Top 10 countries: The above diagram shows the top 10 regions with most malicious IP addresses from the NSFOCUS IP Reputation databases in October. But the United States has the largest allocated IP addresses in the world and China is in the second place. So, report IP Reputation as a...
Category: DDoS Mitigation
Deep Analysis of Memcached Large DRDoS Attacks – China Telecom DamDDoS & NSFOCUS Jointly Released
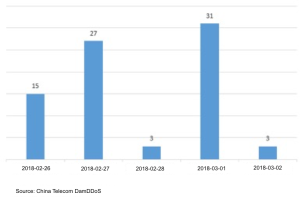
Recently, many domestic and foreign security companies and agencies issued warnings about the Memcached Distributed Reflection Denial of Service attack, which aroused the concern of all parties. According to our monitoring, the peak traffic for this attack has now reached 1.35T. On Feb. 27, Memcached's reflection DDoS attacks ranged from hundreds of...
Traceback of a DDoS Attack
An abnormal increase in the CPU usage of a telecom carrier's 4G firewall substantially slowed down the access from some iPhone users to the Apple website. We suspected that the carrier was hit by a DDoS attack. With the visualized traceback function of NSFOCUS Big Data Security Analytics (BSA), we...
Phantom Squad – DDoS Threat
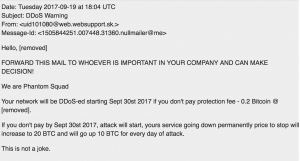
Overview It appears that the new syndicate of the Armada Collective referred to as the Phantom Squad is planning to launch a global DDoS attack on September 30th. Below you will find a screenshot of the mass spear-phishing email that has been distributed to many organization and companies around the...
Does a Dropbear DDoS in the Woods?
Author: Guy Rosefelt - Dir, PM Threat Intelligence & Web Security Recently, NSFOCUS has seen some interesting DDoS behavior. Since Q4 of last year, there has been a rise in SSL/VPN and SSH based DDoS attacks. Most people would not equate VPN or SSH as a viable mechanism for what...
2016 Q3 Report on DDoS Situation and Trends
Sources of Data NSFOCUS collects data from all of their DDoS Protection Solutions deployed worldwide that are being managed by their managed service offering. The botnets that are used across the world can be tracked by NSFOCUS, and those details are used to formulate many of the attack trends shown...