NSFOCUS Security Labs is keeping an eye out for the trends in supply chain security and is pleased to share observations and thoughts with our blog readers. You will see the links for more posts we published about software supply chain security at the end of the article. In the next several posts, we are going to talk about the security solution for the software supply chain.
Numerous supply chain entities are involved in the development of enterprise business and the construction of capability ecology. To avoid malicious pollution of supply chain products and losses caused by supply chain attacks, the Open Trusted Technology Provider™ standard (O-TTPS) has clearly defined the integrity and global supply chain security requirements of COTS and ICT products to alleviate threats to the entire supply chain product lifecycle and manage its supply chain by applying well-defined, monitored, and effectively validated supply chain processes and best technical practices. In terms of supply chain security governance, the following four aspects need to be achieved:
1. Avoid risks from external introduction and conduct special security checks on software suppliers and supply chain products
Examine strictly before adoption and use leniently after adoption, which means eliminating all vulnerable software versions as of the date when they are introduced to strictly control external introduction risks, and after confirmation, the introduced software can be considered safe and available for internal use until vulnerabilities are exposed. Mark the software with a risk status and enter the next cycle.
2. Internal control diffusion, integrating security control into software SBOM management
Establish gray, white and blacklists in conjunction with supply chain management to prevent software versions with vulnerabilities from being introduced into enterprises; Mark software or systems that have exposed vulnerabilities but have not completed governance, and control strictly.
3. Stock management, combined with enterprise software SBOM to clarify dependencies and governance orderly
Due to the large number of existing systems, based on the principle of limited risk, the dependency relationships between systems should be comprehensively considered to develop differentiated governance strategies such as prioritizing governance for basic platforms and governance for critical internet applications, achieving the governance in an orderly manner in batches.
4. Continuously monitor and establish a risk warning mechanism to ensure the safety and controllability of the supply chain.
Vulnerabilities will persist for a long time and require continuous monitoring, proper emergency procedures, and orderly governance of software supply chain risks. Supply chain risk runs through the entire lifecycle of a product. Combined with recent supply chain attacks and intrusion events, we need to strengthen the management of supply chain product security certification from a regulatory perspective, and provide software SBOM hosting and trusted authentication services. Enterprises also need to improve supply chain asset management and security inspections, and can use the SBOM knowledge graph to clarify their supply chain dependency relationships, so that they can calmly respond when alerts appear.
By fully understanding public information such as security qualifications, development environment, and software components, the industry chain itself can ensure its compliance and integrity. Users can understand the safety and compliance status of their products through safety qualifications and information lists of products, ensuring that their judgment system meets the basic national safety protection requirements, and on this basis, carry out targeted reinforcement and supplementation. The purchaser can also ensure their own safety bottom line based on safety standards and make more suitable safety measures.
I. Special Security Inspection
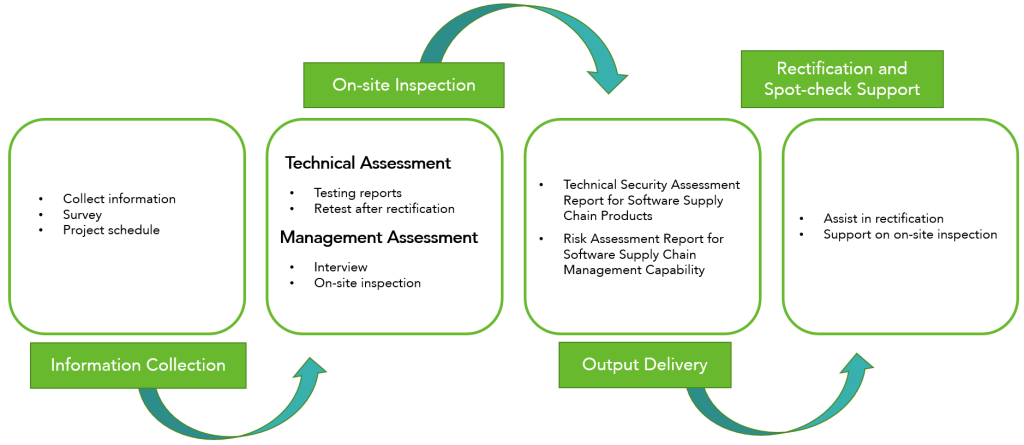
The risks in the software supply chain are dynamic. The purpose of the special security inspection for software supply chain security is to check and verify that the risks of a supervised organization are within an acceptable range. By setting up a special inspection plan for software supply chain security, users can monitor risk management activities, and review control measures regularly. The whole process of implementation is shown as follows:
Implementation process of special security inspection
The special inspection of supply chain security is mainly carried out in four steps:
1. Data collection
Identify and collect critical software supply chain products and sort out with software suppliers the existing sales licenses and relevant test reports, including third-party security test reports, code audit reports, vulnerability scanning reports, penetration test reports, rating evaluation reports, and software composition analysis reports.
