Vulnerability Description
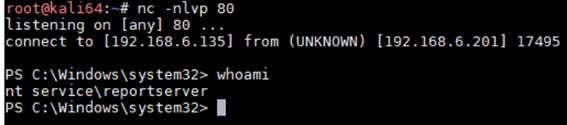
On February 12, Microsoft released a security update to announce the fix of the remote code execution vulnerability (CVE-2020-0618) in Microsoft SQL Server Reporting Services. SQL Server, developed by Microsoft, is a relational database management system (RDBMS) that is widely used in the world.
An attacker gaining low privileges could exploit this vulnerability to execute arbitrary cod in the context of the Report Server service account by sending a carefully crafted request to an affected Reporting Services instance of an affected SQL Server. Currently, the proof of concept (PoC) of this vulnerability is already publicly available. Affected users should apply the related security update for protection.
For details of this vulnerability, visit the following link:
https://portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2020-0618
Scope of Impact
Affected Versions
- SQL Server 2012 for 32-bit Systems Service Pack 4 (QFE)
- SQL Server 2012 for x64-based Systems Service Pack 4 (QFE)
- SQL Server 2014 Service Pack 3 for 32-bit Systems (CU)
- SQL Server 2014 Service Pack 3 for 32-bit Systems (GDR)
- SQL Server 2014 Service Pack 3 for x64-based Systems (CU)
- SQL Server 2014 Service Pack 3 for x64-based Systems (GDR)
- SQL Server 2016 for x64-based Systems Service Pack 2 (CU)
- SQL Server 2016 for x64-based Systems Service Pack 2 (GDR)
Note: For version details and update download links, see the appendix.
Mitigation
- Patch installation
Currently, Microsoft has released security updates to fix this vulnerability in system versions supported by Microsoft. Affected users should apply these updates as soon as possible for protection. These updates are available at the following link:
https://portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2020-0618
For more information on determining your SQL Server version number, see a Microsoft Knowledge Base Article from the following link:
https://support.microsoft.com/en-us/help/321185/how-to-determine-the-version-edition-and-update-level-of-sql-server-an
- Mitigations
As an attacker could encode a request packet to bypass the web application firewall, users are strongly advised to install security updates as soon as possible. Besides, anonymous access should be prohibited to make sure that only authenticated users can access related applications. If you suspect your server is vulnerable, in addition to update installation, change your password for login to the server to prevent attackers from exploiting it.
Appendix: Versions and Patches
| Update Number | Product | Apply If Current Product Version Is … | Patch Download Link |
| 4532097 | SQL Server 2016 Service Pack 2 (GDR) | 13.0.5026.0 – 13.0.5101.9
|
https://download.microsoft.com/download/6/d/8/6d8acd3e-e624-4256-8265-07c39b25e9ad/SQLServer2016-KB4532097-x64.exe |
| 4535706 | SQL Server 2016 Service Pack 2 CU11 | 13.0.5149.0 – 13.0.5598.27 | https://download.microsoft.com/download/9/f/a/9fa97512-ff9b-466a-918e-d95214fbfceb/SQLServer2016-KB4535706-x64.exe |
| 4532095 | SQL Server 2014 Service Pack 3 for 64-bit Systems (GDR) | 12.0.6024.0 – 12.0.6108.1 | https://download.microsoft.com/download/2/d/d/2ddc7094-0c7a-40b0-accf-07a5f57e0040/SQLServer2014-KB4532095-x64.exe |
| 4532095 | SQL Server 2014 Service Pack 3 for 32-bit Systems (GDR) | 12.0.6024.0 – 12.0.6108.1 | https://download.microsoft.com/download/2/d/d/2ddc7094-0c7a-40b0-accf-07a5f57e0040/SQLServer2014-KB4532095-x86.exe |
| 4535288 | SQL Server 2014 Service Pack 2 CU4 | 12.0.6205.1 – 12.0.6329.1 | https://download.microsoft.com/download/4/b/6/4b623928-0e26-4e4f-9d31-9974af8ac8ba/SQLServer2014-KB4535288-x64.exe |
| 4535288 | SQL Server 2014 Service Pack 3 for 32-bit Systems (CU) | 12.0.6205.1 – 12.0.6329.1 | https://download.microsoft.com/download/4/b/6/4b623928-0e26-4e4f-9d31-9974af8ac8ba/SQLServer2014-KB4535288-x86.exe |
| 4532098 | SQL Server 2012 for 64-bit Systems Service Pack 4 (QFE) | 111.0.7001.0 – 11.0.7462.6 | https://download.microsoft.com/download/5/6/b/56bfd2a1-48db-434a-9572-4d8dbf7ef047/SQLServer2012-KB4532098-x64.exe |
| 4532098 | SQL Server 2012 for 32-bit Systems Service Pack 4 (QFE) | 111.0.7001.0 – 11.0.7462.6 | https://download.microsoft.com/download/5/6/b/56bfd2a1-48db-434a-9572-4d8dbf7ef047/SQLServer2012-KB4532098-x86.exe |
Note: If your SQL Server version number is not represented in the table above, your SQL Server version is no longer supported. Please upgrade to the latest Service Pack or SQL Server product in order to apply this and future security updates.
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
About NSFOCUS
Founded in April 2000, NSFOCUS Information Technology Co., Ltd. (NSFOCUS) was headquartered in Beijing. With more than 30 branches and subsidiaries at home and abroad, the company provides most competitive security products and solutions for governments, carriers, and financial, energy, Internet, education, and medical sectors, ensuring customers’ business continuity.
Based on years of research in security assurance, NSFOCUS has set foot in network and terminal security, Internet infrastructure security, and compliance and security management. The company provides the intrusion detection/prevention system, anti-DDoS system, remote security assessment system, and web security protection products as well as professional security services for customers.
NSFOCUS Information Technology Co., Ltd. started trading its shares at China’s Nasdaq-style market, ChiNext, in Shenzhen on January 29, 2014, with the name of NSFOCUS and code of 300369.