3.2 Family Activity
3.2.1 Behavior Seen
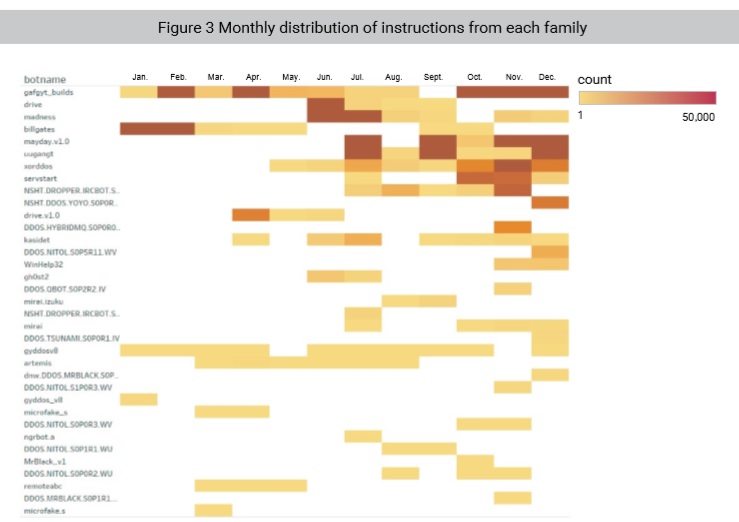
In 2018, a total of 35 active families were found to issue more than 100 botnet instructions, accounting for 24% of all known families. Several families with the highest level of instruction activity accounted for most of the malicious activities throughout 2018.
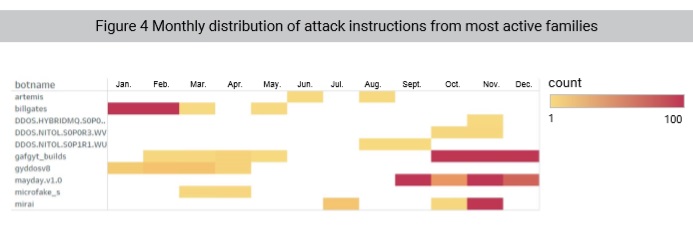
As shown in Figure 4, the most active botnet families issuing instructions were active from January to March and September to December, but became relatively lethargic in June and July, when a smaller number of instructions issued.
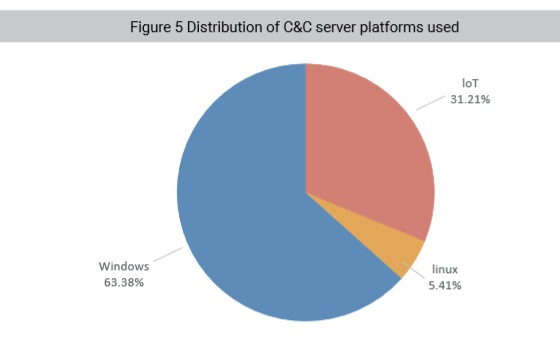
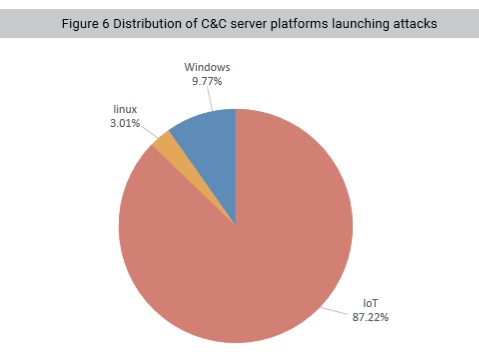
As for platforms hosting C&C servers, families using IoT platforms, though smaller in quantity, were more active, attracting 87% of attackers.
3.2.2 Analysis
IoT Devices with Poor Security Favored by Botnets
In 2018, botnets were shifting from Windows platforms towards Linux and IoT platforms, leading to the fast decline of older Windows-based families and the thriving of new IoT-based ones.
In previous years, Windows platforms were the primary target of all sorts of malware. Research shows that the longest established families, including previous closely monitored families such as Huigezi, gyddos, and Darkshell, mainly run on Windows platforms. Therefore, malicious behavior detection was based around Windows platforms at that time. In 2018, as variants from Gafgyt and Mirai families grew at an explosive rate, we shifted our detection focus to other platforms from Windows.
The shift of attack platforms is due to three factors:
1. Full upgrade of Windows platforms. According to StatCounter2 (an analysis website), before December 2018, Windows 10 had had a global share of 52.36%, overtaking Windows 7 as the most popular Windows operating system. Thanks to its forced update policy, Windows 10 significantly improves over Windows 7 security such that it can block much more malware prior to intrusion.
2. Out-of-date security of IoT platforms. While the total number of IoT devices globally surges rapidly and IoT product lines are increasingly diversified, IoT devices still have poor security. Insecure firmware and communication protocols lead to numerous vulnerabilities in IoT platforms. Meanwhile, IoT device users’ lack of security awareness is a contributing factor to IoT security issues. Currently, a great many IoT devices still use default usernames and passwords, making it possible for hackers to use a wide range of cracking tools to take control of these devices and turn them into new weapons. This is one of the reasons the state of California passed the first of its kind IoT security legislation in the USA, if not the world3.
3. Botnet market segmentation. According to rough statistics on platforms, Windows platforms usually run high-value targets or hold sensitive user information, making them the primary target of information stealing groups. Active families rely on successful banking trojans and ransomware, both of which feature a high degree of covertness. In contrast, Linux platforms run highperformance devices and families usually install multipurpose trojans on these platforms to execute a variety of malicious activity predominately cryptomining. Characterized by their ubiquitous and ease of penetration, IoT devices have also grown to be the new hotbed of DDoS attacks.
While California requires security vendors to improve their security implementations, vendors themselves need to give serious thought about how to respond to changing attack platform segmentation when implementing in-product defenses.
2ï¾ http://gs.statcounter.com/os-version-market-share/windows/desktop/worldwide
3ï¾ Companion bills SB-327 and AB-1906 in the state of California mandate all IoT devices sold in California will implement “reasonable†security features, such as forcing users to change default passwords during installation or provide a unique password on each device at manufacture.
to be continued