Vulnerability Description On February 23, 2021, VMware released a security bulletin to announce the fix of two high-risk vulnerabilities in vSphere Client and ESXi. CVE-2021-21972: vSphere Client (HTML5) contains a remote code execution vulnerability in the vRealize Operations plug-in in vCenter Server, with the CVSSv3 score of 9.8. The affected...
Year: 2021
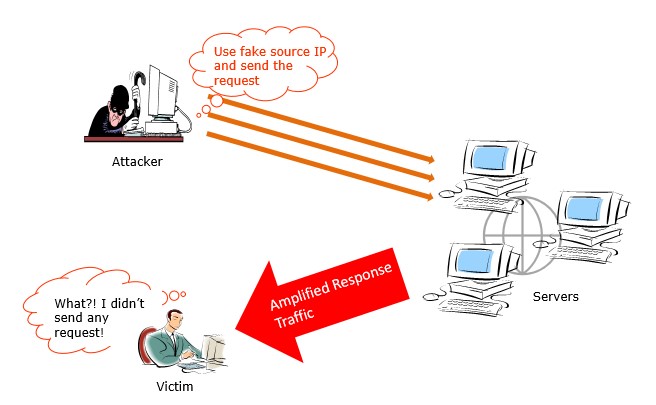
Amplification DDoS Attacks Come Again
Just in February, another two amplification DDoS attacks caught our attention. They are respectively abusing Plex Media Servers and Powerhouse VPN servers to amplify junk traffic to victims. Abuse Plex Media Server for Amplification Attacks On 3rd February, according to ZDNet, DDoS-for-hire services have found a way to abuse Plex...
Microsoft February Security Updates for Multiple High-Risk Product Vulnerabilities
Vulnerability Description On February 10, 2021, Beijing time, Microsoft released February 2021 Security Updates that fix 56 vulnerabilities, including high-risk ones like remote code execution and privilege escalation in various widely used products such as Microsoft Windows, Microsoft Office, Microsoft Exchange Server, Visual Studio, and Microsoft .NET Framework. In these...
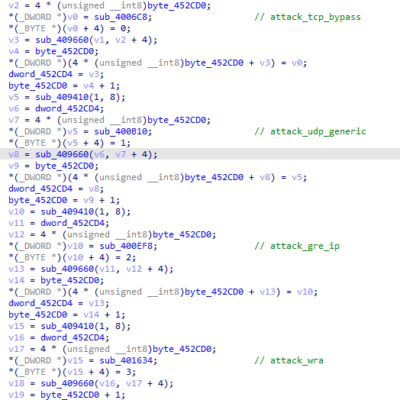
Windows TCP/IP Remote Code Execution Vulnerability (CVE-2021-24074)
Vulnerability Description On February 10, NSFOCUS found that Microsoft fixed the Windows TCP/IP remote code execution vulnerability (CVE-2021-24074) in its February updates. This vulnerability exists in the IPv4 source routing which is blocked by default in Windows systems. Attackers, via a crafted IP packet, could exploit this vulnerability to execute...
Enterprise Blockchain Security 2020-6
Regulatory Policies With years of development, the blockchain industry has taken shape, but enterprise blockchain applications are still at an exploratory stage. The blockchain ecosystem contains SPs, application vendors, and users. SPs in this context provide blockchain information services, whose compliancerequirements are surely different from those for other information services...
Information Disclosure-Incurred Asset Compromise and Detection and Analysis
According to a survey, 25% of internal security incidents are attributed to information disclosure. Attackers, merely through information disclosure, without needing to resort to measures with obvious patterns, like password cracking, can further acquire sensitive information about users and enterprises. It should be noted that this kind of attack method...