Overview With the development of key information infrastructure technologies such as cloud computing, 5G, IoT, and the Industrial Internet, cyberspace has linked industrial physical systems, social systems of humans, and network information systems, becoming the cornerstone of the development of the digital economy. Meanwhile, the attack surface in cyberspace is...
Category: Research
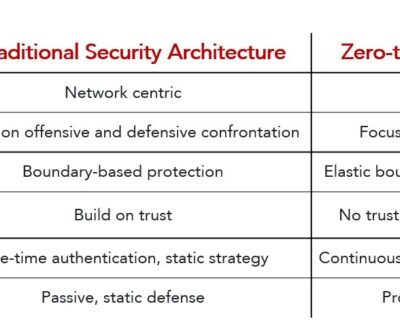
Zero Trust Network Access (ZTNA): Never Trust, Always Verify
After the prior two posts (SASE Popular Science Series – Understanding SD-WAN and SASE: The Relationship Between SD-WAN and SASE), you may already have a basic understanding of SD-WAN, which is used for network connections among users, assets and NSFOCUS Cloud in SASE. What security capabilities does NSFOCUS offer then?...
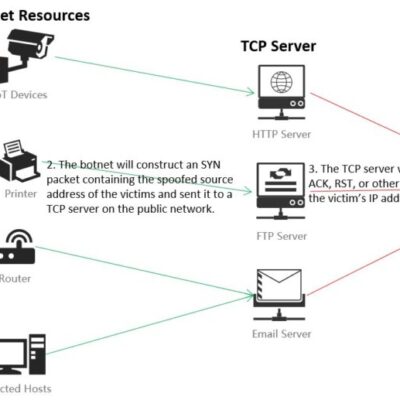
Research and Analysis of Middlebox-based TCP Reflective Amplification Attacks
Abstract In August 2021, Kevin Bock and his team from the University of Maryland and the University of Colorado Boulder proposed a new TCP reflective amplification attack method initiated by the middlebox at the USENIX conference. (See more details at https://geneva.cs.umd.edu/papers/usenix-weaponizing-ddos.pdf) In mid-April this year, NSFOCUS spotted that one of...
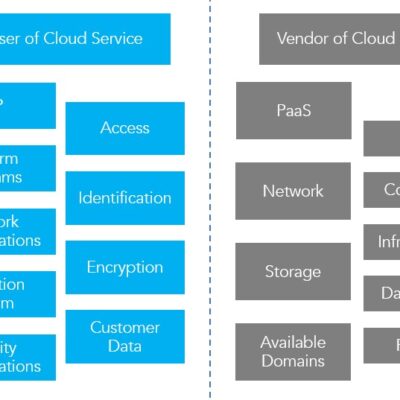
CASB, A Tech “Celebrity” from the Cloud Era
Debut of CASB With cloud computing being a key to industry revolution, more and more enterprises and organizations are discovering the benefits of storing and processing data in the cloud and migrating business systems from local data centers to the cloud. As business systems are migrated to the cloud, the...
Technical Report on Container Security (III)-2
Security Risks and Challenges—Security Threat Analysis Security Threat Analysis When we talk about security risks to containers, we mean security threats to hosts, to containers, and to the carried applications. (more…)
Technical Report on Container Security (III)-1
Security Risks and Challenges — Vulnerability and Security Risk Analysis Vulnerability and Security Risk Analysis As a specific implementation of the container technology, Docker is getting more and more popular in recent years. To some extent, Docker has become a typical representation of the container technology. Docker is based on...