NSFOCUS CTEM Offerings: A Comprehensive Solution to Enhance Your Security Posture Singapore - October 17, 2023 - NSFOCUS, a globally recognized leader in cybersecurity solutions, is pleased to announce a comprehensive suite of security offerings designed to enhance the Continuous Threat Exposure Management (CTEM) program for organizations of all sizes....
Category: Blog
APT Group DarkPink Exploits WinRAR 0-Day to Target Multiple Entities in Vietnam and Malaysia
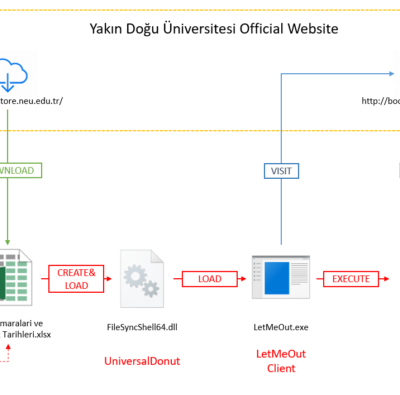
Overview NSFOCUS Security Labs has been continuously monitoring the newly discovered WinRAR 0-day vulnerability, CVE-2023-38831. It has come to our attention that the advanced persistent threat group known as DarkPink has recently begun exploiting this vulnerability to target government entities in Vietnam and Malaysia. In this round of attack activities,...
Countdown to GovWare 2023 – The Application of Artificial Intelligence (AI) in Cybersecurity
The stage is set, and the countdown has begun. GovWare 2023, a pivotal event in cybersecurity, is just around the corner. From a thorough review of the event agenda, we discerned that many speeches, keynotes and panels will be centered around the application of Artificial Intelligence (AI) in cybersecurity. As...
Microsoft’s October security update for multiple high-risk product vulnerabilities
Overview On October 11, NSFOCUS CERT monitored that Microsoft had released a security update patch for October, fixing 104 security problems, involving Microsoft WordPad, Skype for Business, Windows Layer 2 Tunneling Protocol, Microsoft Message Queuing and other widely used products, including high-risk vulnerability types such as privilege enhancement, remote code...
curl SOCKS5 Heap Overflow Vulnerability (CVC-2023-38545) Notification
Overview Recently, NSFOCUS monitored curl's official security announcement, which fixed the SOCKS5 heap buffer overflow vulnerability (CVE-2023-38545) and cookie injection vulnerability (CVE-2023-38546). The details of the vulnerability have been made public. Affected users should upgrade curl as soon as possible. SOCKS5 Heap Buffer Overflow Vulnerability (CVS 2023-38545) When curl is...
Exim Remote Code Execution Vulnerability (CVS 2023-42115) Notification
Overview Recently, NSFOCUS CERT detected an Exim remote code execution vulnerability (CVE-2023-42115). When external authentication is enabled, due to improper user input verification, an unauthenticated attacker can remotely exploit this vulnerability by writing data beyond the bounds, ultimately executing arbitrary code on the target server. At present, the details of...