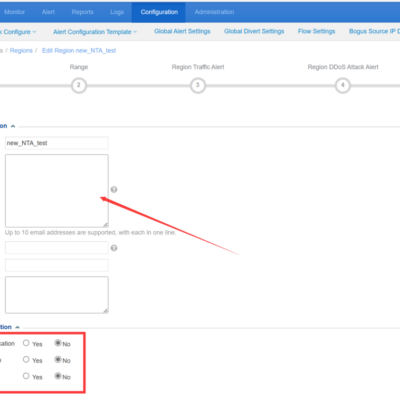
There are two separate email configurations on NTA which do not affect each other. One is the region/IP group email alert, the other is the global email alert. 1. Region/IP Group Email Alert Configuration -> Objects -> Regions -> Edit Corresponding Region/IP Group Email addresses configured on the Region ->...
Tag: DDoS attack
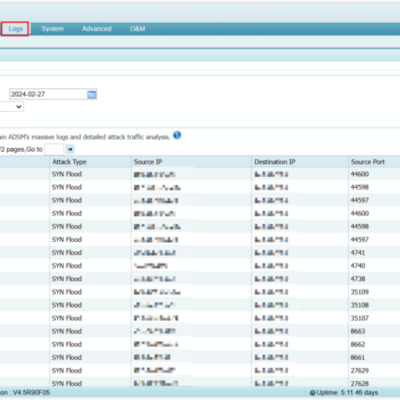
Policy Adjustment Based on Attack Events in ADS
This article provides a brief explanation of policy fine-tuning in ADS. Please note that fine-tuning the protection policy is a time-consuming process. This article focuses on how to check attack details in ADS based on attack events and optimize policies accordingly. Due to different versions of ADS, the screenshots shown...
Modern DDoS Attacks and the Rise of DDoS Coalitions
DDoS attacks have become an indispensable weapon to paralyze network systems in cyber warfare. Emerging DDoS attacks, such as HTTP/2 Rapid Reset and SLP reflection amplification attacks, are constantly emerging. Both attackers and defenders are struggling to upgrade their technology in order to discover new offensive and defensive strategies. DDoS...
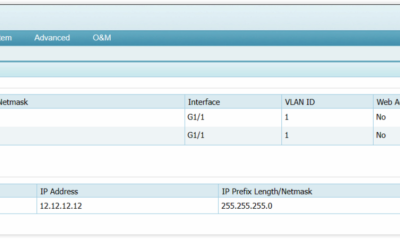
Preparation for ADS Diversion
This article summarizes the preparation configuration of ADS diversion. The specific configuration details may vary depending on the information of the ADS on the client side, router information, and ADS version. The configuration content and order can be referenced from this article. 1. Before configuring diversion, it is necessary to...
NSFOCUS Innovative DDoS Protection Technology Secures Your Network Perimeter
Cybersecurity is crucial for national security in the digital world, where major powers clash over their interests. However, technology also enables more sophisticated and harmful network attacks. One of the most common and dangerous types of attacks is distributed denial-of-service (DDoS), which can hide, coordinate, and scale up to overwhelm...
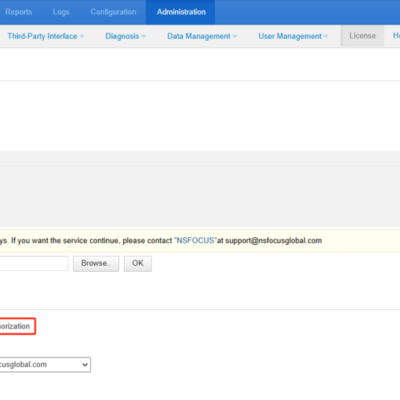
Preliminary Troubleshooting for Cloud Authentication Failure in ADS, NTA and ADSM
If the virtual product uses cloud authentication, it needs to communicate with the cloud authentication center periodically every day to complete the authentication and ensure availability. You can confirm the authorization mode by checking the Authorization Mode of the license. For example, in the image below, NTA uses cloud authorization....