Insights into Vulnerabilities
4.1 Overall Trend
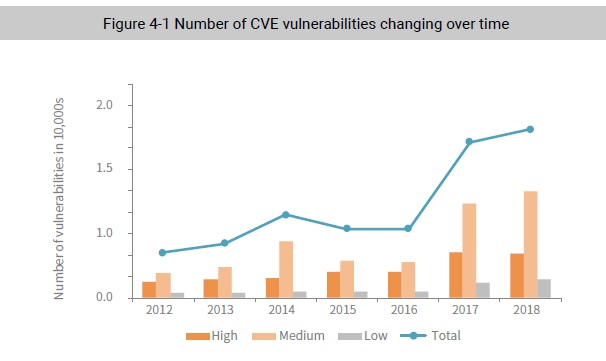
The National Vulnerability Database had recorded 15,800 CVE vulnerabilities for 2018, including 4096 high-risk ones. Compared with 2017, the total number of vulnerabilities found in 2018 increased 8.2%, while the number of high-risk ones dropped by 4.8%. Although the number of vulnerabilities increased steadily, they did so slowly, possibly due to some sources reporting vulnerabilities being more reluctant due to potential prosecution and a large number of vulnerabilities not being officially recorded.
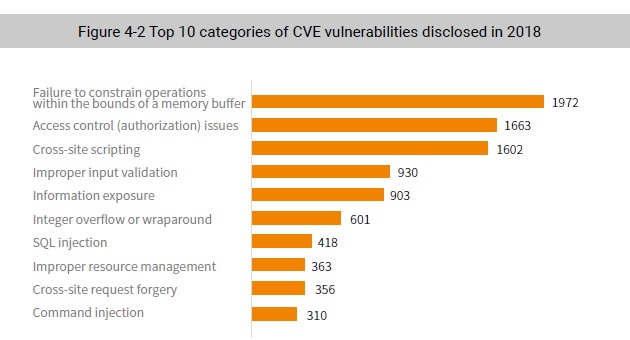
The following figure lists top 10 categories, as classified by Common Weakness Enumeration (CWE), of vulnerabilities disclosed in 2018.
The Top 5 vulnerability categories listed above are:
- CWE-119/125 Failure to constrain operations within the bounds of a memory buffer. By exploiting this type of vulnerability, a hacker can gain privileges for executing arbitrary code,
which may cause a system crash. Related vulnerabilities are mainly found in device firmware, operating systems, Office, PDF, and other software. Such software has high requirements for
performance and the vast majority is developed in C or C++. Vulnerabilities of this category discovered in 2018 were the largest proportion (1972), including approximately 40% of all highrisk
ones. - CWE-264/284 Access control (authorization) issues. Vulnerabilities of this category are closely related to specific services, including unauthorized access and privilege escalation,
which are often seen in server operating systems, database applications, and content management systems (CMSs). Of the 1663 such vulnerabilities disclosed in 2018, the vast
majority were medium-risk ones. - CWE-79 Cross-site scripting. This category does not seem so dangerous, but a lot of vulnerabilities disclosed in 2018 were related to it. They are especially common in various website building systems and are almost impossible to protect against effectively. When exploited together with other categories of vulnerabilities, they may contribute to sophisticated attacks, through which attackers can gain system privileges.
- CWE-20 Improper input validation. By using malformed input, hackers can cause errors to programs for the ultimate end of controlling, stealing data from, or paralyzing devices.
- CWE-200 Information exposure. An attacker can exploit such a vulnerability to disclose sensitive information. If contained in device firmware, these vulnerabilities can render access
control ineffective, leading to compromise of devices. An example of such vulnerabilities is the D-Link device firmware vulnerability (CVE-2018-10106).
To be continued.