3.3 Geographical Distribution
3.3.1 Behavior Seen
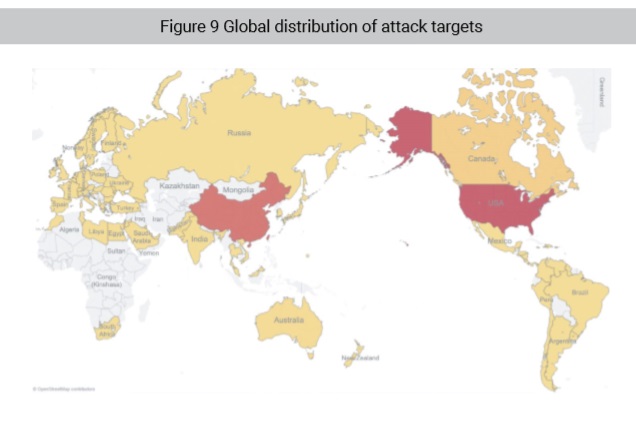
According to geographical analysis of IP addresses, 2018 saw most new C&C servers in the USA (30.64%), closely followed by China (29.79%). Other top C&C hosting countries include Canada, Russia, Germany, France, and Italy.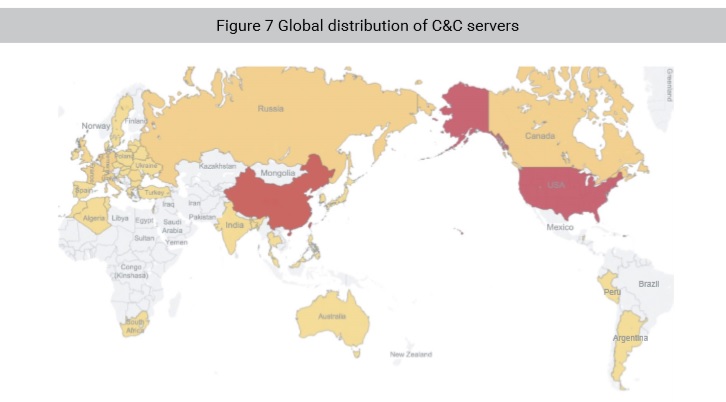
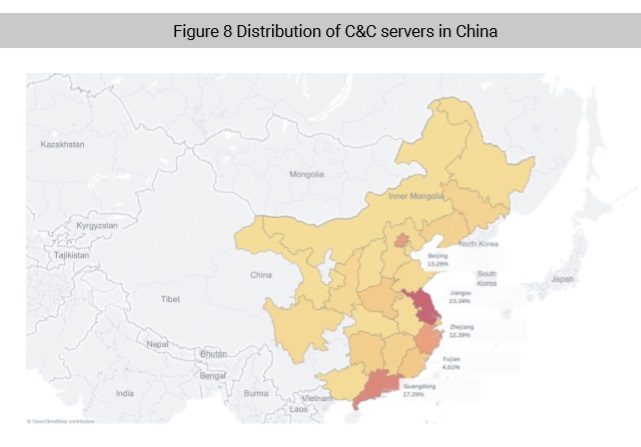
In China, most C&C servers were scattered along the eastern coastal area, with over 60% located in Jiangsu, Guangdong, Beijing, and Zhejiang.
In terms of the distribution of botnet attack victims, the USA (47.2%) and China (39.78%) were two worst-hit countries. Canada, Japan, and Australia were also affected by botnet attacks.
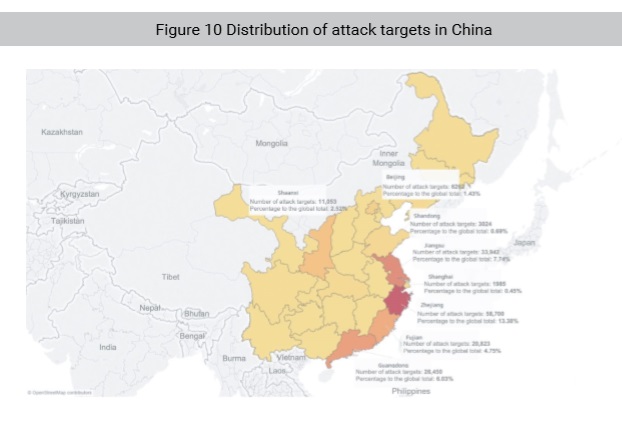
In China, botnet attacks mainly targeted economically developed provinces and municipalities such as Jiangsu, Zhejiang, Guangdong, and Beijing, where C&C servers are densely distributed, and all sorts of attacks are active. It is worth noting that Shaanxi became a new favored attack target in central China.
