Executive Summary In 2020, the total number of distributed denial-of-service (DDoS) attacks declined a little compared with 2019, probably attributable to effective governance and enhanced protection capabilities of Anti-DDoS products. Despite this, DDoS attacks intensified during the COVID-19 pandemic, especially for healthcare, government, and education sectors. January to April 2020...
Category: DDoS Mitigation
‘FreakOut’ Malware Analysis – FreakOut Samples
Produced by: NSFOCUS Security Labs FreakOut samples appearing in the campaign were a typical IRC bot Trojan program written in Python. The Trojan program would connect to IRC channels in hardcoded C&C and act as instructed by C&C to collect information, launch DDoS attacks, interact with shells, and conduct ARP...
‘FreakOut’ Malware Analysis – Groups Behind FreakOut
Produced by: NSFOCUS Security Labs In early January 2021, NSFOCUS Security Labs captured an unknown malicious program called "out.py" via its real-time data platform, which is usually spread with the domain name "gxbrowser.net". NSFOCUS Security Labs conducted an in-depth research on the samples and payloads of the malware and compared...
Numerous Bank Customers Getting Hooked on SMS Phishing
Event Overview Since February 2021, NSFOCUS's emergency response team has found that several provinces in China saw multiple SMS phishing events using fake bank domain names. As these events bear a striking resemblance in the phishing playbook, attack means, and phishing website pages, we can largely determine that these attacks...
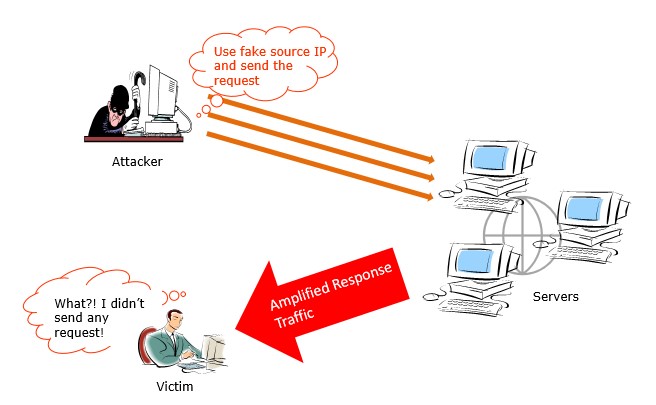
Amplification DDoS Attacks Come Again
Just in February, another two amplification DDoS attacks caught our attention. They are respectively abusing Plex Media Servers and Powerhouse VPN servers to amplify junk traffic to victims. Abuse Plex Media Server for Amplification Attacks On 3rd February, according to ZDNet, DDoS-for-hire services have found a way to abuse Plex...
Information Disclosure-Incurred Asset Compromise and Detection and Analysis
According to a survey, 25% of internal security incidents are attributed to information disclosure. Attackers, merely through information disclosure, without needing to resort to measures with obvious patterns, like password cracking, can further acquire sensitive information about users and enterprises. It should be noted that this kind of attack method...