With the boom of the global digital economy, cybersecurity is converging with the Internet of Things (IoT), industrial Internet, cloud computing, and 5G, bringing about disruptive changes to security in various aspects, including traditional physical security, biological security, public security, and national security. Meanwhile, the attack surface keeps expanding in cyberspace as malicious attackers, larger in size, are well trained and organized to update its arsenal with automated intelligent attack technologies. In view of the current complicated situation, the traditional approach to deploy protective devices at network borders has gone out of date.
As the offensive-defensive battle is getting more intense, Security Operations (SecOps) is born to enable integration between personnel, techniques, and processes, facilitating collaboration of global security defense resources. Currently, SecOps has become the most direct and critical step to make the defense system work to its best when dealing with advanced threats.
Reflecting on the cybersecurity history composed of computer security, information security, cyberspace security, and digital security, we observe that for the conceptual evolution of the security industry, the core trend is that network informatization pushes forward the development of security technologies in each era. However, the attack surface keeps expanding in cyberspace as malicious attackers, larger in size, are well trained and organized to update its arsenal with automated intelligent attack technologies. In view of the current complicated situation, the traditional approach to deploy protective devices at network borders has gone out of date. As offensive/defensive battles keep escalating, the traditional security defense solution focusing only on security borders is gradually being replaced by a more mature and complete sliding-scale protection approach. Shift left of border defense is a systematic intrinsic security mechanism, while shift right is intelligence-driven proactive defense. Thanks to its features such as zero trust, threat capture, threat hunting, security development, and security operations, the intrinsic proactive defense approach has become a widely recognized solution in the security industry. For both shifts left and shift right, SecOps has increasingly become a must-have security capability.
SecOps is intended, via processes, technologies, and services, to provide enterprises and organizations with vulnerability identification and management and threat detection and response among other security capabilities, in an effort to ensure effective control of security risks[i]. Conceptually, the core of SecOps is management of risks that needs to be measured in a dynamic, continuous, and relative way.
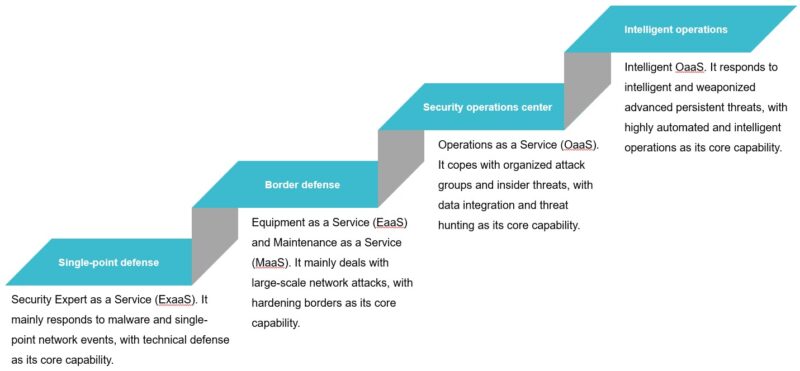
Since security operations is driven by risks, it evolves with progressive risk perception. Overall, going through the single-point defense, border defense, and security operations center phases, security operations finally moves towards intelligent operations.
- Single-point defense: With the advent of the Internet era, malware targeting personal computers first emerged. The threat trend of the Internet world gradually entered the public view. With malware looming largest among other security risks, numerous security experts were engaged in antivirus software research. The concept of SecOps has yet taken shape, security capabilities are delivered typically as Expert as a Service (ExaaS).
- Border defense: For the sake of financial gains, attacks and threats have gradually become organized and industrialized. At the same time, a great number of software vulnerabilities are exposed with the rapid evolution of large-scale Internet services and IT system software. In response, NSFOCUS Anti-DDoS System (ADS), NSFOCUS intrusion Detection System (NIDS), and NSFOCUS Remote Security Assessment System (RSAS) were launched to quickly build the network border protection system. With the deepening of attack and defense research and fast iteration of threat scenarios, security operations makes rapid progress, penetration testing and risk assessment teams are set up, thus forming the prevailing Equipment as a Service (EaaS) and Maintenance as a Service (MaaS).
- Security operations center: The emergence of advanced persistent threats (APTs) and relevant events have brought a huge impact on border defense. Multi-layered security policies and regulations are combined to form compliance requirements. The aggregation of multiple factors leads to radical changes in the whole cybersecurity cognition. It has become a consensus in the industry to conduct normalized, collaborative, in-depth, and intelligent defense. The SecOps concept and architecture have gradually taken shape, and security operations centers (SOCs) have flourished everywhere. SOCs manage threats, vulnerabilities, assets, and other risk-related procedures and data in a centralized manner and adopt such advanced security technologies as behavior analysis, honeynet capture, threat hunting, and intelligence fusion so as to improve the security operations efficiency. Operations as a Service (OaaS) is becoming a critical trend for cyberspace protection. Against this background, the Continuous Adaptive Risk and Trust Assessment (CARTA) architecture and concept are popularized.
