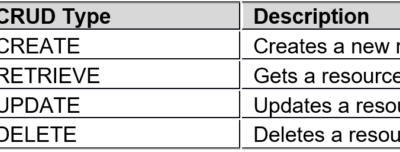
WAF REST API is known as the secondary development interface, and can be called by third-party platforms/software for adding, deleting, modifying, and querying WAF as wells its site, policy, and other configurations. Basic Conventions Format conventions: WAF REST API requests and responses are in JSON format: The attribute (primary key)...
Category: WAF
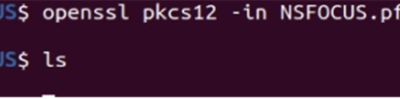
NSFOCUS WAF Website Certificate Generation Method
To protect HTTPS websites, the certificate used by these websites needs to be uploaded to NSFOCUS WAF. These certificates may be in different formats, such as .pfx, .crt, and .pem. NSFOCUS WAF, however, supports .cer certificates only. Therefore, the customer needs to extract the certificate information and private key from...
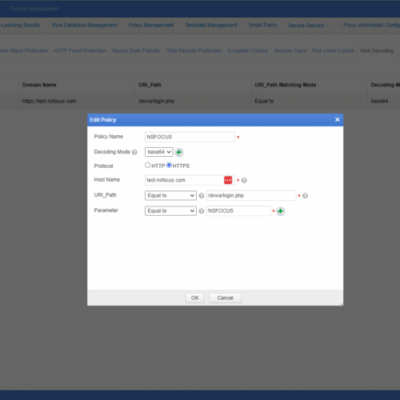
Introduction to NSFOCUS WAF Web Decoding Function
WAF web decoding function can decode base64-encoded data. After that, WAF performs attack detection by identifying attack signatures and provides prevention. The web decoding function is configured per website. Web Decoding Configuration Step 1. Choose Security Management > Website Protection, select a website group, click Web Decoding, and then click...
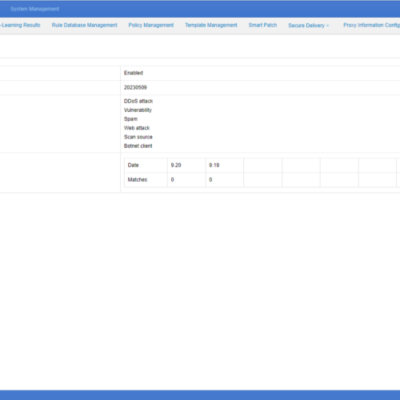
NSFOCUS WAF IP Reputation Introduction
NSFOCUS WAF obtains IP Reputation Data Feed from NSFOCUS Threat Intelligence (NTI). NSFOCUS WAF IP Reputation can get the list of IP addresses that have earned a negative reputation through involvement in suspicious activity, including phishing attacks, spam, botnets, DDoS attacks, APT attacks, and more. NSFOCUS WAF will filter high-risk...
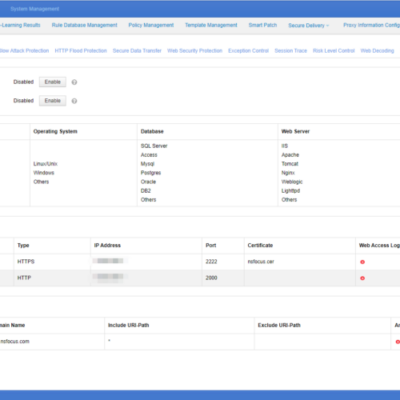
NSFOCUS WAF Secure Data Transfer
NSFOCUS WAF secures data transmission by restricting domain names, URLs, and request methods, and it can improve transmission security by converting ordinary HTTP requests into HTTPS requests forcibly. Configuration precondition: Configure HTTP and HTTPS sites and ensure that both HTTP and HTTPS sites can be accessed. Configuration method: Step 1:...
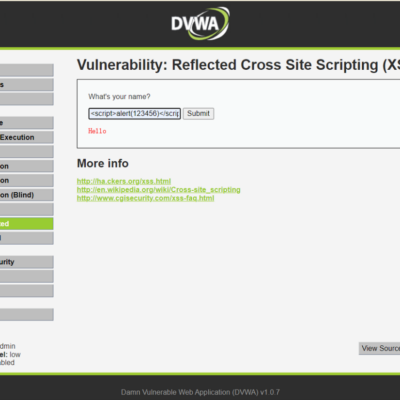
XSS Attack Protection
Cross-Site Scripting (XSS) attacks are a type of injection in which malicious scripts are injected into otherwise benign and trusted websites. XSS attacks occur when an attacker uses a web application to send malicious code, generally in the form of a browser side script, to a different end user. Flaws...