-
Evolution of the Internet and Accompanying Cyber Threats
The fast growth of the Internet has brought constant changes to our lives. More than a decade ago, the egress bandwidth of 100 Mbps was available only to a small number of users, but today links with Tbps-level bandwidths are nothing unusual. The Internet connects everyone and everything, rapidly changing people’s centuries-long habits by bringing everything online, including communication, transportation, payment, and shopping, as well as household appliances. While benefiting from the convenience of the Internet, we are pushing the Internet forward.
Along with the high efficiency and convenience come risks and challenges. From the perspective of the infrastructure, the security of servers, links, and equipment rooms is the prerequisite for normal business operations. From the perspective of business delivery, the security of data and code is an important indicator of the quality of service (QoS), having a direct connection with user experiences. As we need to use the Internet to provide services, we cannot be the only player on the field. The cyberspace is imbued with a variety of threats: distributed denial-of-service (DDoS) attacks, botnets/trojans/worms, backdoors, vulnerabilities, advanced persistent threats (APTs), web defacement, to name but a few. When a specific service is considered, these threats pose severe challenges to the operation and maintenance (O&M) personnel, enterprises, and even underlying service providers. The damages caused by cyberattacks affect the service delivery quality and incur direct financial losses to enterprises. Therefore, the Internet world can be compared to an interconnected battlefield, where DDoS attacks are a frequent haunter that perpetrators take a particular liking for and defenders have to pull out all the stops against.
A DDoS attack is a cyberattack in which the perpetrator seeks to make a machine or network resource unavailable to its intended users by manipulating a large number of terminals, such as PCs, servers, and smart devices, to attack the target. This simple definition indicates that the booming of the Internet creates a hotbed for DDoS attacks and more devices connected to the network will provide more resources for DDoS attackers. Arguably, the evolution of DDoS attacks goes side by side with the development of the Internet. We can effectively defeat DDoS attacks only after gaining a deep understanding and grasp of the DDoS attack trends and keeping our protections up-to-date.
-
DDoS Attack Landscape
From the perspective of network layers, we can divide DDoS attacks into transport-layer and application-layer attacks. The former includes SYN flood, ACK flood, ICMP flood, and UDP flood attacks, and the latter includes HTTP GET/POST flood, HTTPS flood, DNS flood, and SIP flood attacks. These attack types are defined based on the fundamental protocol characteristics. Besides, DDoS attacks can be classified according to the attack behavior or attack tools, like spoofing, low-and-slow, and Black Nurse attacks.
The following describes the DDoS attack landscape from the aspects of the traffic trend and technical features.
2.1 Traffic Trend
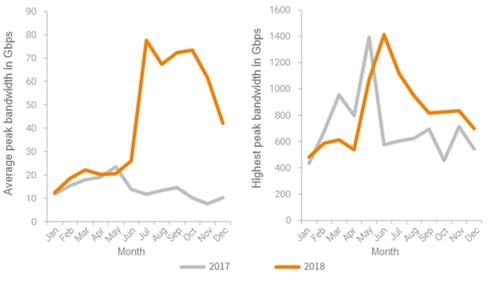
From the traffic volume, the peak bandwidth of DDoS attacks reaches a record high almost every year. In 2013, CloudFlare detected a DNS reflection attack with a peak bandwidth of 300 Gbps, which was soon overtaken by another DDoS attack that peaked at over 450 Gbps registered by Alibaba Cloud in 2014. Two years later, a trojan dubbed “Magic Weasel” (“Mo You” in pinyin) was found to be responsible for a DDoS attack measured at 632 Gbps. In 2018, the highest peak bandwidth of individual DDoS attacks hit 1.4 Tbps.