- Intelligent operations: The security operations team plays a central role for centralized running of SecOps. The development process of SecOps reflects the upgrade of technologies and interpersonal confrontation. Currently, as the data volume grows explosively and technologies become more complicated, attackers and defenders are fighting increasingly arduous battles, but on the defensive part, the current human capacity is far from sufficient to achieve risk control objectives. In view of key features of the digital era, a major breakthrough should be made to cybersecurity operations that merely depend on security experts. In this context, making security operations techniques and processes more automated and intelligent has become a prerequisite for cybersecurity risk governance and control. Intelligence-empowered security operations provide a solid foundation for OaaS in the digital era.
Intelligent security operations has become an inevitable trend. More and more technologies including traffic analysis, behavior analysis, sample analysis, threat association, and automated response use machine learning algorithms, graph algorithms, and reinforcement learning algorithms. Even so, the development level of security intelligence still cannot satisfy security operations requirements in threat discovery timeliness and accuracy, automated event traceback, and risk decision-making automation. There is still a long way to go before AISecOps services are mature.
For security operations, the difficulty in analyzing massive data comes from the imbalance between attacks and defense. In the cyberspace where defenders fight against attackers hiding in the dark, collection and analysis of massive data are a prerequisite for AISecOps. Processing massive data has posed unprecedent challenges to security operations teams that might be haunted by dependence explosion, alert fatigue, and threat identification from too many events. Due to technological bottlenecks, lack of skilled professionals, and less operable processes, security operations eventually cannot work out for the best. The following figure displays a threat analysis system framework that Is based on terminal traceback data and involves multiple data processing and analysis modules. Critical technological challenges brought by big data in security operations can be summarized as follows:
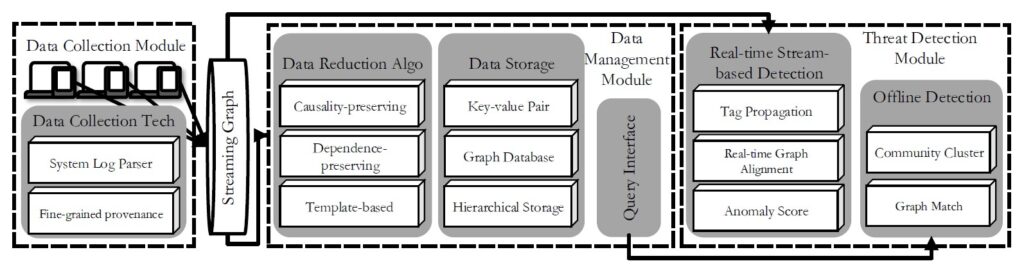
- Data access: data expansion and system bottlenecks. Explosive growth of security operations data places unparalleled performance pressure on the network, storage system, and processing system.
- Data fusion: multisource heterogeneity and ontology modeling. Due to the lack of a uniform graphical model design for multisource and multidimensional data, it is urgent to form associable data views via ontologization and standardization.
- Clue discovery: retrieval models and a high rate of false positives. For instance, anomaly detection models tend to have a high rate of false positives due to the lack of contextual support for threat events retrieved by using key signatures or patterns.
- Event deduction: semantic fuzziness and dependence explosion. Data-driven analysis methods usually lacks security semantics modeling or the analysis of causal relationships involved in data dependence.
- Human-machine collaboration: black-box models and low interaction. Opaque and complex models and operations platforms featuring low interaction or even no interaction reduce the effectiveness of human-machine collaboration during security operations.
- Intelligent engine: attack expiration and data risks. As more attacks are targeting intelligent models, the security robustness of models should be increased to prevent model data theft.
Predictably, as more proven technologies are used for collection and intelligent analysis of security big data, the advent of the AI-based Security Operations (AISecOps) method greatly streamlines threat detection, risk assessment, automated response, and other critical operation phases, in sharp contrast to traditional solutions with overdependence on experts’ experience. This method significantly lowers overall security risks facing critical information infrastructure and data assets of enterprises, organizations, and even the whole country. However, for AISecOps currently in its infant stage, systematic reviews and combings need to be done for its system architecture, evaluation methods, data integration, and technological direction.
Stay tuned for the next blog: AISecOps Technology and System
[i] Security Operations Primer for 2020, Gartner, https://www.gartner.com/en/documents/3978969/security-operations-primer-for-2020
[ii] Li Z, Chen Q, Yang R, et al. Threat Detection and Investigation with System-level Provenance Graphs: A Survey[M]. arXiv preprint arXiv:2006.01722, 2020