NSFOCUS cloud scrubbing center witnessed a torrent of DDoS attack traffic, with peak volume up to 634.8 Gbps.
At 5 p.m. of May 20th, 2020, NSFOCUS SOC team detected an enormous DDoS attack – three IPs of a Hong Kong customer were hit by DDoS attacks and inbound traffic kept increasing sharply. As DDoS attack traffic constantly gushing into the scrubbing center, the peak attack traffic reached 634.8 Gbps, a new height encountered by NSFOCUS’s customers in the year of 2020. When NSFOCUS reported this event to the customer after the attack mitigation, they extended their grateful thanks to NSFOCUS and said selecting NSFOCUS Anti-DDoS solution was their best choice they made because they were well protected even when they were not aware of being targeted by DDoS attacks.
The following diagram shows the attack trend:
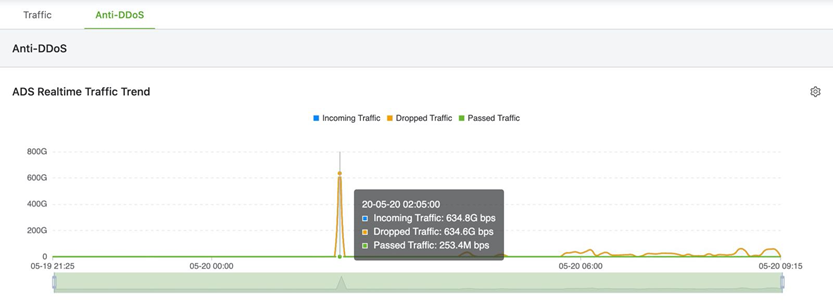
Each of the three attacked IPs, which were deployed in the same subnet, was suffered around 200 Gbps DDoS attacks on average. Protected by NSFOCUS cloud scrubbing center, only 62.1 Mpbs cleaned traffic was sent to the customer, with the scrubbing rates reached 99.99%. On average, around 20 Mbps of cleaned traffic was sent to each IP address. By comparing the cleaned traffic with traffic record in good state on the NSFOCUS SOC platform, the difference value is ±5%, which is a normal bandwidth fluctuation ratio.
According to the logs on SOC platform, the attack events are detailed in the following context:
IP: XXX.XXX.XX.XX4 Attack Peak at 216.5 Gbps, suffered 19.64 Tbits attack in this event.
IP: XXX.XXX.XX.XX1 Attack Peak at 214.1 Gbps, suffered 19.69 Tbits attack in this event.
IP: XXX.XXX.XXX.XX6 Attack Peak at 208.1 Gbps, suffered 20.0 Tbits attack in this event.
During the attack, the total attack traffic reached 59.33 Tbits, of which the peak attack value was 634.8 Gbps / 84.2 Mpps, and the clean traffic was 62.1 Mbps / 25.3 Kpps.
Attack type distribution:

The largest proportion of attack types is SYN Flood, reaching 33.82%. The total scrubbed capacity of UDP attacks is 32.04 Tbits, and the total volume of reflection attacks is 28.26 Tbits.
This kind of attacks usually comes from massive botnets, generally reaching over 200 Gbps, and it lasts from tens of minutes to an hour. Fortunately, the source port of the reflection attack has obvious characteristics and can be discarded by simple rules, so the distribution of scrubbing centers, the stability of scrubbing equipment and the pipelines are more tested rather than the algorithm. The scrubbing centers of NSFOCUS Cloud DPS are distributed in 8 cities among four continents with the sound infrastructure and the scrubbing capacity up to 7 Tbps. So, it becomes easy to complete the scrubbing mission. And on the large monitoring large screen of the NSFOCUS SOC platform, it displays the distribution of attack types, the geographic location of the source attack, the attacked situation, and the TOP ranking of various attack situations. Thus, it takes no effort to help customers operate and formulate protection strategies.
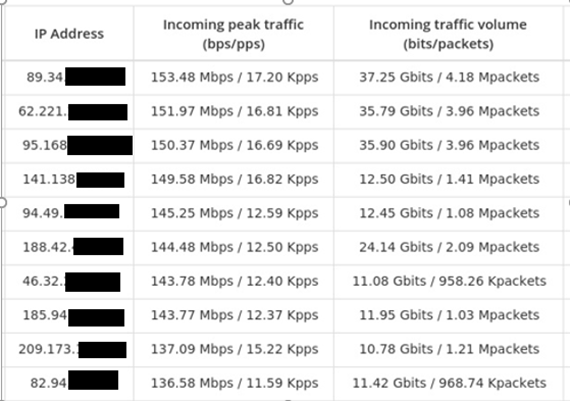
Botnets involved are mainly concentrated in the United Kingdom, the Netherlands, Luxembourg, and the United States. Each attack source has a peak value of 100 Mbps and a total of 10 Gbits to 30 Gbits.
Attackers have already begun to recruit mobile, IDC hosting servers, and IoT devices around world into massive botnet to launch attacks. Once suffering DDoS attacks, the daily loss of a corporation may reach several million dollars. Moreover, the gaming and the financial industries are becoming the “severe disaster areas” under DDoS attacks. To confront such adverse circumstance and minimize damages caused by DDoS attacks, hybrid Anti-DDoS solution is a good choice obviously.