Figure 1 Average and highest peak bandwidths in 2017 and 2018
DDoS attacks keep making records in terms of the peak bandwidth, which, on the one hand, represents a trend of the Internet bandwidth rapidly developing and expanding, and on the other hand, indicates cyber criminals being capable of launching massive DDoS attacks. Successful execution of a high-volume DDoS attack requires control of a large number of devices and a substantial input of money. The fast evolution of the Internet provides abundant resources, and the good returns on the black market have allured swarms of hackers who are becoming members of a mature criminal gang. Although the record of peak attack bandwidths is constantly broken, very high-volume DDoS attacks are still small-probability events.
According to DDoS trend reports in the past few years, the total volume and the count of attacks have both increased year by year, but attacks below 200 Gbps are still dominant in all DDoS incidents. With the continuous expansion and fast growth of business bandwidths, this number will definitely become increasingly large. Therefore, defenders should make good preparations for high-volume DDoS attacks as preparedness averts peril.
2.2 Attack Types
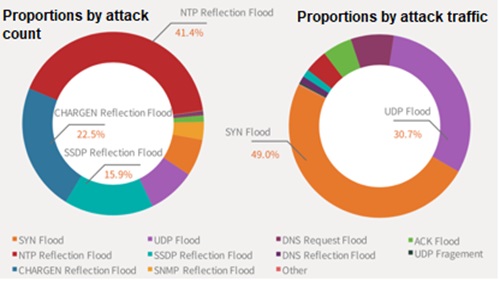
In terms of attack types, transport-layer attacks outdo application-layer attacks in both the frequency and total traffic volume. One of the important reasons behind this is that the cost of initiating attack traffic at the transport layer is far lower than that of application-layer attacks. Attackers can easily obtain open-source DDoS attack tools from the Internet and can generate SYN flood, ACK flood, and other DDoS attack traffic with only a PC or low-end server. More sophisticated attackers may use a packet sender to generate floods of traffic. If the targeted service runs without any protections against DDoS attacks, it will be easily overwhelmed. It is true that policies configured on a switch or firewall can block attack packets, but they do not work very well for hit-and-run attacks that feature short bursts of high-volume traffic in random intervals, spanning a time frame of days or weeks. In this case, O&M personnel will find it difficult to respond promptly. Moreover, reflection/amplification attacks have gained popularity over the past two years, including the DNS reflection flood, SNMP reflection flood, NTP reflection flood, and SSDP reflection flood. This type of attacks leverages characteristics of and vulnerabilities in protocols to attack a challenge-response authentication system. Owing to the low cost and satisfactory effect, such attacks are favored by hackers. From the perspective of protocols, UDP floods take up a majority of reflection/amplification attacks. This explains why more DDoS attacks are detected at the transport layer rather than the application layer.
According to the latest annual DDoS report from a security vendor, SYN floods and UDP floods accounted for 49.0% and 30.7% of the total DDoS traffic respectively, and various reflection/amplification attacks accounted for about 20%. Of all black market services and DDoS ransomware attacks we have observed, most take place at the transport layer. This, however, does not necessarily mean that attackers do not possess techniques for launching application-layer attacks. In fact, they tend to analyze the input-output ratio before carrying out any campaigns. Therefore, we on the defensive side see more transport-layer DDoS attacks than application-layer ones probably because attackers find the former are more cost-efficient.
Figure 2 Proportions of different attack types by count and traffic
Based on reality and the attack count statistics collected by NSFOCUS’s Attack Trend Monitoring (ATM) system, transport-layer DDoS attacks are still taking a dominant position. From the perspective of business development, more and more traffic will be transmitted in an encrypted manner. Therefore, customers require that anti-DDoS systems should be able to scrub HTTPS floods. Obviously, with the prevalence of transport-layer DDoS attacks, corresponding countermeasures also come to maturity. While the defending side is deploying more data security capabilities, the offensive side, lured by handsome gains, will not sit back. Once they develop new attack methods that are more effective and actionable, a new round of fights will be in full swing.
