Overview Recently, NSFOCUS CERT detected that JumpServer issued a security announcement and fixed two remote code execution vulnerabilities. At present, the PoC of the vulnerability has been made public. Affected users should take protective measures as soon as possible. CVE-2024-29201: Since the Ansible module in JumpServer does not perform complete...
Category: Emergency Response
XZ Utils Backdoor Vulnerability (CVE-2024-3094) Advisory
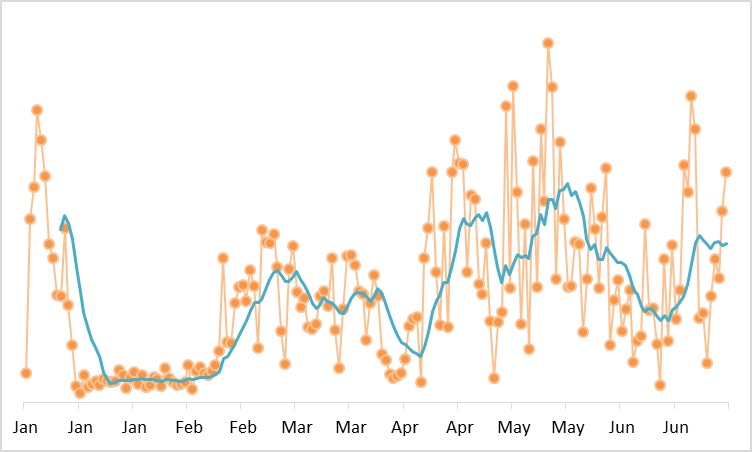
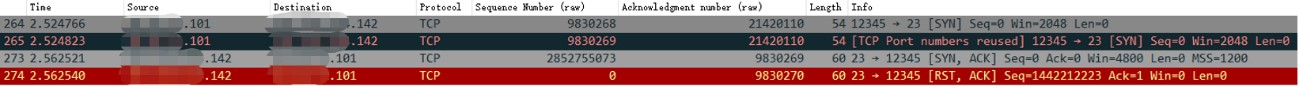
Overview NSFOCUS CERT recently detected that a backdoor vulnerability in XZ Utils (CVE-2024-3094) was disclosed from the security community, with a CVSS score of 10. Because the SSH underlying layer relies on liblzma, an attacker could exploit this vulnerability to bypass SSH authentication and gain unauthorized access to affected systems,...
Linux Kernel Privilege Escalation Vulnerability (CVE-2024-1086) Alert
NSFOCUS CERT has detected that details and a proof-of-concept (PoC) tool for a Linux kernel privilege escalation vulnerability CVE-2024-1086, have been publicly disclosed recently. Due to a use-after-free vulnerability in the netfilter: nf_tables component of the Linux kernel, the nft_verdict_init() function allows the use of positive values as a drop...
Atlassian Confluence Path Traversal Vulnerability (CVE-2024-21677) Notice
Overview Recently, NSFOCUS CERT detected that Atlassian issued a security announcement and fixed the directory traversal vulnerability in Confluence Data Center and Server (CVE-2024-21677), with a CVSS score of 8.3. Unauthenticated attackers need to interact with users, and exploiting this vulnerability can have a great impact on the confidentiality, integrity,...
Runc Container Escape Vulnerability Alert
Overview Recently, NSFOCUS CERT detected that the runc officially issued a security notice and fixed a container escaping vulnerability (CVE-2024-21626). Since the internal file descriptor of runc is leaked during initialization and the final working directory is not verified to be located in the mount namespace of the container, attackers...
Jenkins Arbitrary File Read Vulnerability (CVE-2024-23897) Notice
Overview Recently, NSFOCUS CERT detected that Jenkins issued a security announcement and fixed an arbitrary file reading vulnerability in the Jenkins CLI (CVE-2024-23897). Since one function of its CLI command parser is enabled by default in Jenkins, the specific parser function expandAtFiles can replace the character following the file path...