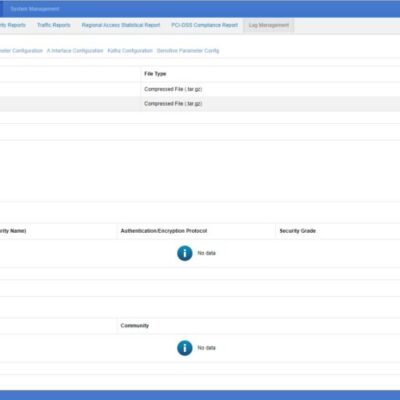
Introduction to NSFOCUS WAF SNMP
Simple Network Management Protocol (SNMP) is an application-layer protocol that transmits management data between network devices. SNMP belongs to the Transmission Control Protocol/Internet Protocol (TCP/IP) family and is one of the most widely used network protocols for managing and monitoring network components across a variety of industries. The majority of...
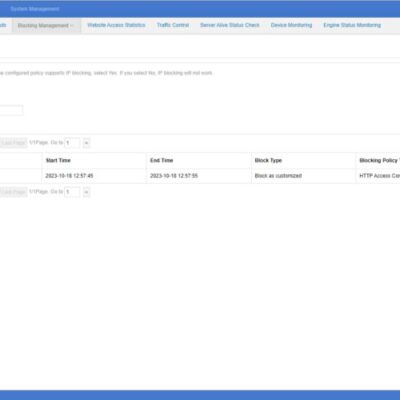
Introduction to NSFOCUS WAF Blocking Method
When you configure a protection policy for your protected website and set the protection action to block, NSFOCUS WAF supports three methods to execute blocking actions: Source IP Block, Session Block, and UA Block. Session Block and UA Block are newly added on system version 6073. Each block supports three...