An HA switchover is initiated when: A manual switchover is performed. The slave NTA does not receive any keepalive packet from the master NTA within the specified period. The master NTA engine works improperly. The link of the VRRP group interface is down. The master NTA interface is down. The...
Category: Knowledge Base
Troubleshooting of Failure to Import a License into NSFOCUS ADS
After ADS is installed, you must import a license before using it. License types vary a bit for hardware devices and virtual devices: Hardware device: License types include Trial, Temporary Sales, and Perpetual. Virtual device (vADS): License types include Trial, Temporary Sales, Perpetual, and Subscription. ADS will provide limited functions...
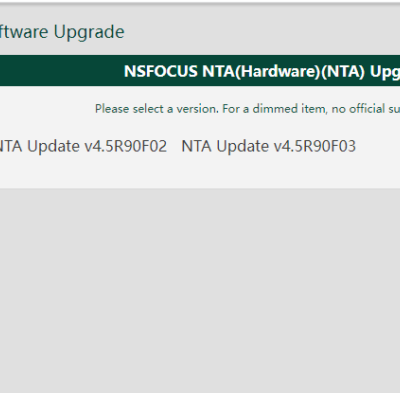
New Feature – Upgrade of Detection Rules via the Cloud in NTA V4.5R90F04
Function Description This function will be available in NTA V4.5R90F04 in Q2 2023. NTA allows online upgrades of the DDoS detection rule library for automatic protection. This function can meet most of the current customization requirements by providing the latest detection rules against new types of DDoS attacks. Configuration Procedure...
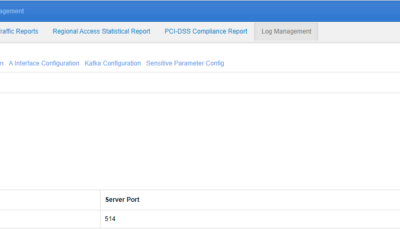
NSFOCUS WAF Syslog Introduction
In computing, syslog is a standard for message logging. It allows separation of the software that generates messages, the system that stores them, and the software that reports and analyzes them. Each message is labeled with a facility code, indicating the type of system generating the message, and is assigned...
Introduction to NSFOCUS WAF REST API
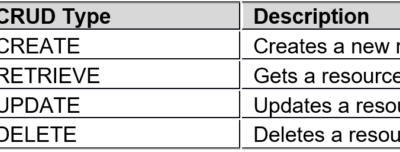
WAF REST API is known as the secondary development interface, and can be called by third-party platforms/software for adding, deleting, modifying, and querying WAF as wells its site, policy, and other configurations. Basic Conventions Format conventions: WAF REST API requests and responses are in JSON format: The attribute (primary key)...
NIPS V5.6R10 Policy Matching Mechanism
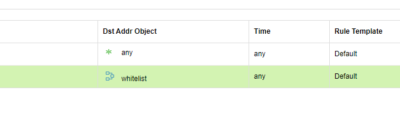
The NIPS policy matching mechanism is blocking first. That is, when traffic is matched against all policies, if one policy is matched whose action is set to block, traffic is blocked. When configuring IPS policies, it is recommended that they should not be overlapped. For example, security zones should not...