As cloud computing, big data, Internet of Things (IoT), and mobile Internet evolve, application forms and requirements are going through changes. I believe that the application security trend virtually highlights technologies and design theories: technological innovations continue to focus on API concepts; the design theories of solutions, products, and services continue to move towards DevOps (development and operations). In this article, I will discuss the application security trend.
The fundamental thing for network is connection. Websites came into being with the advent of the Internet to serve as the bridge between natural persons and the virtual world. However, currently, websites have gone beyond web, with the rapid addition of Internet of vehicles, IoT, and mobile applications. The current informationization tide and technical advances raise more business requirements for enterprises. Unfortunately, the current number of programmers cannot satisfy the almost explosive requirements, whether due to the decrease of the labor force population or the rise of salary of employees. Therefore, making good use of the DevOps concept, breaking down inter-department communication barriers, increasing the efficiency through automation, releasing through APIs, and minimal iteration and reuse will become mainstream trends of application development in the future.
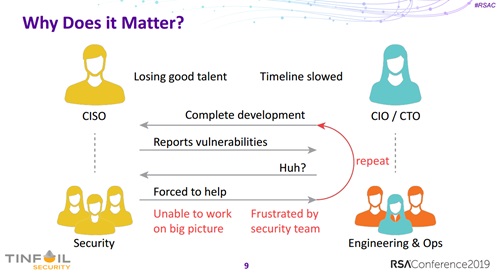
Vendors that provide application security for customers should realize another important aspect: DevOps is intended to lead the company process towards repeatability and automation. Though a good many best practices can achieve this goal currently, if DevOps is broken for security reasons, the first thing is to re-establish such a closed loop. The following is a quote of a slide page of the CEO of Tinfoil Security. We can see that different departments, if striving for inconsistent objectives, will pin down each other during cooperation instead of helping each other.
Therefore, I believe that vendors that can deliver value for customers in the future must adapt their application security products and solutions to customers’ DevOps platforms in order to integrate them to the entire R&D system.
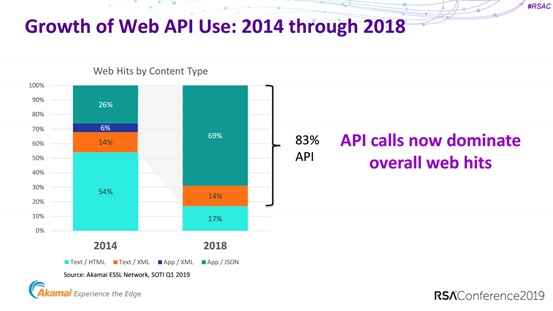
Besides, APIs also contain security issues. APIs, characterized by high cohesion and low coupling, lower the cost of communication between programmers, teams, and companies, implement rapid iteration and updates, and rebuild business. According to Akamai, among traffic of public clouds, 83% is generated by API requests; one third is contributed by web browsers and the remaining two thirds is from home TVs and smart refrigerators.
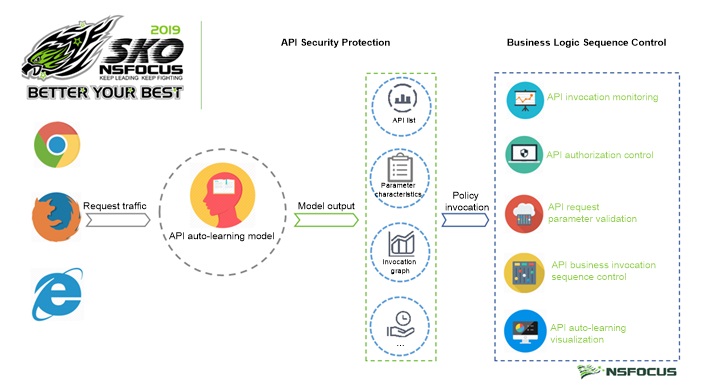
Likewise, NSFOCUS has dealt with a wide range of attacks in 2018 such as API bypass, injection, and cross-site attacks. What’s more, since the end of 2018, NSFOCUS Web Application Firewall (WAF) has successfully coped with a series of massive application-layer DDoS attacks launched with APIs. The remarkable changes in attack forms lead NSFOCUS’s R&D team to turn to API security, assessing how well current products of the new form can protect customers. On the whole, APIs are convenient but vulnerable. The reason why API-targeted attacks have become mainstream attacks is that the attack surface consisting of APIs is no less than that of websites. Meanwhile, as new APIs mean new business going live, the number of attack points of new business is inversely proportional to what weight given to security in the development phase. Besides, APIs are so easy to use that attackers can perform attack commissioning effortlessly and succeed in less time and lower cost, rendering certain API authorization mechanisms meaningless in practice. Therefore, API security protection capabilities in the future should incorporate API authorization management and invocation monitoring.
Enterprises are undergoing business transformation in an era when cloud computing, big data, IoT, and mobile Internet dominate. Keenly noticing this point, RSA presents various topics in the application security domain, almost each of which is closely related to changes to business forms. In my opinion, to achieve excellent application security assurance for win-win results, companies should concentrate their strategic objectives of related product families around DevOps and APIs.