3.4 DDoS Attacks
3.4.1 Behavior Seen
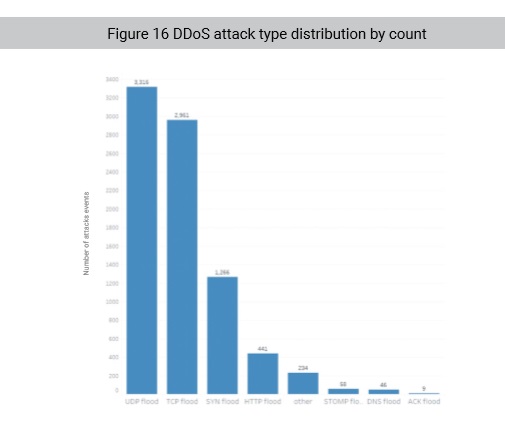
Effective attack instructions are botnet attack instructions that control a task other that starting and stopping. Effective attack instructions captured in 2018 included DDoS, Local Area Network (LAN) scanning, and vulnerability exploits among other types of attacks. There were 440,000 DDoS attack instructions issued from botnet families, constituting most effective attack instructions. Categorizing attack instructions by source IP address, target IP address, attack type, and attack initiation time, we found that the DDoS attack instructions were responsible for 8,332 attack events. From key indicators of these attack events, we discovered that UDP and TCP flood attacks, with a total percentage of 75.34%, formed the biggest part of attacks. Figure 16 shows the numbers of various DDoS attacks.
In addition, we captured numerous attack instructions directly against anti-DDoS service providers. These instructions, whether for directly attacking providers, testing anti-DDoS capabilities, or just showing off their botnet attack capabilities, reveal that botnets and their attack controllers still hold the initiative on the DDoS battlefield and need to be taken seriously. Many anti-DDoS providers can mitigate massive attacks by distributing the attack traffic across DDoS scrubbing centers. But a massive attack directed at one or few scrubbing centers could cause great impact to the provider.
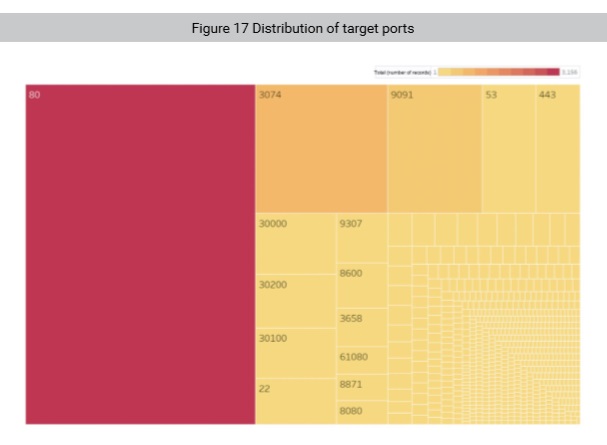
In terms of ports, port 80 was still most frequently targeted and ports 22, 25, 53, and 443 were also favored by DDoS attacks. It should be noted that two attack events, respectively led by the Gafgyt family and the BillGates family, were against ports 3074 (Xbox Live , both TCP and UDP) and 9091 (TCP: CiscoSecure and Transmission web UI, UDP: xmltec-xmlmail and QuickTime server) which were found to be easy targets. The two attack events are discussed in the Analysis section.
3.4.2 Analysis
Reflection Attacks Making a Resurgence
At the end of 2018, the number of UDP flood attacks rose unexpectedly, surpassing TCP and SYN flood attacks to become the dominant DDoS attack type based on attack DDoS instructions. This may be related to the popularity of some UDP based reflection attacks.
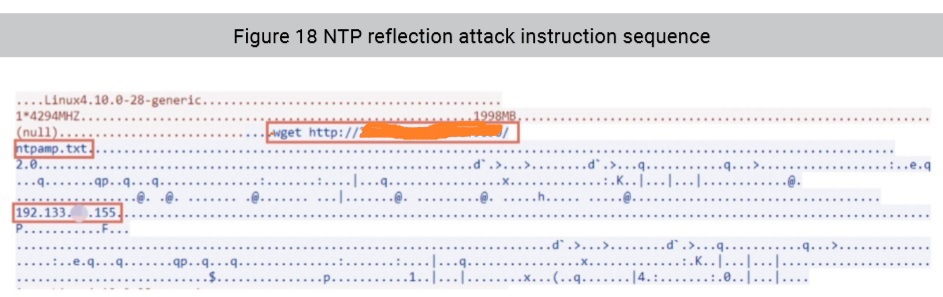
Reflection DDoS attacks amplify the amount of UDP response traffic compared to the amount of request traffic initiating the attack such as a small DNS query returning a response with a lot of DNS data. Reflection attacks provide attackers with a lot of flexibility because they can utilize a number of different UDP services for attacks, yet are difficult to detect, trace and prevent. Because of these characteristics, such attacks have long been popular with hackers in conjunction with various botnet families. In 2018 H1, NSFOCUS and several other security vendors detected Memcached based reflection DDoS attacks which generated several massive DDoS attacks, the size of which were previously unseen. NTP reflection and SSDP reflection attacks have also been popular in 2018. What is concerning is the multi-protocol capabilities being deployed in newer malware which allows customization of UDP flood instructions, giving botnet controllers the ability to launch multiple DDoS reflection attacks using different protocols simultaneously or in series.
Figure 18 shows a typical reflection attack instruction sequence. During this sequence, the C&C server dispatches download instructions to direct the controlled end to download the reflector list. The controller then issues customized UDP flood instructions directing the bot to launch NTP reflection attacks against specific target IP addresses.
Considering the number of UDP flood attack instructions seen being issued in the wild, we believe governance crackdown on poorly secured reflection sources (as was recently done in China and other countries for DNS servers) is the most effective and economical defense against reflection attacks. After that, organizations still need to implement defensive capabilities to defend against other common UDP flood and reflection attacks.
Internet Gaming Users Fall Victim to Botnet DDoS Attacks
Port 9091 is used by a variety of services including email protection software GFI MailEssentials, BitTorrent client Transmission, and Openfire chat & messaging server. In the first half of 2018, we observed an attack event where BillGates carried out DDoS attacks against port 9091 on certain IP addresses in South China. Although we could not verify If these targets had port 9091 open, if so, the DDoS attacks would have devastated them.
Port 3074 is used by Microsoft’s Xbox home gaming systems to participate in the Xbox Live service. The Gafgyt family launched numerous attacks against this port in Q4 2018. During those attack events, the attacker mounted hybrid DDoS attacks against port 3074 on each IP address monitored. As personal devices are less capable of resisting DDoS attacks than enterprise devices, these attacks could block network communications of host devices immediately, leading to players going offline. These kinds of attack behavior have been seen used against many online multiplayer and esports services, allowing attackers to manipulate matches by increasing the latency of other players or completely knocking them offline.
From the above, we find that targeted DDoS attacks are easy to launch and capable of doing specific, yet extensive damage. If these kinds of attacks become more prevalent, online service providers should consider including basic DDoS protection for users. This could, however, greatly increase the operating costs of online gaming services and may actually be cost prohibitive in which case, revenues could decline as users become frustrated from these tactics.
To be continued.