Executive Summary
OpenVPN is an application layer VPN implementation based on the OpenSSL library and serves over port 1194. In September 2019, OpenVPN was found to be vulnerable to UDP reflection attacks. This document analyzes threat exposure of the entire network, common attack means, and the bandwidth amplification factor (BAF) of reflection attacks via the entire network survey data from NSFOCUS Threat Intelligence (NTI) and threat data captured by NSFOCUS Threat Capture System.
Key findings of this document include:
The five countries that have employed the OpenVPN service and own the largest number of exposed assets are the United States, Germany, China, the United Kingdom and Italy in sequence.
According to the analysis of the log data that records the access to port 1194 captured by the NSFOCUS Threat Capture System from June 1, 2020 to August 10, 2020, daily logs captured range from several dozens to hundreds except for sudden burst on individual days. Therefore, we conclude that it is more a detection to the OpenVPN service rather than reflection attack attempts by exploiting the OpenVPN service.
Payloads captured by the NSFOCUS Threat Capture System mainly are 2 bytes (24.6%), 14 bytes (19.8%), and 1 byte (10.1%) in length.
We have evaluated the OpenVPN BAF in three methods: (1) We send a 14-byte payload and the test node replies with a 26-byte message. If no further responses are received, the node will send a 14-byte message every 2, 4, 8, 16 seconds. In this way, the average OpenVPN BAF will be 5.9. (2) We send a 2-byte payload and 51,161 IP addresses across the network have response to it, all of which are 26 bytes long. Then, some live IP addresses are randomly selected for verification. However, only one message is received, through which the average BAF is calculated as 13. (3) We send a 1-byte payload and only select several IP addresses for simplified verification. Similar to method 2, only one response message is received and the average BAF is calculated as 26. Considering returns of attacks, we determine that IP addresses that respond to 2-byte and 1-byte payloads impose more threats.
Some articles suggest configuring filtering rules on anti-DDoS devices or boarder routers to filter UDP data packages that are longer than or equal to 56 bytes and are sourced from port 1194. However, according to payloads captured by the NSFOCUS Threat Capture System and our analysis as well as verification, the rules should be improved and set as that only data packages longer than or equal to 14 bytes are filtered.
Analysis on Exposure of the OpenVPN Service
This section analyzes the exposure of the OpenVPN service based on the complete survey data obtained by NTI in May 2020.
About 750,000 IP addresses over the world have employed the OpenVPN service and are likely to be exploited for DDoS attacks.
The five countries that have employed the OpenVPN service and own the largest number of exposed assets are the United States, Germany, China, the United Kingdom and Italy in sequence.
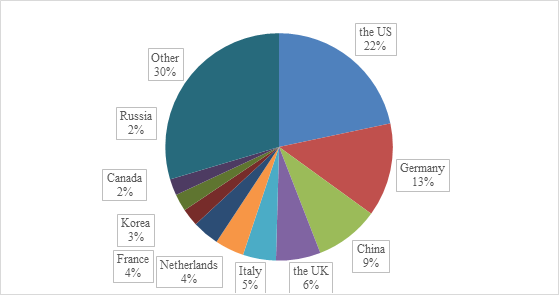
Figure 1.1.Countries of Assets Employing the OpenVPN Service
Analysis on OpenVPN Reflection Attacks
This section describes the current situation of OpenVPN reflection attacks based on analysis of log data captured over port 1194 by the NSFOCUS Threat Capture System from June 1, 2020 to August 10, 2020.
We have analyzed log data captured over port 1194 by the NSFOCUS Threat Capture System, as shown in Figure 2.1. It can be seen that daily logs captured range from several dozens to hundreds except for sudden burst on individual days. Therefore, we conclude that it is more a detection to the OpenVPN service rather than reflection attack attempts by exploiting the OpenVPN service.
