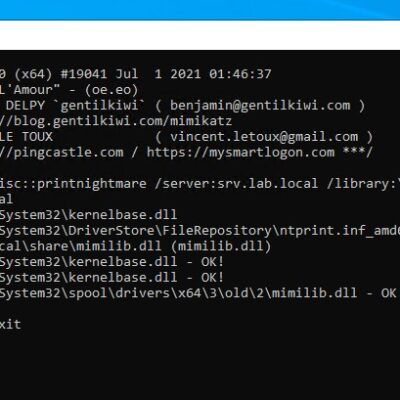
Overview On July 7, 2021, Beijing time, Microsoft released a security patch on the PrintNightmare vulnerability (CVE-2021-34527). NSFOCUS CERT recommends that users install this patch as soon as possible. On June 29, NSFOCUS CERT found that a security researcher published an exploit of the Windows Print Spooler remote code execution...
Category: Emergency Response
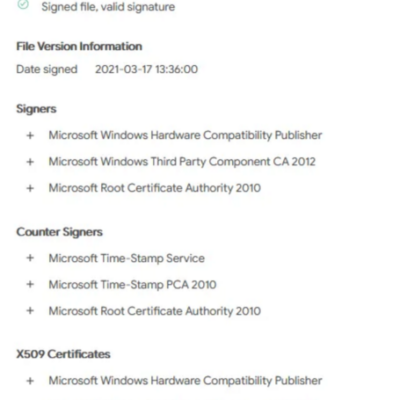
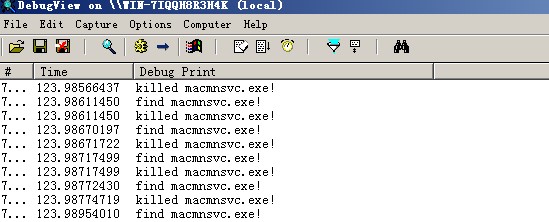
“Netfilter” malicious driver bypasses Microsoft’s signature system
In June 2021, German computer security solutions software company G Data Software detected a malicious driver named "Netfilter". Unexpectedly, the malicious driver bypassed and obtained Microsoft's file signature. When Microsoft learned about it, it immediately added the signature of the malware to the security center of the Windows system for...
Microsoft’s June 2021 Security Updates Fix Multiple Products’ High-Risk Vulnerabilities
Overview According to NSFOCUS CERT's monitoring, Microsoft released June 2021 Security Updates on June 9 to fix 50 vulnerabilities, including high-risk remote code execution and privilege escalation, in widely used products like Windows, Microsoft Office, Microsoft Edge, Visual Studio, and SharePoint Server. In the vulnerabilities fixed by this month's security...
Microsoft’s May 2021 Security Updates Fix Multiple Products’ High-Risk Vulnerabilities
Overview On May 12, 2021, Microsoft released May 2021 Security Updates to fix 55 vulnerabilities, including high-risk remote code execution and privilege escalation, in widely used products like Microsoft Windows, Office, Exchange Server, Visual Studio Code, and Internet Explorer. In the vulnerabilities fixed by this month's security updates, there are...
VMware VCenter Server Remote Code Execution Vulnerability (CVE-2021-21985) Threat Alert
Vulnerability Description On May 26, NSFOCUS CERT discovered that VMware released a security advisory that announces mitigation of the VMware vCenter Server remote code execution vulnerability (CVE-2021-21985) and vCenter Server plug-in authentication bypass vulnerability (CVE-2021-21986). The Virtual SAN Check plug-in in vCenter Server lacks input validation, allowing attackers who have...
Oracle April 2021 Critical Patch Update for All Product Families
Vulnerability Description On April 21, 2021, NSFOCUS detected that Oracle released the April 2021 Critical Patch Update (CPU), which fixed 400 vulnerabilities of varying risk levels. This CPU involves multiple commonly used products, such as Oracle Database Server, Oracle Java SE, Oracle Fusion Middleware, Oracle MySQL, and Oracle Communications. Oracle...