After nearly 20 years of cloud computing development, we have stepped into the cloud native era. Cloud native technologies, exemplified by container, service mesh, and micro-service, are bringing disruptive changes to IT infrastructure, platforms, and application systems deployed for various sectors and are also permeating industrial Internet platforms with IT/OT convergence, 5G infrastructure with IT/CT convergence, edge computing platforms, and other emerging infrastructure.
Having a good understanding of cloud native’s new architectures, new risks, and new threats, we can work out an excellent security protection mechanism for new IT infrastructure. By integrating the advanced cloud native technologies, we are able to build a resilient, adaptive, and agile defense system to improve overall security protection.
What Is Cloud Native Security?
Like cloud computing security, cloud native security is broken down into two categories: security for cloud native environments and security with cloud native characteristics.
Security with Cloud Native Characteristics
Security with cloud native characteristics refers to all sorts of security mechanisms with cloud native traits like resilience, agility, light weight, and orchestration.
Cloud native is a conceptual innovation. It reshapes traditional development and operations systems to speed up business go-live and upgrade by means of microservice, containerization, and resource orchestration. Likewise, cloud native’s excellent traits will provide many useful insights for security vendors, inspiring them to reshape their security products and platforms and reform delivery and update modes.
Here we still use DDoS as an example. In the security system of a data center, anti-DoS is a typical security service mainly provided by cleaning hardware devices. The major disadvantage of this security mechanism is its inability to respond to massive DoS attacks as it is impossible to deploy additional cleaning hardware devices in a short time (the reason is that it usually takes weeks to go through the process of ordering, production, shipment, delivery, and go-live of hardware security devices) to deal with the DDoS traffic that goes beyond the total cleaning capacity of protection devices. This issue, however, could be solved by a cloud native security mechanism. With this mechanism, security vendors can deliver containerized virtual cleaning devices in the form of container images and leverage system orchestration to implement dynamic horizontal capacity expansion among idle servers to start enough cleaning devices to handle high-volume traffic. In this case, the cloud-native DDoS cleaning mechanism protects business systems that are, however, likely to be traditional ones.
Security for Cloud Native Environments
Security for cloud native environments refers to protecting security of infrastructure, orchestration systems, and microservices in cloud native environments.
This kind of security mechanism does not necessarily have cloud native characteristics (like containerization and orchestration), but can be deployed in a traditional manner or even a hardware device to protect increasingly prevalent cloud native environments.
The anti-DoS service for container as a service (CaaS) is a typical example of this mechanism. In this case, the DDoS mitigation mechanism can be used to protect the security of CaaS. Due to performance restrictions, this kind of mitigation mechanism is usually implemented by a hardware device to ensure the availability of cloud native systems.
In addition, host configuration security, repository and image security, behavior detection, border security, and the like are all security mechanisms for cloud native environments.
Cloud Native Security — Integrated Security
From the technical perspective, cloud native security falls into two categories. However, for cloud native security, it is imperative to adopt security technologies featuring cloud native to protect the security of cloud native environments. Therefore, the two kinds of technology are integrated during actual use.
Also, DDoS threats are still used as an example here. On the one hand, availability is an essential security attribute of the entire cloud native system, in consideration of the necessity to ensure the availability of hosts, containers, microservices, and serverless systems. On the other hand, to guarantee the availability of cloud native systems, on-demand scalable DDoS mitigation capabilities should be built at physical borders and a virtual and scalable DDoS protection mechanism should be deployed at borders of containers and microservices. All of these call for cloud native security capabilities. We can see that the two cloud native security technologies are equally indispensable and mutually complementary.
Why Is Cloud Native Security Important?
Currently, a host of attack incidents against cloud native have been discovered, including Docker/Kubernetes exposure, Tesla Kubernetes cluster cryptomining incident, container images in Docker Hub being poisoned by injecting a cryptominer, massive Kubernetes cryptomining incident discovered by Microsoft Azure Security Center, and Graboid worm cryptomining spreading incident.
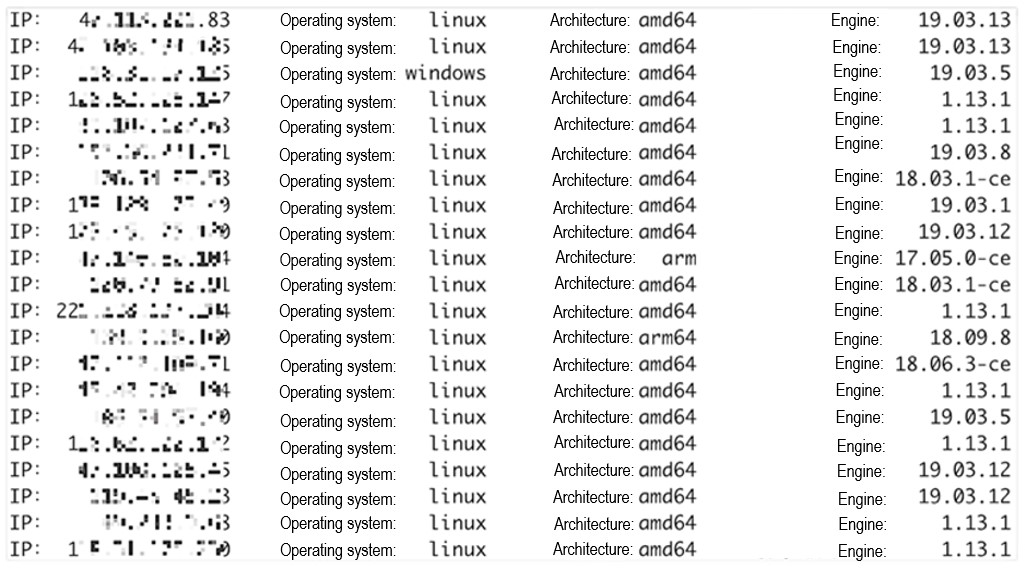
With the cyberspace search engine Shodan, we make an analysis of Docker daemon services exposing port 2375 on a specific day in October 2020 and find that approximately 4800 services make port 2375 publicly available and some allows direct interactions due to the absence of access authentication. Also, our contemporary statistics suggest that about 1200 Kubernetes Dashboard services are exposed on the Internet and some can be accessed without authentication. Undoubtedly, port exposure will put these services at risk.
On April 8, 2020, Microsoft Azure Security Center released a post to announce the detection of the massive cryptomining incident targeting Kubernetes[i].On June 10, 2020, this center published another article to warn against massive cryptomining incidents against Kubeflow[ii]. Microsoft’s two alarms sounded in just two months send a strong signal that cloud native systems, typically Kubernetes, are probably opening up a new channel for perpetrators to garner illegal profits.
The Kubeflow-targeting attack incidents affect dozens of Kubernetes clusters. As nodes used for machine learning in a Kubernetes cluster usually have more powerful computing capabilities than common servers, and such capabilities, once exploited by attackers, will bring considerable benefits for cryptomining.
In fact, malicious cryptomining is nothing new in containers as cryptomining activities are often seen in vulnerable containers. For instance, hackers exploit vulnerable web applications running in a container to take control of the container to deploy a cryptominer.
As cloud native comes into widespread use, security risks and threats facing it emerge constantly. Security has become an important influencing factor of the implementation of cloud native.
