Key Technologies for Software Supply Chain Security—Techniques for Generating and Using the List of Software Compositions (Part 1) Analysis Tools of List of Software Compositions According to the classification by the LINUX Foundation [1], SBOM tools are grouped into three categories, namely, to produce, consume and transform. Each category has...
Blog
Introduction to NSFOCUS WAF REST API
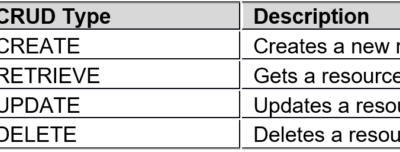
WAF REST API is known as the secondary development interface, and can be called by third-party platforms/software for adding, deleting, modifying, and querying WAF as wells its site, policy, and other configurations. Basic Conventions Format conventions: WAF REST API requests and responses are in JSON format: The attribute (primary key)...
Key Technologies for Software Supply Chain Security—Techniques for Generating and Using the List of Software Compositions (Part 1)
The list of software compositions and the software bill of materials (SBOM) are different in the requirements for the granularity of the "minimum elements" of the software, without a substantial difference in technical ideas and implementation steps. Considering the relatively mature SBOM generation tools and techniques, this document focuses on...
IBM WebSphere Application Server Remote Code Execution Vulnerability (CVE-2023-23477) Notice
Overview Recently, NSFOCUS CERT found that IBM officially fixed a remote code execution vulnerability in WebSphere Application Server (CVE-2023-23477). Due to the flaw in WebSphere Application Server's validation of the data entered by users, under certain conditions, unauthenticated remote attackers can finally execute arbitrary code on the target server by...
Protecting IoT Ecology and Building a Secure Future for Smart Cities
Smart city is a multi-disciplinary, multi-field, highly integrated large-scale system. One of the core components of the intelligent system of smart city is the Internet of Things (IoT), which drives the technologies that enable the perception of, as well as interaction and coordination with the physical world by the digital...
NSFOCUS Optimized Emergency Response for Network Security Incidents and Vulnerabilities
At the beginning of 2023, NSFOCUS started an internal review and optimization of its Emergency Response Process for Network Security Incidents and Vulnerabilities. This policy is used to guide the implementations and operations of emergency response to ensure the controllability of quality and progress, as well as the rapidity of...