3.5 Delivery and PropagationÂ
3.5.1 Behavior SeenÂ
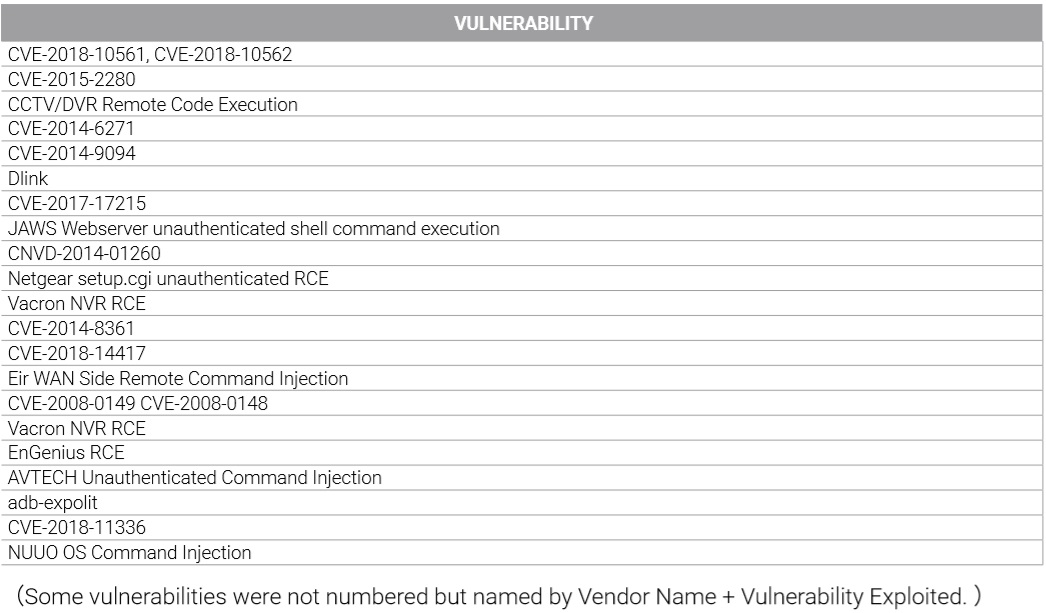
Studying 25 million intrusion logs extracted from NSFOCUS managed services customers in 2018, we found that approximately 14 million logs recorded intrusions using weak password cracking mainly against Telnet, RDP, and SSH services. From other logs, a large portion of intrusions seen were vulnerability-based intrusions, with 54 vulnerabilities frequently exploited (Shown in the table) mostly against routers and IoT cameras.Table 1 Frequently Exploited Vulnerabilities
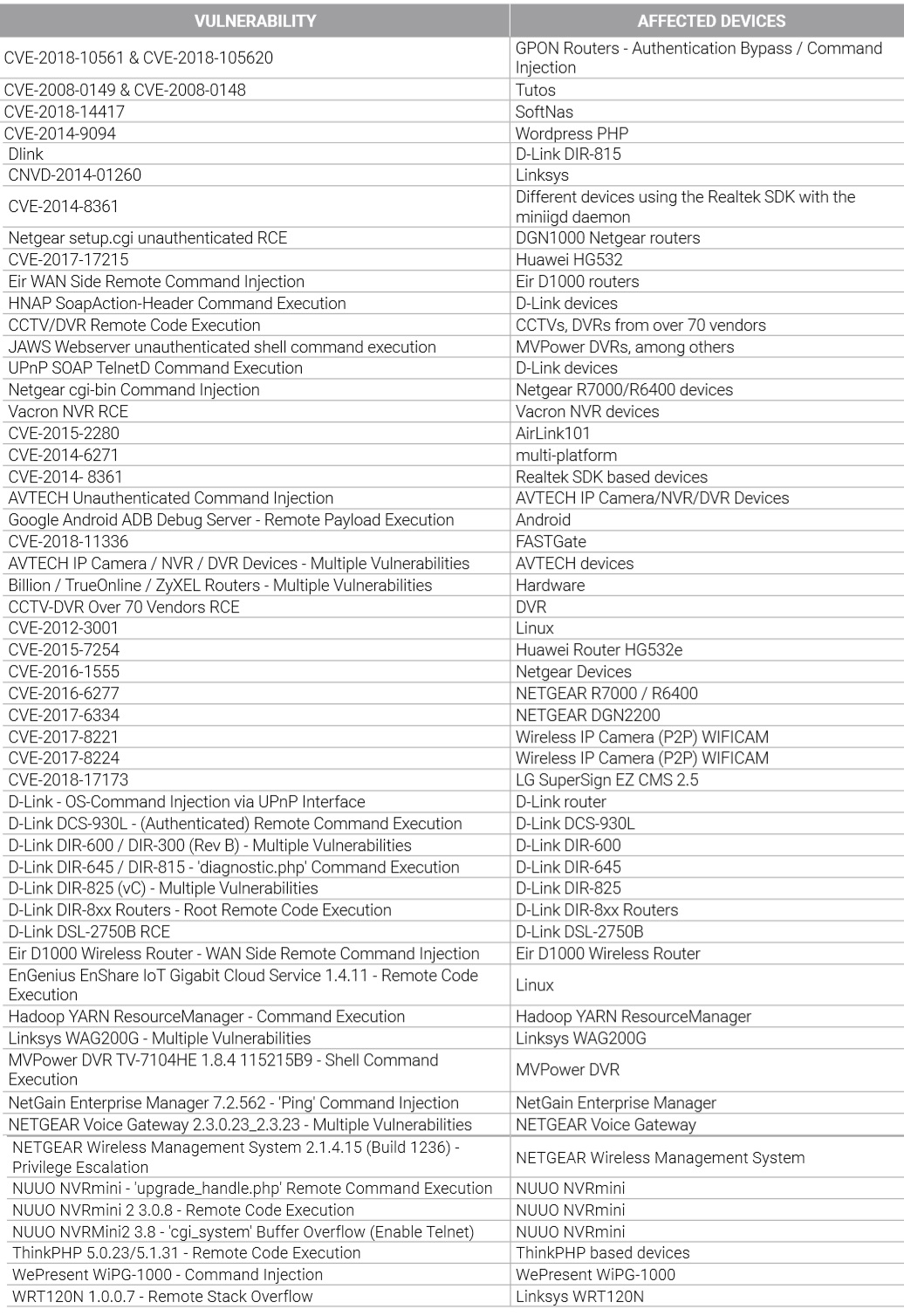
All vulnerabilities listed in the previous table were exploited by botnet families that have been seen across different platforms. Variants from the very active Gafgyt family carried out a total of 43 vulnerability exploits4. One strain of OrkSec, a Mirai variant botnet discovered in H2 2018, exploited 22 vulnerabilities.
Table 2 Vulnerabilities Exploited by OrkSec
3.5.2 AnalysisÂ
New Platforms with Poor Security Fueling Botnet Spreading
Traditional attacks using weak password scanning and social engineering are unable to meet the demand requiring the rapid growth of botnets. Instead, more and more malicious programs are using modules that can exploit dozens of vulnerabilities to first gain a foothold into an environment and then quickly spread to nearby platforms that have not been properly patched or maintained.
Malicious programs usually spread through the following techniques:
• Using spam to trick users into clicking an eye-catching malicious link
• Deploying malware on user’s computers by browsing or being redirected to a malicious webpage
• Masquerading as a normal software patch update
• Exploiting poor passwords
