Overview
On August 17, 2017, the National Bank of Ukraine (NBU) warned financial institutions in the country about a potential cyberattack. The virus would exploit the CVE-2015-2545 vulnerability to cause remote code execution by sending emails with the code disguised as a Microsoft Word document. Subsequently, a cybersecurity institution found traces of such an attack and suspected that it was associated with a series of other attacks targeting East European countries.
Related information can be found at the following link:
https://www.reuters.com/article/us-cyber-ukraine-banking-idUSKCN1AY0Y4
Technical Analysis
Basic Information
| File Name | Договор.docx |
| File MD5 | 57F51443A**********C6AFBD368E40E |
| File SHAI | 3224F221B**********CB2F1B4A16F7A6CC76190 |
| File Size | 346.40 KB (354713 bytes) |
| File Type | Office Open XML Document |
| Summary | Exploitation of the CVE-2015-4525 vulnerability to drop and execute malicious files |
| File Name | winword.exe |
| File MD5 | 5B4417521C**********2FE94AB395B2 |
| File SHAI | 2EE8EE6D8C**********BB96952861F3704E82E9 |
| File Size | 62.50 KB (64000 bytes) |
| File Type | Portable Executable 32 |
| Summary | Communicating with the server to obtain command codes and then performing different operations according to different commands |
Overall Attack Process
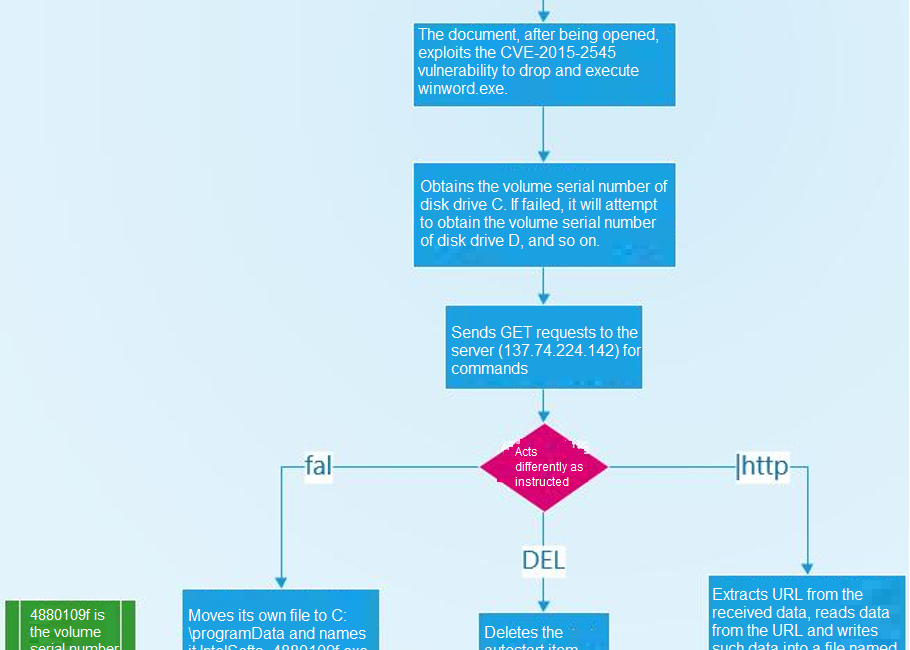
The attacker sends an email with a specially crafted Office document as an attachment, which, by exploiting the CVE-2015-2545 vulnerability in Microsoft Office, drops and executes an executable file. Then the child program, after connecting to the server, sends a GET request to the latter for commands, and finally performs actions as instructed.
The CVE-2015-2545 vulnerability affects Microsoft Office 2007 SP3, 2010 SP2, 2013 SP1, and 2013 RT SP1. An attacker could remotely execute arbitrary code via a specially crafted EPS image.
The overall attack process is as follows:
Behavior Analysis
Once opened, the malicious Office document will drop and execute a WINWORD.exe program. (FLTLDR.exe is an Office program.)
The EPS image extracted from the document contains a large quantity of data, followed by the exec function. Obviously, this Office document drops WINWORD.exe via this EPS image.
After being started, WINWORD.exe first attempts to get the volume serial number of a disk drive and then uses such serial number to craft a URL and rename the file.
The virus then crafts a URL and sends GET requests to the server to obtain command codes: fal, DEL, and |http.
fal
The virus moves itself into the system directory and renames itself IntelSofts_4880109f.exe, where 4880109f is the volume serial number previously obtained. Subsequently, the virus deletes the original file and modifies the registry by adding an autostart item.
DEF
The virus deletes the autostart item and exits the program.
|http
The virus obtains data when sending GET requests to the server previously. Now it extracts the URL from this data and then reads data from this URL before writing it into a local file with the name of MicrosoftUpdte.exe, which is then executed.
Attack Source
The IP address of the server accessed is 158.69.218.119.
Detection and Protection Methods
Static Detection
- The virus, after execution, drops WINWORD.exe in C:\Users\HelloWorld\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup.
- Then it creates an autostart item named IntelSofts in the registry in the HKCU\Software\Microsoft\Windows\CurrentVersion\Run
Dynamic Detection
The virus attempts to connect to the server (IP address: 158.69.218.119) to obtain data.
Preventive Measures
- Do not open emails from strangers, especially those containing links or attachments.
- Disable macros in Microsoft Office. If macros have to be enabled, make sure that the file comes from a reliable source.
- Enable the system firewall.
- Use the latest system and applications to prevent attacks based on known vulnerabilities.
NSFOCUS Solutions for Removing Trojans
- Short-term service: NSFOCUS engineers provide the onsite trojan backdoor removal service (manual services + NIPS + TAC) to ensure that risk points are immediately eliminated from the network and the event impact is minimized. After the handling, an event analysis report is provided.
- Mid-term service: NSFOCUS provides 3- to 6-month risk monitoring and preventive maintenance inspection (PMI) services (NIPS + TAC + manual services) to detect this malicious sample in an ongoing manner, thereby securing customers’ systems.
- Long-term service: NSFOCUS provides industry-specific risk mitigation solutions (threat intelligence + attack traceback + professional security service).
Conclusion
The attacker, by exploiting a vulnerability in Microsoft Office, crafts a malicious document, which will drop an executable with the name looking perfectly normal to effectively hide its true nature. Then the virus will modify the registry by adding an autostart item for persistent attacks. For such attacks, it is important to take preventive measures by hardening system security and requiring standard operations, so as not to end up a victim.