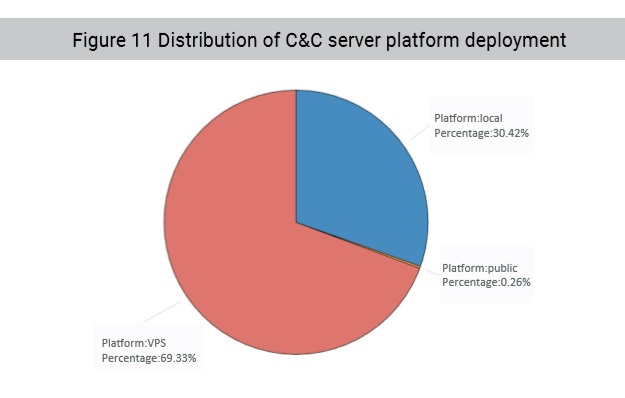
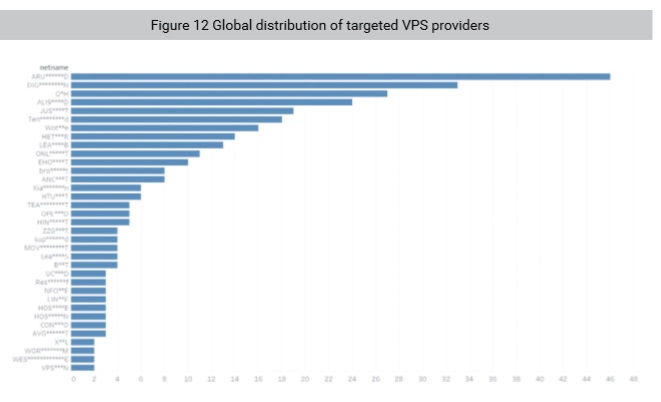
According to analysis of platforms, most C&C servers are deployed on virtual private servers (VPSs) located in private clouds.
Further analysis of VPS providers suggests that well-known providers in China and globally were especially favored by botnets.
Figure 12 Global distribution
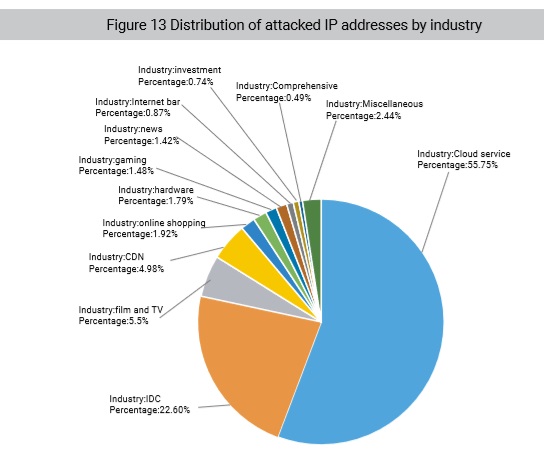
After deduplicating IP addresses, we worked out the distribution of attacked IP addresses by industry. As shown in the following figure, botnets are indiscriminate and attack almost all computer industries. Analysis of IP addresses with a clear attribution show that Internet cloud providers and traditional IDC providers received most attacks.
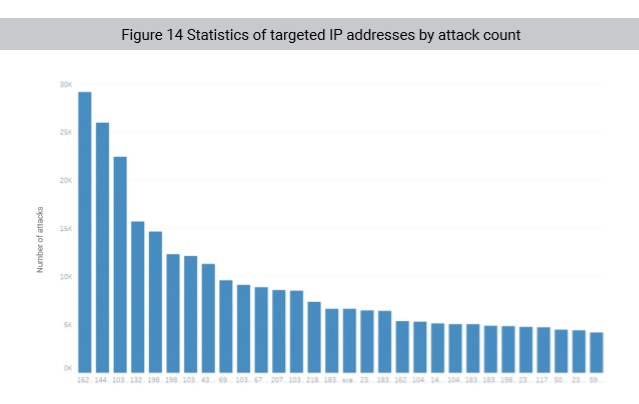
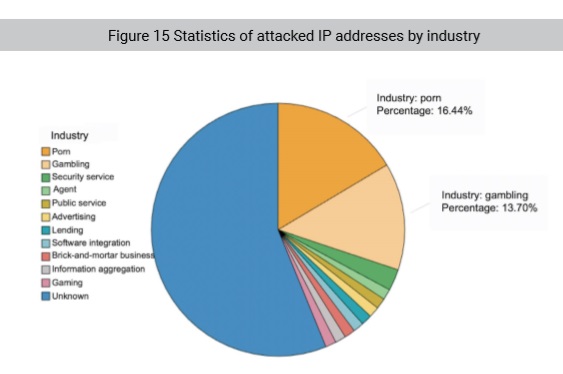
Studying targeted IPs themselves is informative if not entertaining. Statistical analysis show that gambling and porn websites were the most targeted, with the IP address, 162.218.*.142, suffering 29,161 (an average of 79 per day) DDoS attacks throughout 2018.
To be continued