1 Vulnerability Overview
Recently, a security researcher with Twitter alias SandboxEscaper, once again, published proof-of-concept (PoC) code for a new 0-day vulnerability affecting Windows. This is the third Windows 0-day vulnerability published by this same researcher since August 2018. The vulnerability made known to the public this time could lead to arbitrary file read. Specifically, it allows low-privileged users or malicious programs to read, but not write into, arbitrary files on a targeted Windows host. Before an official patch is released by Microsoft, all Windows users will be affected by this vulnerability.
Currently, the researcher’s Twitter account has been suspended and his/her GitHub account taken down. However, since the PoC exploit for this vulnerability has been published, all related users should stay wary and keep their systems under scrutiny.
Reference link:
https://thehackernews.com/2018/12/windows-zero-day-exploit.html
2 Scope of Impact
All Windows systems are affected by this vulnerability.
3 PoC-based Vulnerability Check
Users can use the PoC to check whether the vulnerability exists in the operating system by reference to the video available at the following link:
https://v.qq.com/x/page/l1355lq4hp7.html
The PoC can be downloaded from the following link:
https://cloud.nsfocus.com/api/krosa/secwarning/files/windows-arbitrary-file-read-PoC.zip
4 How to Mitigate
This vulnerability cannot be remotely exploited. Therefore, to trigger it, an attacker has to run the related exploit on a targeted host. As of the day when this alert is released, no official patch has been released. Users are advised to check Microsoft’s official security bulletins from time to time so as to get the related patch as soon as possible.
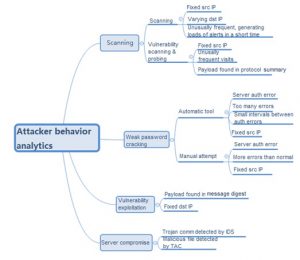
To prevent attackers from exploiting this vulnerability to read sensitive information from local hosts, users should avoid running files from unidentifiable resources, install antivirus software, and monitor hacking activities in real time. Common hacking methods are illustrated in the following figure.
Considering these common attack methods, users should pay special attention to alerts with the following patterns:
- If the same source IP address triggers loads of alerts and the interval between alerts is relatively short, scanning may be taking place. If the protocol summary of alerts contains some contents of the PoC, it can be confirmed that vulnerability scanning is happening. If the protocol summary contains any attacking payload, someone must be executing malicious code by exploiting the vulnerability.
- For repeated alerts on service authentication errors, if the interval between such errors is pretty short and it is always the same source IP address involved, a brute-force cracking event is happening. If the number of such errors is small, but still beyond the normal range, it is probably because an attacker is trying weak passwords again and again manually.
- If trojan communication is detected to be ongoing on the intranet, it is a sure thing that the server has been compromised.
Appendix
-
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
-
About NSFOCUS
NSFOCUS IB is a wholly owned subsidiary of NSFOCUS, an enterprise application and network security provider, with operations in the Americas, Europe, the Middle East, Southeast Asia and Japan. NSFOCUS IB has a proven track record of combatting the increasingly complex cyber threat landscape through the construction and implementation of multi-layered defense systems. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide unified, multi-layer protection from advanced cyber threats.
For more information about NSFOCUS, please visit:
https://www.nsfocusglobal.com.
NSFOCUS, NSFOCUS IB, and NSFOCUS, INC. are trademarks or registered trademarks of NSFOCUS, Inc. All other names and trademarks are property of their respective firms.