Overview
Beginning in the second quarter of this year, NSFOCUS Security Labs discovered that the APT group Gamaredon began frequently using a number of different types of attacks to conduct cyberattacks against military and police targets in Ukraine’s Kherson, Donetsk and other regions.
In this attack cycle, Gamaredon mainly used attack tools such as malicious office documents, malicious HTML attachments, and malicious SFX files, along with carefully designed decoy messages, to form three different attack processes. Tracking analysis revealed that Gamaredon significantly increased the frequency of various types of attack activities in late July, and the number of decoy deliveries reached a new peak.
About APT Group Gamaredon
The earliest activities of the Russian APT group Gamaredon can be traced back to 2013. The group has carried out phishing attacks against government departments in Eastern European countries, especially Ukraine, for a long time. Common tools include various decoys disguised as official government documents, various scripting programs, and various homemade Trojans.
The Ukrainian side blamed the Gamaredon organization on the Russian Federal Security Service (FSB).
Gamaredon is known for its huge attack scale. According to NSFOCUS Global DDoS Attack Landscape (H1 2022) report, medium and high-sophistication level threat actors have more attack resources to launch large-scale attacks. With adequate attack resources, launching Tb-level DDoS attacks will not be a difficult thing. Â
With its large attack resources, the Gamaredon consistently delivers a wide variety of short-lived attack modules to minimize the chances of exposure and countermeasures.
As the situation between Russia and Ukraine gradually escalated, the Gamaredon group significantly increased the frequency of its cyberattacks, actively using various known techniques to try to infiltrate critical institutions such as the Ukrainian government, military barracks, and police stations.
Trend Analysis
In the process of tracking and analyzing the three types of attack activities used by Gamaredon, we found that the organization significantly intensified the frequency of attacks after July, and the attack trends showed the following two aspects:
- Gamaredon added dependencies on the attack processes of spear phishing attacks using malicious HTML attachments and attacks using SFX self-extracting files.
- The decoy content used by attackers has gradually shifted from news-based information in the early days to military-based information.
Our tracking study found that, on the one hand, a malicious SFX self-extracting file attack process commonly used by Gamaredon had two obvious peaks in late April and late July, and the decoys carried in the process gradually unified into various Russian military documents; On the other hand, a spear phishing attack containing malicious HTML attachments and lnk files also reached its peak in mid-to-late July, and the bait content of such spear phishing emails focused more on Ukrainian military information and cyber security information.
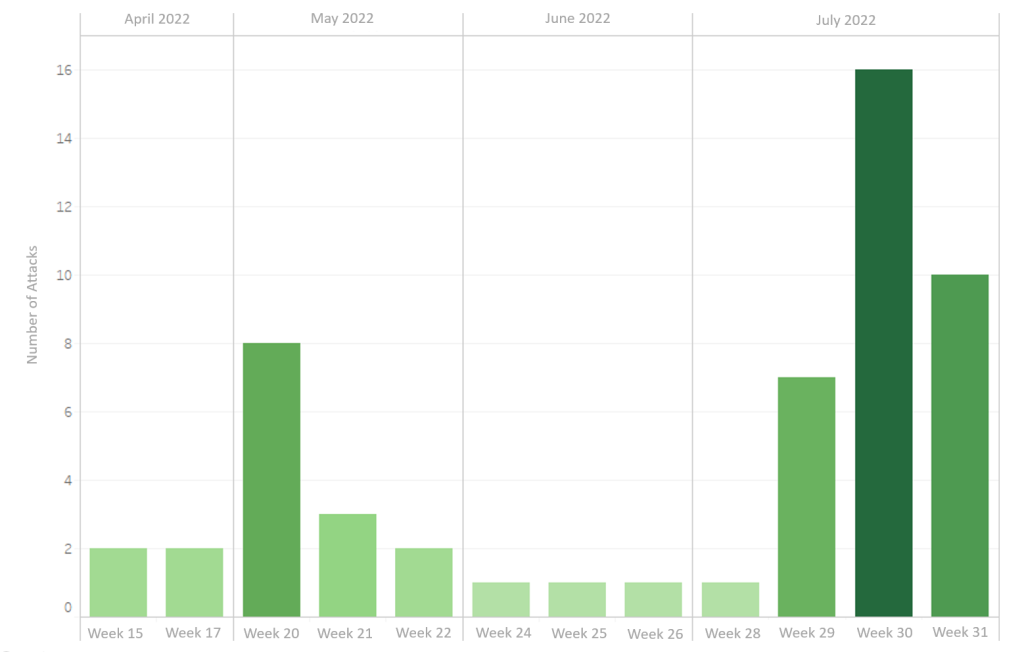
Taking the second type of attack activity using HTM and lnk attack chains as an example, we captured relevant samples since Q2’22, extracted the malicious lnk files, and plotted the following statistical chart with the file creation time as in the figure below:
Figure 1 Statistical chart of the frequency of the second type of attack activity
It can be found that throughout the second quarter, Gamaredon made less use of this type of attack method, with a higher frequency attacks in early May; while starting from the middle of July, Gamaredon significantly increased the frequency of lnk spear phishing attacks, with more than 10 such incidents observed every week.
