Se a sua empresa depende de site, sistema interno, API, e-mail corporativo, ambiente em nuvem e operação digital contínua, entender como funciona o monitoramento de ameaças online é uma necessidade prática, não só técnica. Ataques não seguem rotina, não surgem em fila organizada e, quase sempre, aparecem por meio de...
Blog
RSAC 2026 Innovation Sandbox | Geordie AI: Architect of Enterprise AI Agent Security Governance Systems
Company Profile Geordie AI is a cybersecurity startup founded in 2025 and headquartered in London, specializing in AI Agent security and governance. The company has developed an "Agent-native" security platform for enterprises, enabling real-time discovery, behavior monitoring, and risk control of AI agents deployed within organizations. This helps security teams...
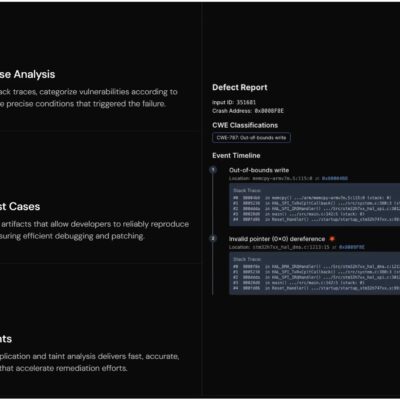
RSAC 2026 Innovation Sandbox | Crash Override: From Passive Scanning to Active Traceability, Reshaping the Software Supply Chain Security Foundation
Industry Macro Background and the Software Supply Chain Crisis By 2026, the deepening of global digital transformation, coupled with the proliferation of Generative AI and large language models, is reshaping software development. The industry is shifting from being "efficiency-driven" to "governance-driven." The root cause lies in the loss of visibility...
RSAC 2026 Innovation Sandbox | Fig Security: Guardian of the Reliability of Security Detection Systems
Company Profile Fig Security is a cybersecurity startup founded in 2025. It is headquartered in Israel with business operations also based in the United States. Despite its short history, the company has quickly gained industry attention through its innovative approach to security operations and has gradually emerged within the global...
RSAC 2026 Innovation Sandbox | Token Security: Advocate of the Machine-First Identity Security Concept
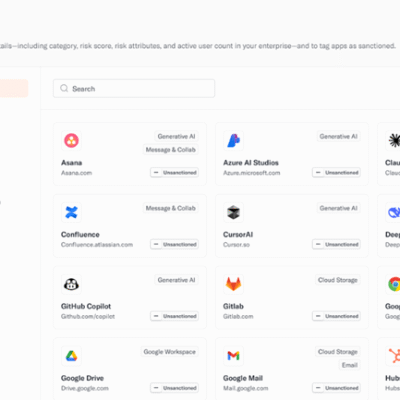
Company Introduction Token Security[1] (see Figure 1) is a cybersecurity company focusing on the security of Agentic AI and Non-Human Identities (NHI). It is committed to building an "identity layer" that enables Agentic AI to land securely. As AI agents evolve from assistants to independent actors that can perform tasks, Token...
RSAC 2026 Innovation Sandbox – Glide Identity: Building a Next-Generation AI Passwordless Authentication Platform
Company Profile With the rapid development of artificial intelligence technology today, identity and access control have leapt from a simple security component to the core control plane of the digital world. In this context, Glide Identity, a startup shortlisted for the 2026 RSA Conference Innovation Sandbox, stands out. The company...