Activity of Attack Sources
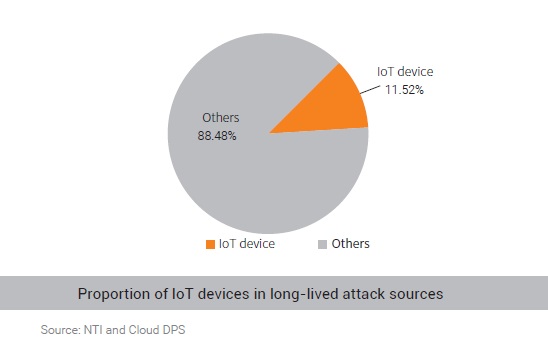
Ongoing monitoring of attack sources reveals that 90% of them were active for no longer than 10 days. There were two reasons behind this. For one thing, in order to keep attack sources fresh
and prevent them from being blacklisted by defenders, attackers tended to use the hit-and-run strategy. For the other, there were a lot of vulnerable IP addresses widely distributed on the Internet, which could be easily obtained at a very low cost. Moreover, the proportion of IoT devices in attack sources that were active for more than 10 days rose sharply to 11.5%.
Geographical Distribution of Active Attack Sources
Based on the activity duration, attack sources active for over 10 days are regarded to be highly active. These IP addresses often contain obvious and easily exploitable security hazards that can pose very severe threats.
Globally, highly active attack sources were mostly distributed in China, the UK, and the US. In China, they were mostly found in coastal provinces and economically developed regions, such as Zhejiang, Jiangsu, Guangdong, and Shandong. With a larger base of infrastructure, networks in these regions are more vulnerable than in other regions, provided that the same level of protections is deployed, because of hosting a much larger number of potentially vulnerable devices.
“Recidivist” Attack Sources
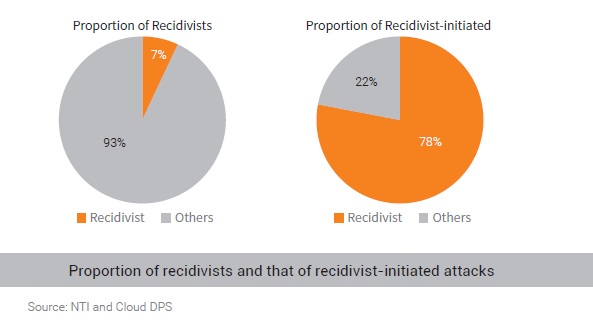
In 2019, 7% of recidivists5 were responsible for 78% of DDoS attacks. Obviously, recidivists are too menacing to overlook.
Anomalous Behavior
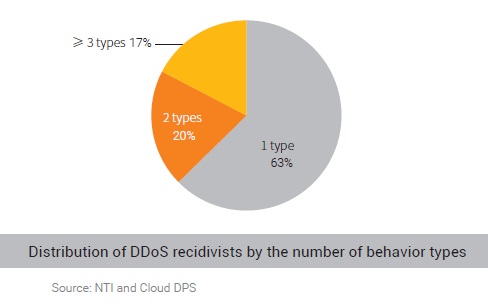
Compared with 2018, attack resources used in DDoS attacks were involved in more types of activity in 2019. Of those resources, 39% had engaged in several types (up to 8) of anomalous activity in 2019.
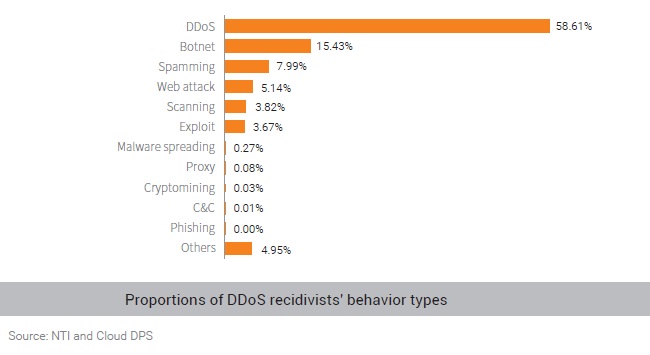
According to proportions of DDoS recidivists’ behavior types shown in the following figure, 15.43% of attack sources were controlled by botnets; 7.99% were found in spamming; 58.61% were marked by NTI as to have repeatedly conducted DDoS attacks because they contained vulnerabilities that could be remotely controlled and were left unfixed for a long time, or because they had the reflection capability.
Analysis of Attack Group Behaviors
The previous analysis finds that 7% of DDoS recidivists were responsible for 78% of attack events. However, DDoS attacks are usually launched collaboratively from multiple sources. That is to
say, several groups of DDoS recidivists often work together to initiate attacks. Such groups are collectively referred to as an “IP gang”. In this report, through analysis of DDoS attack data collected
by NSFOCUS in 2019, we have identified multiple IP gangs and done a systematic research on their behavior.
The principle behind our research method is that IP addresses with similar historical attack behavior will be assigned to an IP gang. The behavior similarity is reflected in the following aspects:
1. Behavior similarity in a short time: hitting the same target again and again using the same attack means at the same time.
2. Behavior similarity in the long run: hitting the same target repeatedly using the same attack means in different periods.
In this section, we make a statistical analysis of behavior of IP gangs, profile major ones, and find that IP gangs have the following characteristics:
1. Of recidivists carrying out activities as IP gangs, 17% are IoT devices. This means that IoT devices found in DDoS attacks as attack sources remain active for a long period of time and a large proportion are identified as recidivists. Besides, such devices tend to possess characteristics of gangs performing attacks.
2. For the largest gang with the most attack sources, IoT devices account for 31%, of which 64% are routers (94% from MikroTik).
3. The second largest gang in terms of attack source quantity includes 23,000 recidivists and produces the largest attack traffic. For the recidivists, the most notable characteristic is that they are skilled in the use of volumetric SYN flood attacks as 99.54% of them have resorted to this kind of attack according to historical attack records. For attacks launched in 2019, the peak attack traffic stands at above 100 Gbps for 60 days, with the maximum hitting 780 Gbps.
To be continued.