Techopedia – Cybersecurity has been a key topic in IT for years and each and every year brings new challenges. Hackers develop new and more sophisticated ways to access data, resources and an increasing number of other things that are now found in the cloud, leaving cybersecurity professionals to defend...
Category: NSFOCUS in the News
The Merkle, Top 4 Cybersecurity Predictions for 2017
The Merkle – Even though there has been a strong focus on cybersecurity throughout 2016, the year 2017 will be a defining moment for online security. Experts have weighed in what we are most likely to encounter in the cyber world over the coming months, and things are not looking...
Who’s on Your IT Security Dream Team?
Computerworld - Getting the gang together. Last month, I presented you a chamber of horrors—the worst people you meet doing IT security, many of them your friends and, sadly, co-workers. But I don't like to dwell on the negative! So I asked a slew of IT pros about the best...
The Real Hacker Threat to Election Day? Data Deception and Denial
Wired - Hacks, data leaks, and disinformation have all added to the chaos of one of the most contentious elections in history. US intelligence agencies have even accused Russia of perpetrating some portion of the digital meddling. And now reports indicate that officials are preparing for worst-case cybersecurity scenarios on...
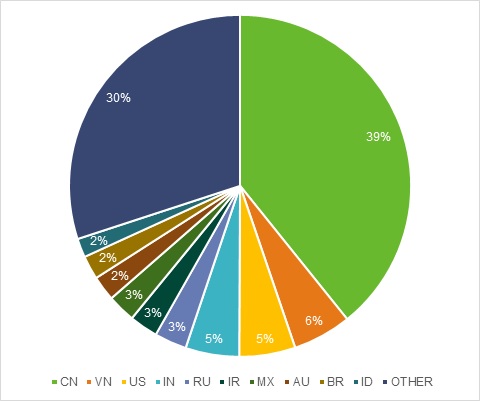
Massive DDoS Attacks Disable Internet Access Throughout Liberia
eSecurity Planet - British security researcher Kevin Beaumont recently reported that a series of massive cyber attacks using the Mirai DDoS botnet periodically disabled all Internet access throughout the country of Liberia. "Liberia has one Internet cable, installed in 2011, which provides a single point of failure for Internet access....
The Myth Of Threat Intelligence In The Channel, And An Intelligent Hybrid Security Approach
Business Solutions Magazine - Over the last year, Threat Intelligence (TI) has become a hot topic for the cybersecurity industry. Organizations of all sizes are looking to the channel to provide recommendations on what to purchase, how to implement, and how to gain the greatest value from TI. It is...