O Distributed Denial of Service (DDoS) é um dos maiores desafios de segurança para empresas de todos os tamanhos, pois esse tipo de ataque tem como objetivo inoperar serviços vitais e aplicações importantes, afetando diretamente a fonte de receita das organizações. Com o crescimento da internet, as empresas têm tido...
Blog
ISOP – O que é e como a solução pode proteger seus ativos?
No mundo digital, a segurança dos ativos tornou-se uma preocupação primordial para empresas de todos os portes e setores. A ameaça de ataques cibernéticos, violações de dados e outras formas de comprometimento de segurança é uma realidade constante. Neste cenário, ferramentas e plataformas inovadoras são essenciais para garantir a proteção...
AI and Cybersecurity: Unveiling NSFOCUS’s Innovative Edge at HKIB Cybersecurity Solutions Day 2024
On March 15th, the Cybersecurity Solutions Day event, organized by the Hong Kong Institute of Bankers (HKIB), officially commenced. The event focused on addressing the increasingly complex cybersecurity environment influenced by AI technologies, gathering globally renowned information security vendors and experts to discuss new trends and models driven by AI...
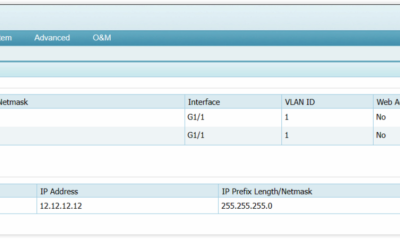
Preparation for ADS Diversion
This article summarizes the preparation configuration of ADS diversion. The specific configuration details may vary depending on the information of the ADS on the client side, router information, and ADS version. The configuration content and order can be referenced from this article. 1. Before configuring diversion, it is necessary to...
Atlassian Confluence Path Traversal Vulnerability (CVE-2024-21677) Notice
Overview Recently, NSFOCUS CERT detected that Atlassian issued a security announcement and fixed the directory traversal vulnerability in Confluence Data Center and Server (CVE-2024-21677), with a CVSS score of 8.3. Unauthenticated attackers need to interact with users, and exploiting this vulnerability can have a great impact on the confidentiality, integrity,...
Your FAQ Guide to RSA Conference 2024
Here’s your essential FAQ guide for RSA Conference 2024! Whether you’re a first-timer or a seasoned attendee, this guide aims to help you navigate the conference with ease and make the most of your experience. Welcome to stop by our booth #3301 at the South Expo of Moscone Center! Q1:...