2.3 Attack Methods
So far, DDoS attacks have undergone thorough changes in both methods and techniques. First, DDoS attacks are not the ultimate end. Let’s remind ourselves that the Internet is pregnant with various attacks and DDoS is only one of them. A common method employed by attackers is to first launch a DDoS attack to cover up for their ulterior motives. When O&M personnel are burying themselves in response to the DDoS attack, attackers will further conduct a trojan, APT, or exploit-based attack. By occupying O&M personnel with the task of handling the DDoS attack, attackers can achieve their purpose of stealing business data or compromising server security.
Second, other attacks can also turn into DDoS attacks. An example of such attacks was the DDoS attack originated by “Magic Weasel”. The attacker first planted the trojan into a large number of target hosts, thus reducing them to zombies. Next, the attacker had these bot machines send massive requests to a destination IP address, making it deny service to legitimate users. This attack created history by generating up to 632 Gbps of traffic.
Third, zombies are everywhere. Previously, zombies were either PCs or servers. Recent research reports, however, discover that Internet of Things (IoT) devices like cameras and home routers contain lots of vulnerabilities that can easily turn smart devices into zombies. With the development of smart home, every object around us can become a source of attack against ourselves.
In an era characterized by the fast-moving Internet sector, how should we react to effectively address the ubiquitous DDoS threats and challenges? An appropriate scrubbing solution, manual O&M, digital report, and closed-loop governance are all feasible options. To ensure the efficiency, these activities must be carried out in a smart manner.
2.4 Attack Targets
DDoS attackers’ initial targets were mainly governments’ critical infrastructure, carriers, and the financial sector. Now their targets are expanded to the Internet sector. According to the 2018 DDoS Attack Trend Report jointly released by NSFOCUS and China Telecom, the cloud service/IDC, online gaming, and e-commerce were most targeted sectors. Cloud services/IDCs provide network infrastructure for a variety of businesses and were therefore favorite targets of DDoS attackers. Online gaming and e-commerce are latency-critical sectors that set great store by business continuity and players in these sectors are neck-deep in fierce competition. Besides, they see inflows and outflows of massive data as well as large flows of cash each day and so are fat geese in the eyes of attackers. On the one hand, attackers may be hired by a vicious competitor to launch attacks against other players for illegal gains. On the other hand, vicious competitors may try to win over users by degrading the QoS of their counterparts.
-
Robust DDoS Scrubbing Solution Powered by Smart Policies and Collaboration
A robust DDoS scrubbing solution should feature smart protection, collaboration, and operations.
3.1 Smart Protection
Current DDoS protection options include traffic filtering and rate limiting based on ACLs configured on routing devices or null routing, attack traffic detection and blocking based on session tables configured on firewalls, and decentralized handling with content delivery network (CDN) nodes. These options can, to some extent, mitigate the impact of DDoS attacks, but cannot address DDoS attacks in an optimal manner because of the possibility of affecting normal services. As for ACLs or null routing, O&M personnel need to put a lot of energy on the maintenance of policies and sometimes some services have to be sacrificed to ensure the bandwidth available for other services. As far as the firewall is concerned, its protection performance will be challenged by DDoS attacks originated from swarms of random source IP addresses. Protection with CDN nodes indicates either sacrifice of services on some nodes or transfer of the protection location from the local network to CDN nodes that does not make any difference in the protection effect.
By contrast, a smart protection solution features a professional anti-DDoS device, which is usually deployed at the network edge to scrub DDoS traffic based on a traffic check mechanism while ensuring normal service interactions as well as the downstream link bandwidth and the availability of other security devices. We call it a smart solution in that it can adapt itself to different business scenarios by using diverse protection algorithms and can dynamically identify source IP addresses by using a proper check mechanism. This is different from conventional solutions that usually employ rate limiting or null routing, which may affect normal service operations. Therefore, smart protection devices will play a crucial role in response to DDoS attacks and traffic scrubbing.
