ChatGPT is like a bomb in the Artificial Intelligence (AI) world, causing vibrations that have gradually spread to various industries. Against the backdrop of the widespread application of AI, why can ChatGPT still stand out and become the new top stream of popular discussion? After analyzing the core of ChatGPT,...
Blog
Models are also assets: AI will be a new arena of attack and defense
On the afternoon of April 24, 2023, RSA Conference announced the winner of the innovation sandbox contest this year, and HiddenLayer, an AI security vendor, was crowned the Most Innovative Startup 2023. Starting from HiddenLayer, the innovative sandbox champion, this article will further interpret and explore AI security. Figure 1....
Strapi Multiple Security Vulnerability Notice
Overview Recently, NSFOCUS CERT found that Strapi has officially issued a security notice, which fixes several Strapi security vulnerabilities. Due to a flaw in the Strapi system, when there are any entries created or updated by super administrator users on publicly accessed entries, attackers can execute arbitrary code on the...
NSFOCUS Launches NSFOCUS T-ONE CLOUD at RSAC 2023
A Revolutionary Security Architecture Empowers ISPs, MSSPs and Hosting Providers To Deliver SOC-as-a-Service To Customers Santa Clara, Calif. April 26, 2023 – NSFOCUS, a leading provider of network security solutions and services, is proud to announce the launch of NSFOCUS T-ONE CLOUD, a cutting-edge security architecture designed specifically for Internet Service...
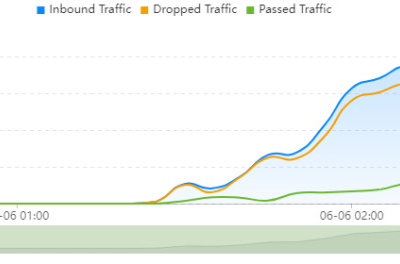
NSFOCUS Blocked an 8-Day Persistent DDoS Attack with 386.5 Gbps Peak Traffic
What happened In March 2023, NSFOCUS security team blocked the worst DDoS attack of the year. The attack was targeted at an Internet service provider customer located in Brazil, with a peak attack traffic of 386.5 Gbps and astonishing total attack traffic of 1184.4 Tbps. This large-scale DDoS attack lasted...
Spring Boot Security Bypass Vulnerability (CVS-2023-20873) Notice
Overview Recently, NSFOCUS CERT found that Spring officially issued a security notice, which fixed a Spring Boot authentication bypass vulnerability (CVE-2023-20873). When Spring Boot is deployed to Cloud Foundry and there is code/cloudFoundryapplication/* * that can handle matching requests, and used in conjunction with a catch all request mapping that...