Overview
Recently, a researcher discovered that his computer motherboard BIOS comes with an anti-theft trace application Computrace from Absolute, which, after a computer startup, will be silently installed by the operating system and then transmit data overseas. Besides, this software can remotely obtain users’ files from their computers, monitor their behavior, and download and install unknown programs in an unauthorized manner.
Computrace resides in the BIOS chip of computers of various models. It provides network protocols for remote control, and so can be controlled by a remote server without any encryption or authentication. This function automatically runs at startup and resides permanently in users’ computers, exposing users to a great security risk.
Impact
Certain laptops, desktops, and workstations from a number of vendors, including Lenovo, Dell, Apple, Microsoft, HP, FUJI, Toshiba, Panasonic, Samsung, ASUS, and Acer, are affected by this threat.
Solution
Users are advised to check their own computers for this software and handle it as required by their own business requirements. Following are our recommendations on handling this threat.
- How to check
Choose the BIOS Security menu and check whether there is the Anti-Theft item. If yes, click it and then you can find Computrace.
- How to handle
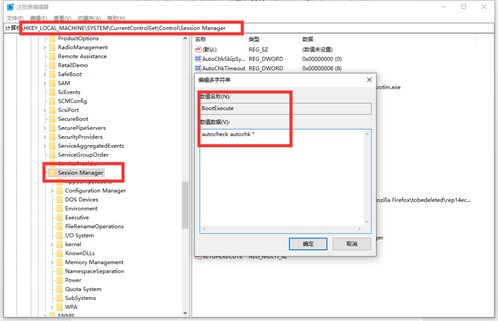
- Open the registry and find HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager. Back up the BootExecute key value and then delete it to stop this program from automatically running at startup.
- Delete rpcnet.exe, rpcnetp.exe, rpcnet.dll, and rpcnetp.dll in the System32 directory and terminate related processes in the Task Manager.
- Create the preceding four files in the System32 directory, with no content. For each file, right-click its name and choose Properties from the shortcut menu, click the Security tab, and then set Full control to Deny for all users/groups.
Besides, users can modify the hosts file to restrict access to specified domain names. In the hosts file in the C:\Windows\System32\drivers\etc directory, add the following information and then save the file:
127.0.0.1Â Â Â Â Â Â search.namequery.com
127.0.0.1Â Â Â Â Â Â search.namequery.com
127.0.0.1Â Â Â Â Â Â search2.namequery.com
127.0.0.1Â Â Â Â Â Â search64.namequery.com
127.0.0.1Â Â Â Â Â Â search.us.namequery.com
127.0.0.1Â Â Â Â Â Â bh.namequery.com
127.0.0.1Â Â Â Â Â Â namequery.nettrace.co.za
127.0.0.1Â Â Â Â Â Â m229.absolute.com
At the same time, configure the firewall to block Internet access requests from rpcnet.exe and rpcnetp.exe.
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
NSFOCUS IB is a wholly owned subsidiary of NSFOCUS, an enterprise application and network security provider, with operations in the Americas, Europe, the Middle East, Southeast Asia and Japan. NSFOCUS IB has a proven track record of combatting the increasingly complex cyber threat landscape through the construction and implementation of multi-layered defense systems. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide unified, multi-layer protection from advanced cyber threats.
For more information about NSFOCUS, please visit:
https://www.nsfocusglobal.com.
NSFOCUS, NSFOCUS IB, and NSFOCUS, INC. are trademarks or registered trademarks of NSFOCUS, Inc. All other names and trademarks are property of their respective firms.