• Exploiting vulnerabilities in systems or platforms to gain privileges
The first three usually required some type of manual intervention affected by social engineering to turn a host into a zombie bot. However, as users become more security conscious those methods become less effective.
Today, attackers exploit default passwords and vulnerabilities as a more effective way to propagate bots. This makes IoT platforms with multiple security vulnerabilities the primary victims. Common IoT devices such as routers and cameras, once configured, stay permanently online and often lack timely updates. Since IoT devices may not be updated for months, even years, they have a high probability of being exploited. The incredibly fast spread of the Mirai virus is a testament to that. Hundreds of thousands of IoT devices have been compromised to date and are becoming a dire threat to public networks.
Much more attention is needed from not only IoT developers, but security researchers and end users as well. Users should ensure their devices are better secured by updating drivers, applying patches to fix vulnerabilities where possible, and changing default passwords immediately. Developers should be more responsible for fixing issues with their products and setting good default security controls. The state of California has recently passed new laws to ensure IoT vendors be more responsible. Security researchers should identify how to enhance security protections for IoT platforms to better defend against invasion and exploitation, especially with the historically poor security practices of both users and developers.
Â
4ï¾ For detailed description of the IoT Botnet Gafgyt family, see Gafgyt: The choice for IoT Botnets.
To be continued.