Today, we're diving into the fascinating world of cyber ranges—a critical component in the ever-evolving landscape of cybersecurity. But what exactly is a cyber range? Let's break it down. What is a Cyber Range? A cyber range is a sophisticated environment that leverages technologies such as virtualization, hybrid reality, security...
Blog
NSFOCUS Showcases Two Groundbreaking Topics at SAS 2024
NSFOCUS Showcases Two Groundbreaking Topics at SAS 2024: An In-Depth Analysis of the DarkCasino APT Group and the Evolution of New Botnets. SANTA CLARA, Calif., October 30, 2024 – The 17th Security Analyst Summit (SAS), a premier global event focused on cybersecurity, recently concluded in Bali, Indonesia, where NSFOCUS was...
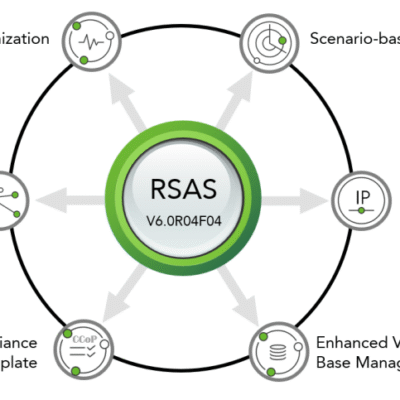
NSFOCUS RSAS New Features: Scenario-based Scans, CCoP Benchmarks, Richer Vulnerability KB, and More
In the ever-evolving landscape of cybersecurity threats, we're always on the lookout for cutting-edge solutions to safeguard our digital assets. Today, I'm thrilled to announce the release of NSFOCUS RSAS 6.0R04F04, a new iteration that comes packed with a suite of features designed to enhance your security posture and streamline...
NSFOCUS Enhances DDoS Protection Capabilities in New Version of Anti-DDoS Products
We’re excited to announce an upcoming upgrade to our NSFOCUS on-premises DDoS protection product suite! The new version of our Anti-DDoS products will further enhance our capabilities to detect and protect against DDoS attacks, empowering our customers to tackle increasingly sophisticated threats. What’s New in Version 4.5R90F06? Enhanced Protection with...
NSFOCUS Exhibits at GovWare 2024
Singapore, October 16, 2024 – NSFOCUS, a global leader in cybersecurity solutions, today exhibits at GovWare 2024, Asia’s premier cyber information and connectivity platform, taking place at Sands Expo and Convention Centre in Singapore. NSFOCUS at GovWare 2024 Founded in 2000, NSFOCUS has built a reputation for deep technical expertise...
A Deep Dive into DDoS Carpet-Bombing Attacks
With the rapid growth of the internet, especially in areas like cloud computing, 5G, and IoT technologies, the scale of botnets continues to expand, intensifying the battle between attack and defense. In response, DDoS attacks have evolved, taking on a more intelligent form to evade security defenses. Traditional DDoS attacks...