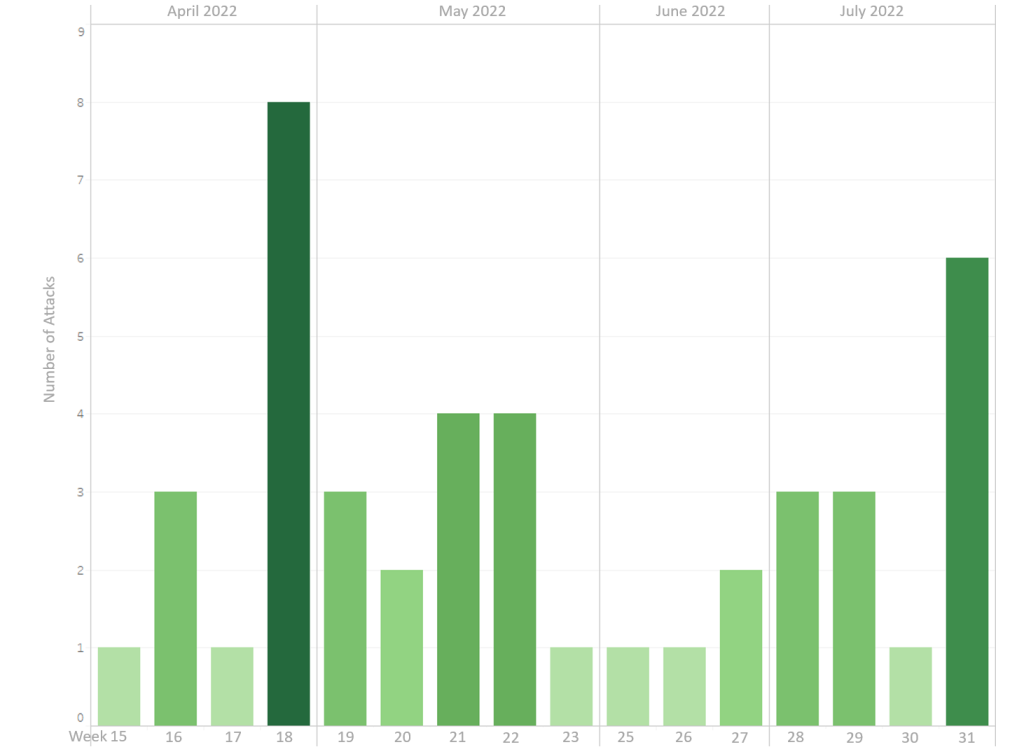
The third type of attack activity using SFX files exhibits similar variations. Based on the time appearance in the wild, the frequency of such activities is calculated as follows:
Figure 2Â Statistical chart of the frequency of the third type of attack activity
It can be found that, overall, the frequency of SFX decoys is relatively even, again with two peaks in late April and late July, which is more in line with the pace of the second type of attacks.
The above statistics show that Gamaredon significantly increased the frequency of cyber attacks against Ukraine in late July and used more military file information as bait, which can be judged as an intensive offensive against Ukrainian military targets.
