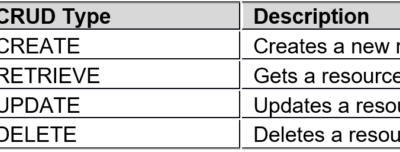
WAF REST API is known as the secondary development interface, and can be called by third-party platforms/software for adding, deleting, modifying, and querying WAF as wells its site, policy, and other configurations. Basic Conventions Format conventions: WAF REST API requests and responses are in JSON format: The attribute (primary key)...
Tag: knowledge base;
NIPS V5.6R10 Policy Matching Mechanism
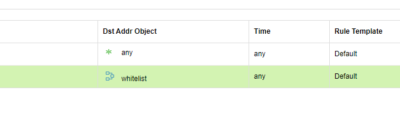
The NIPS policy matching mechanism is blocking first. That is, when traffic is matched against all policies, if one policy is matched whose action is set to block, traffic is blocked. When configuring IPS policies, it is recommended that they should not be overlapped. For example, security zones should not...
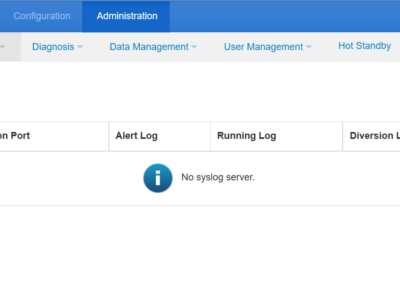
NSFOCUS NTA Syslog Introduction
Computer system designers may use syslog for system management and security auditing as well as general informational, analysis, and debugging messages. A wide variety of devices, such as printers, routers, and message receivers, across many platforms use the syslog standard. This permits the consolidation of logging data from different types...
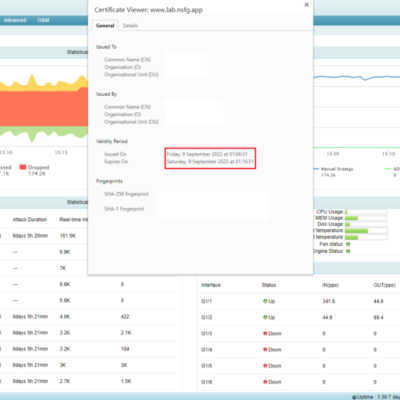
SSL Certificate Replacement on NSFOCUS ADS
A Secure Sockets Layer (SSL) certificate is digitally signed and issued by a trusted certificate authority (CA) to an organization for authentication of server identities and encryption of data in transit. Therefore, SSL certificates can protect user privacy and information security. For a website with an SSL certificate issued by...
NSFOCUS WAF Website Certificate Generation Method
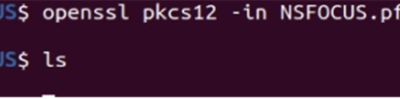
To protect HTTPS websites, the certificate used by these websites needs to be uploaded to NSFOCUS WAF. These certificates may be in different formats, such as .pfx, .crt, and .pem. NSFOCUS WAF, however, supports .cer certificates only. Therefore, the customer needs to extract the certificate information and private key from...
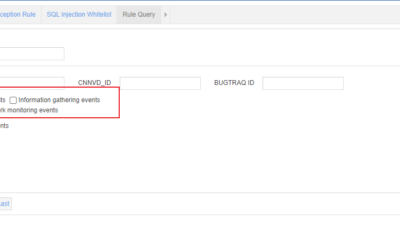
NIPS V5.6R10 Rule Types
NIPS V5.6R10 has five types of rules to detect DDoS attacks, local privilege elevation, information gathering, suspicious network behaviors, and network monitoring events, respectively. They are described as follows. 1. Information gathering Information gathering is the first step of network intrusion. Attackers use various methods to scan and probe target...