New Trends of APT Groups
Here are three trends that shaped APT groups in 2019:
Firstly, mobile devices became common constituents of the attack surface. In 2019, MuddyWater developed malicious files against Android platforms, heading towards mobile devices. Google’s Project Zero team revealed five exploit chains deployed in the wild to attack iOS systems and noted that these exploit chains, relying on 0-day vulnerabilities, could be easily used by APT groups to target multiple iOS versions.
Secondly, security research teams have profiled APT attacks, conducted tool analysis, and upgraded detection capabilities. Also, the code of APT attack tools were sold or made public. All of these lead APT groups to keep improving their toolsets and attack methods. Such changes are reflected in the following aspects:
- Both BITTER and MuddyWater have employed new remote access trojan (RAT).
- To build more powerful and covert Trojans to defeat detection devices, OceanLotus constantly refines Trojans’ features such as multilevel free, memory loading, code obfuscation, and cryptography.
- The toolkit disclosed by APT34 in 2019 differs from those made public earlier.
- Over three years, FIN7 has constantly updated malware delivery techniques and developed and sharpened several RAT tools for better control of targets.
Thirdly, botnets are found involved in APTs. Botnets will play a vanguard role in APT attacks as their credential stealing, lateral movement, and module delivery functions can be fully utilized in those attacks to hide activity traces, allowing hackers to achieve malicious purposes under cover of them.
Predictably, in the next few years, APT attacks will be more difficult to detect and will be often found to associate with notorious botnet families.
APT and Botnet
Lazarus Group is an APT group that began to target multiple sectors at least from 2009, including finance organizations, governments, and non-government organizations.
This organization is perfecting an attack framework dubbed Anchor.
Among components delivered by Anchor, there is one tool that is nearly the same as an attack component of TrickBot. And all captured C&C servers are those of TrickBot. Therefore, we infer that Anchor is only a child project of TrickBot and still uses its C&C servers and components.
APT33 is an APT group that began to carry out attacks at least from 2013, mainly against aviation and energy sectors. Recently, this organization was revealed to use a botnet to hit a tiny range of targets. In this round of attack, this organization used about 12 C&C servers and adopted a multilevel obfuscation technique to obscure its real behavior .
This kind of behavior is very common in activities of botnets. It is predicted that this kind of attack will become increasingly prevalent, allowing APT groups to use common threats like botnets to obscure their traces and persistently penetrate and hit their desired targets.
APT and CVE
As an attack group with high skills, APT groups are ready to try and exploit vulnerabilities that are newly revealed or not yet made known to the public. In 2019, multiple APT groups set out to design kill chains based on the WinRAR vulnerability (CVE-2018-20250). Some attempted to exploit the CVE-2019-0604 vulnerability to target the affected SharePoint versions. Besides, certain organizations tried to use vulnerabilities like CVE-2019-0797, CVE-2019-0859, CVE-2019-11510, CVE-2019-11539, and CVE-2018-
13379.
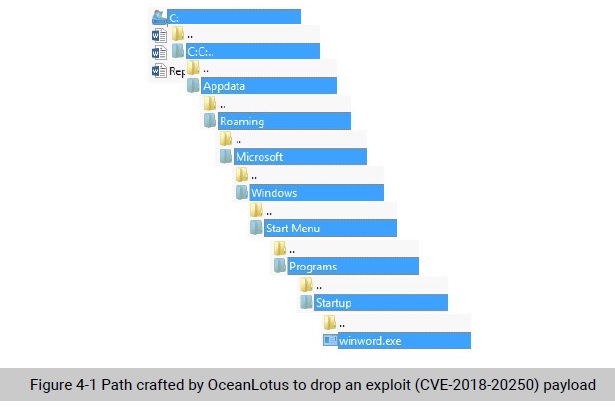
A directory traversal vulnerability (CVE-2018-20250) in the common compression software WinRAR stole the spotlight in 2019. Via a malformed relative path, the attacker instructed the vulnerable WinRAR to decompress compressed files in the ACE format to the specified absolute path. After that, the attacker implemented code execution through system file replacement. Via a compressed file, this vulnerability can be easily used together with spear phishing emails. No wonder that OceanLotus and MuddyWater among other APT groups have rapidly crafted and dropped exploit payloads based on this vulnerability to launch lightning-fast attacks against target users with incomplete email protection and software update policies.
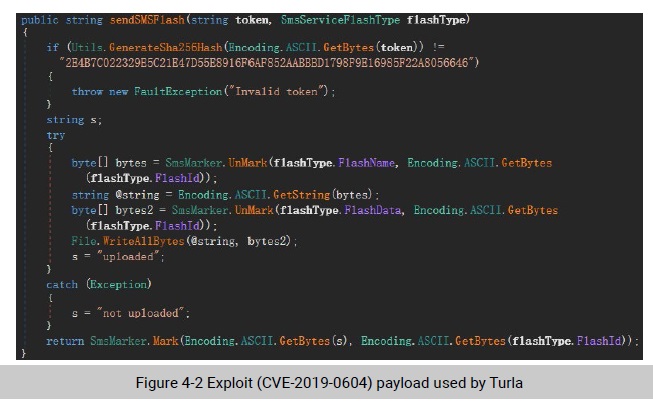
The remote code execution vulnerability (CVE-2019-0604) in Microsoft SharePoint is also a highly sought-after one. Via a specially crafted request, an attacker could exploit this vulnerability to execute arbitrary code on an affected SharePointer server. Since Microsoft disclosed this vulnerability, Turla and FIN7, among other APT groups, have crafted related tools and made attack attempts.
To be continued.