Activity Analysis
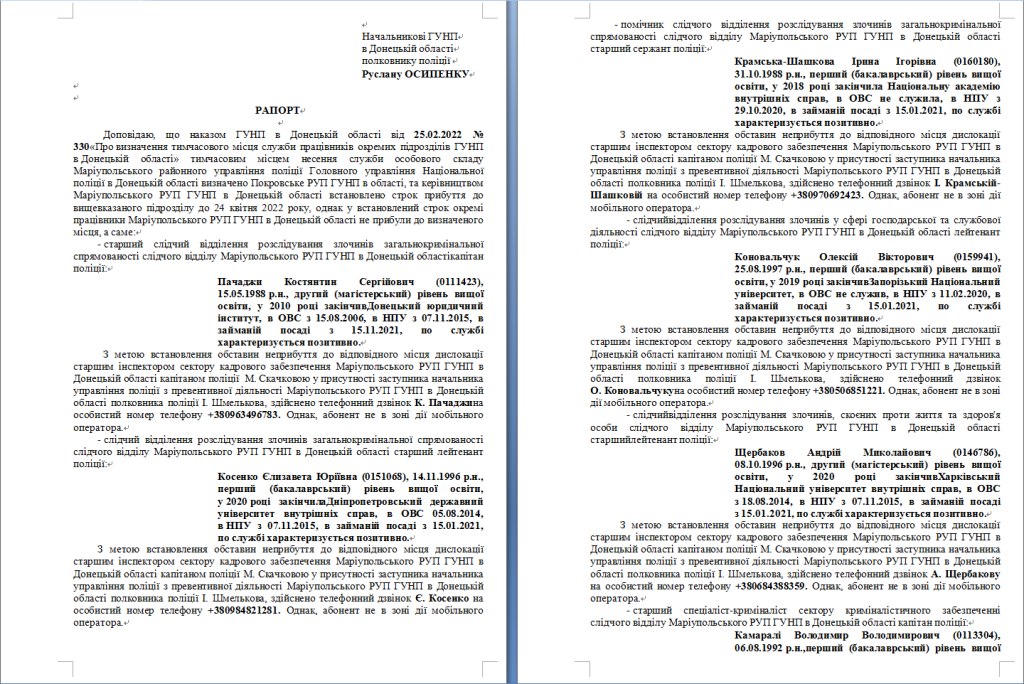
Type 1: Malicious documents disguised as police files
The main bait used by Gamaredon in such campaigns is a malicious document disguised as a Ukrainian investigation report. We found that most malicious documents of this type carry the content of common police documents such as duty records, police records, and processing reports, and are mainly used by Gamaredon to attack police officers in various regions of Ukraine.
A recently discovered document of this type, named “Ð ÐПОРТ МРУП 06.06.22.docx”, abuses the Office remote template mechanism and tries to obtain the malicious payload at the specified network location (shown below) when it is opened, and then run it.
http[:]//faithfully.glitter17.drowrang[.]ru/WIN-BDQQL5EO1F2/interested/naturalists/lowered/lowered/lowered.hr2
Observing the decoy text in the document, we can find that its direct target is the Police Station of Donetsk District in Ukraine.
Figure 3 Type 1 – A decoy document
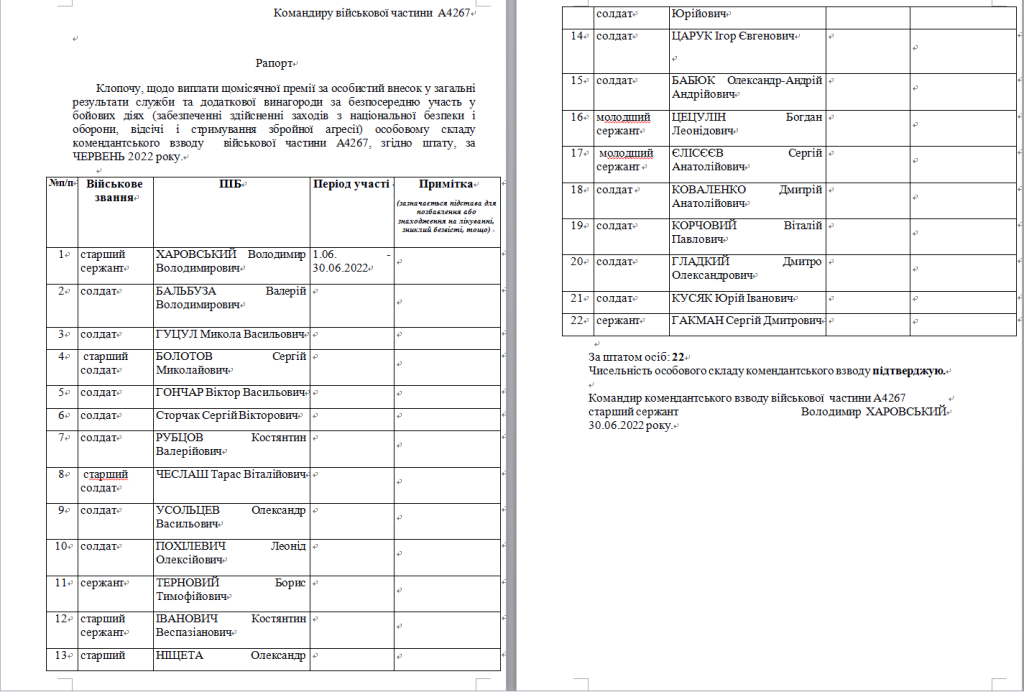
Other decoys of this type include a document called “ÐšÐ¾Ð¿Ð¸Ñ Ð—ÐРПЛПТРТравень 2022.docx”, carrying a malicious link of http[:]//enforce.interdependent23.vipertos[. ]ru/DESKTOP-STA1AO7/salmon/salmon.udb, which actually holds a multi-stage VBScript payload. The associated content indicates that the direct target of the decoy was A4267 unit of the Ukrainian Army’s.
Figure 4 Type 1 — Another decoy document
(To be continued…)