2. On-site inspection
- Product safety technical inspection
Test the sales license and security of the product in order of open source components, purchased products, and customized products. Put stress on whether the software supply chain product has a sales license, whether there are relevant test reports (third-party security test report, code audit report, vulnerability scanning report, penetration test report, rating evaluation report, and software composition analysis report), and whether there are known but unpatched vulnerabilities, open source code, security risks of third-party components, etc.
- Management evaluation
According to relevant policies, standards, and the company’s supply chain management system, develop a software supply chain management evaluation form to evaluate and manage supplies.
Inspection methods include:
Personnel interview: to investigate the information security management status of an organization in terms of design, development, testing, delivery, and lifecycle management through communication and inquiry with the organization’s supplier management personnel and corresponding suppliers;
On-site inspection: to check security status on site to see the development and implementation of management systems and the use of technical measures and determine whether the enterprise meets requirements.
3. Deliverables
Based on the inspection and risks identified in security technologies and management systems, propose security issues and risk handling suggestions, and issue the report for Software Supply Chain Products and the Risk assessment report for Software Supply Chain Management Capability.
4. Coordinate rectification and spot-check support
Actively assist in the repair and rectification of known but unpatched vulnerabilities, open-source code, and third-party components that have security hazards identified through inspection. Cooperate and support the relevant spot checks after the special security inspection of the software supply chain.
Continue to read the next part: Software Supply Chain Security Solution – Supply Chain Security Supervision (Part 2)
Previous posts on software supply chain security:
- Software Supply Chain Security: Overview
- Threats against Software Supply Chain Security
- The Increasing Trend of Software Supply Chain Attacks
- The Increasingly Complex and Varied Vectors to Attack Software Supply Chain
- Security Concept for Software Supply Chain (Part 1) — Transparency of Software Supply Chain Compositions
- Security Concept for Software Supply Chain (Part 2) — Assessable Capabilities of Software Supply Chain Compositions
- Security Concept for Software Supply Chain (Part 3) – Building Trusted Software Supply Chain
- Relationship Between Security Concept and Security Assessment for Software Supply Chain
- Technical Framework of Software Supply Chain Security
- Key Technologies for Software Supply Chain Security—Techniques for Generating and Using the List of Software Compositions (Part 1)
- Key Technologies for Software Supply Chain Security—Techniques for Generating and Using the List of Software Compositions (Part 2)
- Key Technologies for Software Supply Chain Security – Detection Techniques (Part 1) – Software Composition Analysis
- Key Technologies for Software Supply Chain Security – Detection Techniques (Part 2) – Static Application Security Testing (SAST)
- Key Technologies for Software Supply Chain Security – Detection Technique (Part 3) – Dynamic Application Security Testing (DAST)
- Key Technologies for Software Supply Chain Security—Detection Technique (Part 4)—Interactive Application Security Testing (IAST) and Fuzzing
- Key Technologies for Software Supply Chain Security – Data Security Technology