3.2 Smart Collaboration
An anti-DDoS device deployed at the egress of the local network suffices to protect against DDoS attacks whose bandwidth is below the egress bandwidth. However, when the attack bandwidth exceeds the egress bandwidth, a joint scrubbing solution should be used; otherwise, normal services will be affected, like no protection adopted. From the DDoS attack trends presented previously, high-volume DDoS attacks, although small in number, take place from time to time. When the local egress is congested and normal service requests cannot pass through it, a common practice today is to employ cloud scrubbing as a supplement to the on-premises protection.
Currently, there are two cloud scrubbing options on the market. The first one is to redirect website access requests to the cloud-side resource pool by means of DNS redirection and use remote nodes to scrub this traffic before reinjecting the clean traffic to the network for forwarding to the originally requested server.
This option features collaboration between the on-premises scrubbing device and the scrubbing cloud. To be smart, this solution must provide such functions as automatic traffic detection, notification, and DNS resolution so that attack traffic exceeding the local egress bandwidth will be automatically switched to the advanced collaboration platform for scrubbing. In this process, the scrubbing object, service type, and applicable policy should be accurately notified to the platform. As for traffic scheduling, automatic translation between domain names and IP addresses should be performed by the DNS server for fast and effective traffic diversion and protection.
The second option is similar to the first option, but performs traffic diversion based on IP addresses, omitting the DNS resolution step.
Only with smart collaboration, can the smart solution be called complete and show its advantages.
3.3 Smart Operations
Nowadays, the scrubbing solution is mainly maintained by individuals, who are responsible for analyzing attack behavior, adjusting protection policies, and monitoring the service status. To fulfill these tasks, O&M personnel should possess the latest DDoS defense skills and spend much time and energy understanding and grasping use methods and working principles of protection devices from different vendors. In the case of an unexpected DDoS incident, O&M personnel may be caught off hand and hesitant about how to configure appropriate policies on the protection device, resulting in attack packets passing through the device, hence disruption of services. A scrubbing solution is regarded smart when equipped with automatic attack behavior analytics and with the capability of monitoring services offered by the protection object. When finding that the protection effect is not satisfactory, it automatically adjusts protection policies according to the analysis result, performs ongoing monitoring, and makes prompt decisions to achieve efficient protection and smart closed-loop management. Such automated capabilities lower the human labor required and accelerate the response.
A robust DDoS scrubbing solution should not only be complete but also be characterized by autonomy of all components’ functionality and smartness of their collaboration, reducing the latency caused by manual O&M and improving the protection efficiency.
-
Efficient Anti-DDoS Operations System Powered by Smart Monitoring and Response
Making the devices and platform smarter is for the purpose of reducing input of human labor and improving the protection efficiency. Smart protection does not mean that people are no longer important. Instead, they are still essential in supervision and notification of the attack status. An efficient anti-DDoS operations system should have smart incident monitoring, report, and governance functions to ensure reliable and stable operations.
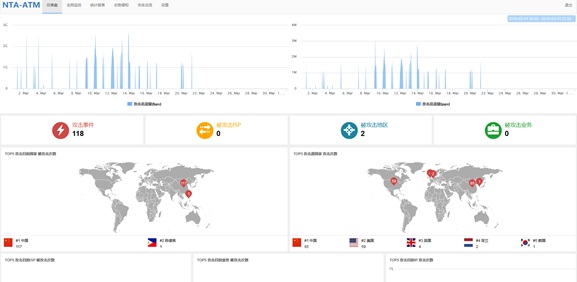
4.1 Smart Monitoring
Whether monitoring is conducted onsite or offsite, the operations department expects to be notified immediately after an attack is detected. Traditional monitoring and notifications usually use static messages and do not distinguish statistics for presentation. Smart monitoring has at least the function of dynamically displaying and tracking incidents. For example, an attack can be dynamically displayed based on source and destination locations, and related statistics displayed in a differentiated manner according to the attack size or type, providing O&M personnel with an insight into the current attack situation and letting them know what their top priority should be. Incident tracking uses a timeline to accurately reflect the protection system’s step-by-step response to the attack so that the operations department can be updated about the progress, make informed decisions, and know when the right time is to intervene.
