I. Principle
At present, there has been a great deal of news coverage about information disclosure. A large amount of information is constantly disclosed and sold through various websites, resulting in endless cases of telecom fraud. We have already known that SQL injection is the culprit responsible for all the cases. An SQL injection attack refers to an act of inserting SQL statements into parameter included in web forms, domain names, or page requests, in an attempt to trick the server into executing malicious SQL commands to obtain all information in the database.
II. Impact
As a high-risk vulnerability, SQL injection is very popular among hackers. Usually, it can pose the following types of threats:
- Obtaining all the information in database.
- Bypassing authentication, e.g. logging in to the background of a website by bypassing authentication.
- Taking control of a server
III. Examples
First, determine which functional module has the chance to interact with the database. Then confirm whether user input is allowed at the place whether interactions with the database occur. Usually, pages for login or query requires user input.
For example, open the login page of a system, http://xxx.xxx.com/login.php?action=login
In the username and password text boxes, type special characters such as a single quotation mark (‘), “and”, or “or”. In this case, there will be incorrect syntax when the server splices the characters entered by the user and the statements in the code. As a result, the database reports an error.
Then we can roughly deem that an SQL injection vulnerability exists.
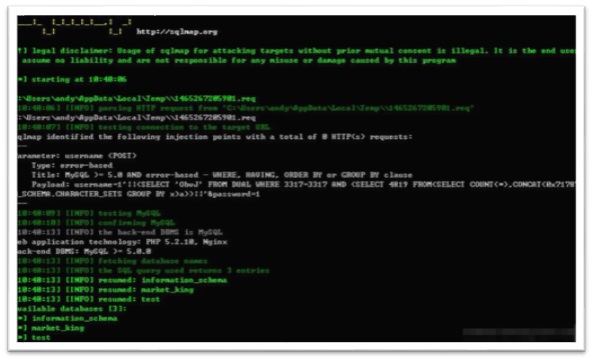
Using the SQL injection tool “sqlmap” for automatic injection, we can successfully obtain a great amount of user information by accessing all tables and information of the database.
At the same time, we can gain access to the table that contains the user names and passwords of website users. Using the obtained account credentials of the administrator, we can successfully log in to the background of the website.
IV. Protection Methods
SQL injection can be prevented in one of the following ways:
- Filter the submitted parameter data and reject special characters such as comma (,), “xor”, “or”, emdash (–), hashtag (#), “elect”, and “and”.
- Make sure that all query databases are submitted via the parametrized query interface provided by the database. Use parameterized statements that consist of parameters, instead of embedding user input variables into the SQL statements.
- Strictly limit the web user’s access to the database by giving the user only privileges that are essential to do his or her work, in an attempt to minimize the harm done by injection attacks to the database.
- Make sure that the website does not display SQL error information, including type error and field mismatch, in case attackers take the chance to obtain useful information.