By: Stephen Gates, Chief Research Intelligence Analyst, NSFOCUS Cyber extortion and attacks can take many forms – from ransomware to DDoS shakedowns and data-dump blackmail, organizations all over the globe have been directly impacted by these campaigns in 2016. This year we saw the first DDoS attack exceeding 1Tbps in size...
Category: Blog
Case Study: Thwarting 100,000+ Attacks on the G20 Summit, the NSFOCUS Experience
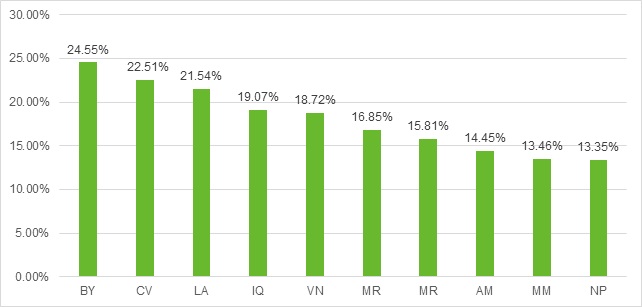
By: Dr. Richard Zhao, SVP of Global Threat Research, NSFOCUS In September 2016, prominent world leaders representing the top 20 global economies gathered together in Hangzhou, China to kick off the 11th meeting of Group of Twenty (G20). This year marked the first time that the event was hosted in...
Threat Intelligence: What It Is and How to Use It Effectively
By: Anil Nandigam, Sr. Director, Product Marketing, NSFOCUS In today’s cyber landscape, decision makers constantly question the value of their security investments, asking whether each dollar is helping secure the business. Meanwhile, cyber attackers are growing smarter and more capable every day. Today’s security teams often find themselves falling behind,...
Threat Intelligence – You can’t complete the picture, if you don’t have the missing piece.
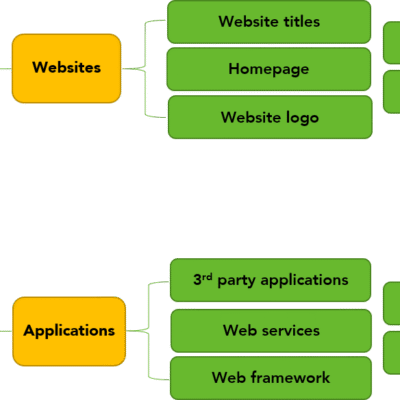
Author: Stephen Gates, Chief Research Intelligence Analyst, NSFOCUS Over the last year, the cybersecurity industry has been abuzz about this new thing called “threat intelligence”. However, threat intelligence (intel) as a whole is not really that new. Threat intel was probably used in every military-like campaign going back to the...
Advanced Persistent Threats – A Simple Analogy
Author: Stephen Gates, Chief Research Intelligence Analyst, NSFOCUS One of the things that amazes me the most is how the general population lacks a firm understanding of the cyber threats they face daily. Since few people outside of security circles have actually been trained in cyber security, the general lack...
Building Cyber Awareness – What I would do first!
Track: General Security Author: Stephen Gates, Chief Research Intelligence Analyst, NSFOCUS In my travels around the globe, I am often asked what strides an organization should take in order to measurably reduce their exposure to cyber threat actors, and their relentless cyber-attacks. Deploying the right security technologies obviously makes good sense....