Figure 3 NSFOCUS’s DDoS situation awareness maps
4.2 Smart Reports
Smart reports can also be seen as human-focused data analytics. Statistics are beyond calculations and should provide recommendations revolving around the report purpose. Report readers have various departments (O&M, security, network, …) and business scenarios. They want to receive recommendations on how to adjust policies and improve protection solutions in addition to learning about the frequency, number, traffic volume, and distribution of attacks. Therefore, reports should not be just dull and dry data, but rather a presentation and explanation of analysis results. In a word, good reports can not only make the protection system look smart but also help raise the quality of operations.
4.3 Additional Smart Functions to Close the Loop
In most scenarios, people are concerned about outsider-originated DDoS attacks against their networks or systems. However, internal hosts or servers can also be used without their knowledge as the source of attacks against external targets. When attacking a target, these compromised or controlled hosts not only consume their own resources but also occupy the uplink bandwidth to prevent other hosts from providing services to users. Therefore, a smart anti-DDoS solution should not only protect internal hosts from being affected by external factors but also be able to accurately locate internal hosts that have been infected based on detection data and smartly block packets sent by them. These additional smart functions close the loop of smart protection and complete the protection system to significantly enhance the value of the smart anti-DDoS solution with smart governance.
Operations monitoring is an integral part of DDoS protection, enabling O&M personnel to have a grip of the attack situation, analyze attacks on an informed basis, and promptly check and harden network security when and where necessary. This will definitely upgrade the response efficiency in DDoS defenses, and more importantly, contribute to a cleaner network environment and safeguard the secure operation of services and hosts across the network. When monitoring and feedback statistics are done smartly, security operations will be more efficient and effective.
-
Sum–up
Frost & Sullivan, in one of its analysis reports, points out that motives of launching DDoS attacks are varied, including political venting, competition for profits, and show-off of skills. It is impossible for us to know every possible reason behind these attacks. However, by using feasible technical methods and analyzing the technical development pattern, we can understand the DDoS attack landscape and propose options for addressing the current and future attacks.
DDoS attacks are becoming increasingly sophisticated for the following reasons:
(1) The development of the Internet gives rise to new attack types so that attackers can use a mix of various methods to confuse defenders and then cause damage.
(2) A variety of devices are connected to the network. Yet to mature, they contain a lot of vulnerabilities and backdoors that can be exploited by cyber criminals to launch DDoS attacks. The protocol stack behavior of these smart devices is inconsistent with related standards, which further complicates protection against DDoS attacks.
To effectively address DDoS attacks, we should pool resources from every party concerned to overcome the problems of egress bandwidth saturation caused by high-volume DDoS attacks and delayed technical updates. No product or solution is equipped with all necessary protection capabilities. Therefore, in the face of a complicated DDoS situation, anti-DDoS products and solutions should be flexible and scalable for future possible collaboration with other devices to defeat multi-vector attacks of various forms.
A smart DDoS scrubbing solution is of crucial importance to DDoS defenses. DDoS attacks are aimed at disrupting services, so business continuity and stability is a key indicator to measure the quality of protection. DDoS attacks keep changing in their patterns and their launch time is unpredictable. In this context, only with fast response, prompt judgment, and proper adjustment can we head towards a sure victory. This requires the anti-DDoS solution to adopt a smart mechanism for all-round monitoring, proper policy adjustment, and informed analysis and feedback. Therefore, DDoS protection cannot follow the beaten track. Instead, we should make full use of the big data and artificial intelligence (AI) technology, provide more effective warning and detection solutions, take advantage of cloud scrubbing and threat intelligence, and share threat information with regulatory bodies and security vendors, thereby achieving coordinated defense and win-win cooperation.
When the Internet moves to a higher level, cybersecurity will also enter a new epoch. We should take reality into account while setting our eyes on the future. Only by doing so, can we move faster and forestall attackers.