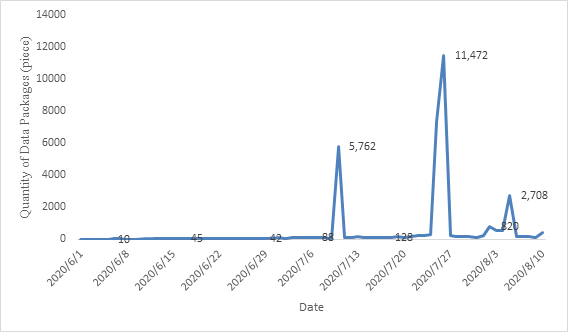
Figure.2.1 Trends of Access to the OpenVPN Service
We have collected statistics about payloads in log data received from port 1194 and have named the payloads by the length of the messages so as not to spread attacking messages. Figure 2.2 shows that attackers frequently use 2-byte, 14-byte, and 1-byte payloads, among which 14-byte payloads come in various types.
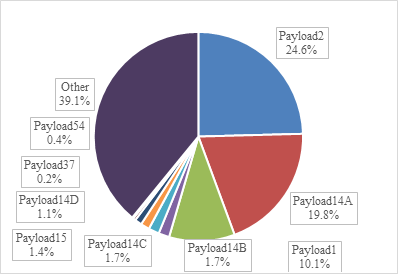
Figure 2.2 Proportion of Payloads Captured by the NSFOCUS Threat Capture System
 Rather than the 96-byte message mentioned by an article [1] of a peer vendor, we used the 14-byte message (Payload14A) that was adopted by the attack victim captured by the NSFOCUS Threat Capture System while doing the entire network survey for the OpenVPN service. That is to say, about 750,000 IP addresses will respond to the 14-byte message, which is consistent with the OpenVPN exposures mentioned in the peer vendor’s article. In this way, this message can be used as a service detection message. We have randomly selected 30 live IP addresses for verification and found the following OpenVPN response rule: OpenVPN responds with a 26-byte message at first and sends 14-byte messages every 2s, 4s, 8s, and 16s if no further response is given. See Figure 2.3. In this way, we can obtain the average bandwidth amplification factor (BAF) [1] [2] of 5.9 for OpenVPN. In addition, considering the fact that the shorter the length, the larger the reflection times, we have performed a survey on payload2. A total of 51,161 IP addresses have responded to it with average response package length of 26 bytes (non-OpenVPN services filtered out). Then, some live IP addresses are randomly selected for verification. However, only one message is received. By this method, we can obtain the average BAF of 13 for OpenVPN. We did not carry out any survey on payload1. However, a simplified verification on it yielded response packages of 26 bytes in length, indicating a BAF of 26. Considering returns of attacks, we determine that IP addresses that respond to 2-byte and 1-byte payloads impose more threats.
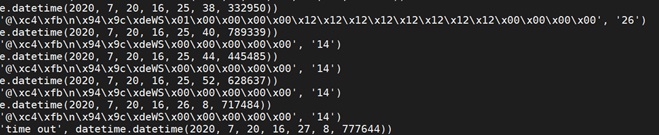
Figure 2.3 Response of a Test IP Address to Payload14A
Conclusion
This document analyzes threat exposure of the entire network, common attack means, and the bandwidth amplification factor (BAF) of reflection attacks via the entire network survey data from NSFOCUS Threat Intelligence (NTI) and threat data captured by NSFOCUS Threat Capture System.
Security vendors can:
Enable OpenVPN scanning on scannable products to detect security risks in customers’ networks in time.
Enable OpenVPN-oriented traffic detection on protective products to detect security threats in customers’ networks in time, and associate threat intelligence of IP addresses employing the OpenVPN service to prevent connection of targeted source IP addresses.
Telecom operators must comply with BCP38 Network Ingress Filtering.
Supervision organs must monitor OpenVPN threats in the network and notify related parties if they detected threats.
OpenVPN users should configure service access whitelist.
Users with the anti-DDoS requirement can purchase anti-DDoS products from security vendors that are capable to resist OpenVPN reflection attacks.
References
- https://www.freebuf.com/vuls/215171.html
- https://www.ndss-symposium.org/ndss2014/programme/amplification-hell-revisiting-network-protocols-ddos-abuse/
