By default, NSFOCUS NIPS identifies the protocols and detects attacks on standard ports only. For example, File Transfer Protocol (FTP) operates on ports 20 and 21, Telnet protocol operates on port 23, and HTTP protocol uses port 80. However, the traffic using preceding protocols on non-standard ports will not be...
Author: Jie Ji
Description of ADS Hardware Status Alerts
1.CPU threshold The default threshold value is 80%.The system CPU usage is updated every 10 seconds. 2.Memory threshold: The default threshold value is 90%.The system memory usage is updated every 10 seconds. 3.CPU temperature threshold: The default threshold value is 90 °C.The equipment CPU temperature is updated every 10 seconds....
What Information will Master/Backup NTAs Share
After two NTAs are configured to operate as the master and backup NTAs for hot standby, the master NTA will synchronize the configuration to the backup one in real time. This will guarantee that the configuration of the backup NTA is consistent with that of the master NTA. The synchronized...
NSFOCUS was listed in 2022 Gartner® Market Guide for Security Orchestration, Automation and Response Solutions
Santa Clara, Calif. July 6, 2022 – We are pleased to announce that NSFOCUS has been listed as a Representative Vendor in 2022 Gartner® released Market Guide for Security Orchestration, Automation and Response Solutions report for our product ISOP. ISOP has flexible out-of-the-box capabilities, automated orchestration capabilities and rich intelligence operations...
Multiple High-Risk Vulnerability Alerts of GitLab
Overview On July 1, 2022, NSFOCUS CERT detected that GitLab officially released a security bulletin and fixed multiple security vulnerabilities in GitLab Community Edition (CE) and Enterprise Edition (EE). Please take measures to protect it as soon as possible. GitLab Remote Code Execution Vulnerability (CVE-2022-2185): A remote code execution vulnerability...
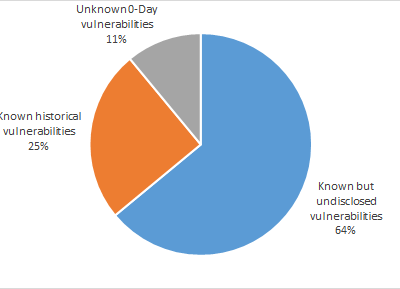
Technologies and Applications of the Security Knowledge Graph – Employ Security Knowledge Graph and Join Hands for Cognitive Intelligence
Overview With the development of key information infrastructure technologies such as cloud computing, 5G, IoT, and the Industrial Internet, cyberspace has linked industrial physical systems, social systems of humans, and network information systems, becoming the cornerstone of the development of the digital economy. Meanwhile, the attack surface in cyberspace is...